Last Updated on December 12, 2022 by
Cisco Netacad ITN Version 7.00 CCNA 1 v7 Final Exam Answers 2021 2022 2023 – Introduction to Networks
-
Recommend
ITN (Version 7.00 & v7.02) – ITNv7 Final Exam Answers 2021 2022 2023 Full 100%
-
A client packet is received by a server. The packet has a destination port number of 143. What service is the client requesting?
- Telnet
- SSH
- IMAP
- FTP
-
Which two functions are performed at the MAC sublayer of the OSI Data Link Layer to facilitate Ethernet communication? (Choose two.) —> Case A
-
- handles communication between upper layer networking software and Ethernet NIC hardware
- places information in the Ethernet frame that identifies which network layer protocol is being encapsulated by the frame
- implements trailer with frame check sequence for error detection
- adds Ethernet control information to network protocol data
- applies delimiting of Ethernet frame fields to synchronize communication between nodes
-
Which two functions are performed at the MAC sublayer of the OSI Data Link Layer to facilitate Ethernet communication? (Choose two.) —> Case B
- adds Ethernet control information to network protocol data
- integrates Layer 2 flows between 10 Gigabit Ethernet over fiber and 1 Gigabit Ethernet over copper
- handles communication between upper layer networking software and Ethernet NIC hardware
- implements CSMA/CD over legacy shared half-duplex media
- enables IPv4 and IPv6 to utilize the same physical medium
-
Which two functions are performed at the MAC sublayer of the OSI Data Link Layer to facilitate Ethernet communication? (Choose two.) —> Case C
- implements trailer with frame check sequence for error detection
- handles communication between upper layer networking software and Ethernet NIC hardware
- adds Ethernet control information to network protocol data
- places information in the Ethernet frame that identifies which network layer protocol is being encapsulated by the frame
- implements a process to delimit fields within an Ethernet 2 frame
-
-
A new network administrator has been asked to enter a banner message on a Cisco device. What is the fastest way a network administrator could test whether the banner is properly configured?
- Enter CTRL-Z at the privileged mode prompt.
- Power cycle the device.
- Exit privileged EXEC mode and press Enter.
- Exit global configuration mode.
- Reboot the device.
Answers Explanation & Hints:
While at the privileged mode prompt such as Router#, type exit ,press Enter , and the banner message appears. Power cycling a network device that has had the banner motd command issued will also display the banner message, but this is not a quick way to test the configuration.
-
What happens when the transport input ssh command is entered on the switch vty lines?
- The switch requires a username/password combination for remote access.
- The SSH client on the switch is enabled.
- Communication between the switch and remote users is encrypted.
- The switch requires remote connections via a proprietary client software.
Answers Explanation & Hints:
The transport input ssh command when entered on the switch vty (virtual terminal lines) will encrypt all inbound controlled telnet connections.
-
What is the subnet ID associated with the IPv6 address 2001:DA48:FC5:A4:3D1B::1/64?
- 2001:DA48::/64
- 2001::/64
- 2001:DA48:FC5:A4::/64
- 2001:DA48:FC5::A4:/64
Explanation:
-
A client is using SLAAC to obtain an IPv6 address for its interface. After an address has been generated and applied to the interface, what must the client do before it can begin to use this IPv6 address?
- It must send an ICMPv6 Router Solicitation message to determine what default gateway it should use.
- It must send a DHCPv6 INFORMATION-REQUEST message to request the address of the DNS server.
- It must send a DHCPv6 REQUEST message to the DHCPv6 server to request permission to use this address.
- It must send an ICMPv6 Neighbor Solicitation message to ensure that the address is not already in use on the network.
Explanation:
Stateless DHCPv6 or stateful DHCPv6 uses a DHCP server, but Stateless Address Autoconfiguration (SLAAC) does not. A SLAAC client can automatically generate an address that is based on information from local routers via Router Advertisement (RA) messages. Once an address has been assigned to an interface via SLAAC, the client must ensure via Duplicate Address Detection (DAD) that the address is not already in use. It does this by sending out an ICMPv6 Neighbor Solicitation message and listening for a response. If a response is received, then it means that another device is already using this address.
-
Which range of link-local addresses can be assigned to an IPv6-enabled interface?
- FE80::/10
- FDEE::/7
- FF00::/8
- FEC0::/10
Explanation:
Link-local addresses are in the range of FE80::/10 to FEBF::/10. The original IPv6 specification defined site-local addresses and used the prefix range FEC0::/10, but these addresses were deprecated by the IETF in favor of unique local addresses. FDEE::/7 is a unique local address because it is in the range of FC00::/7 to FDFF::/7. IPv6 multicast addresses have the prefix FF00::/8.
-
What mechanism is used by a router to prevent a received IPv4 packet from traveling endlessly on a network?
- It checks the value of the TTL field and if it is 100, it discards the packet and sends a Destination Unreachable message to the source host.
- It increments the value of the TTL field by 1 and if the result is 100, it discards the packet and sends a Parameter Problem message to the source host.
- It checks the value of the TTL field and if it is 0, it discards the packet and sends a Destination Unreachable message to the source host.
- It decrements the value of the TTL field by 1 and if the result is 0, it discards the packet and sends a Time Exceeded message to the source host.
-
A network administrator is designing the layout of a new wireless network. Which three areas of concern should be accounted for when building a wireless network? (Choose three.)
- mobility options
- security
- interference
- coverage area
- packet collision
- extensive cabling
Explanation:
The three areas of concern for wireless networks focus on the size of the coverage area, any nearby interference, and providing network security. Extensive cabling is not a concern for wireless networks, as a wireless network will require minimal cabling for providing wireless access to hosts. Mobility options are not a component of the areas of concern for wireless networks.
-
Refer to the exhibit. What is wrong with the displayed termination?
CCNA1 v7 – ITNv7 – Final Exam Answers 07 - The untwisted length of each wire is too long.
- The woven copper braid should not have been removed.
- The wrong type of connector is being used.
- The wires are too thick for the connector that is used.
Answers Explanation & Hints:
When a cable to an RJ-45 connector is terminated, it is important to ensure that the untwisted wires are not too long and that the flexible plastic sheath surrounding the wires is crimped down and not the bare wires. None of the colored wires should be visible from the bottom of the jack.
-
A network administrator notices that some newly installed Ethernet cabling is carrying corrupt and distorted data signals. The new cabling was installed in the ceiling close to fluorescent lights and electrical equipment. Which two factors may interfere with the copper cabling and result in signal distortion and data corruption? (Choose two.)
- EMI
- signal attenuation
- crosstalk
- RFI
- extended length of cabling
Explanation:
EMI and RFI signals can distort and corrupt data signals that are carried by copper media. These distortions usually come from radio waves and electromagnetic devices such as motors and florescent lights. Crosstalk is a disturbance that is caused by adjacent wires bundled too close together with the magnetic field of one wire affecting another. Signal attenuation is caused when an electrical signal begins to deteriorate over the length of a copper cable.
-
Data is being sent from a source PC to a destination server. Which three statements correctly describe the function of TCP or UDP in this situation? (Choose three.)
- TCP is the preferred protocol when a function requires lower network overhead.
- The source port field identifies the running application or service that will handle data returning to the PC.
- The TCP source port number identifies the sending host on the network.
- UDP segments are encapsulated within IP packets for transport across the network.
- The UDP destination port number identifies the application or service on the server which will handle the data.
- The TCP process running on the PC randomly selects the destination port when establishing a session with the server.
Explanation:
Layer 4 port numbers identify the application or service which will handle the data. The source port number is added by the sending device and will be the destination port number when the requested information is returned. Layer 4 segments are encapsulated within IP packets. UDP, not TCP, is used when low overhead is needed. A source IP address, not a TCP source port number, identifies the sending host on the network. Destination port numbers are specific ports that a server application or service monitors for requests.
-
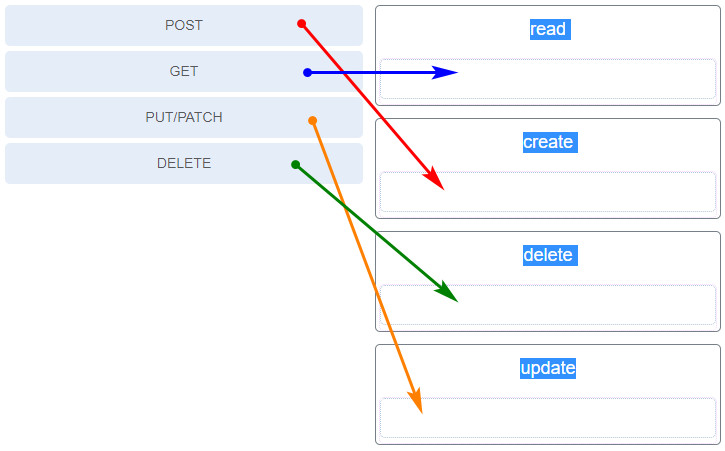
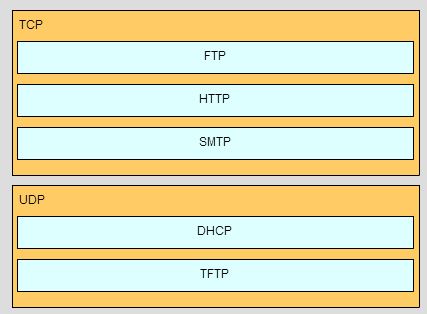
Match the application protocols to the correct transport protocols.
CCNA1 v7 – ITNv7 – Final Exam Answers 01 -
A group of Windows PCs in a new subnet has been added to an Ethernet network. When testing the connectivity, a technician finds that these PCs can access local network resources but not the Internet resources. To troubleshoot the problem, the technician wants to initially confirm the IP address and DNS configurations on the PCs, and also verify connectivity to the local router. Which three Windows CLI commands and utilities will provide the necessary information? (Choose three.)
- netsh interface ipv6 show neighbor
- arp -a
- tracert
- ping
- ipconfig
- nslookup
- telnet
Explanation:
The ipconfig and nslookup commands will provide initial IP address and DNS configuration information to the technicians and determine if DHCP is assigning correct information to the PCs. The ping utility would be used to verify, or not, connectivity to the default gateway (router) using the configured default gateway address, or using the known correct default gateway address if these are found to be different. The arp -a or netsh interface ipv6 show neighbor commands could be used if the problem is then suspected to be an IP address to MAC address mapping issue. The telnet and tracert utilities could be used to determine where the problem was located in the network if the default gateway configuration was found to be correct.
-
What two pieces of information are displayed in the output of the show ip interface brief command? (Choose two.)
- speed and duplex settings
- MAC addresses
- next-hop addresses
- interface descriptions
- IP addresses
- Layer 1 statuses
Explanation:
The command show ip interface brief shows the IP address of each interface, as well as the operational status of the interfaces at both Layer 1 and Layer 2. In order to see interface descriptions and speed and duplex settings, use the command show running-config interface. Next-hop addresses are displayed in the routing table with the command show ip route, and the MAC address of an interface can be seen with the command show interfaces.
-
A network administrator is adding a new LAN to a branch office. The new LAN must support 25 connected devices. What is the smallest network mask that the network administrator can use for the new network?
- 255.255.255.224
- 255.255.255.192
- 255.255.255.240
- 255.255.255.128
-
Which frame field is created by a source node and used by a destination node to ensure that a transmitted data signal has not been altered by interference, distortion, or signal loss?
- transport layer error check field
- error correction process field
- flow control field
- User Datagram Protocol field
- frame check sequence field
-
What is a function of the data link layer?
- provides delivery of data between two applications
- provides for the exchange of frames over a common local media
- provides end-to-end delivery of data between hosts
- provides the formatting of data
-
What are three characteristics of the CSMA/CD process? (Choose three.)
- After detecting a collision, hosts can attempt to resume transmission after a random time delay has expired.
- A jam signal indicates that the collision has cleared and the media is not busy.
- All of the devices on a segment see data that passes on the network medium.
- The device with the electronic token is the only one that can transmit after a collision.
- Devices can be configured with a higher transmission priority.
- A device listens and waits until the media is not busy before transmitting.
-
What characteristic describes a Trojan horse?
- an attack that slows or crashes a device or network service
- malicious software or code running on an end device
- a network device that filters access and traffic coming into a network
- the use of stolen credentials to access private data
-
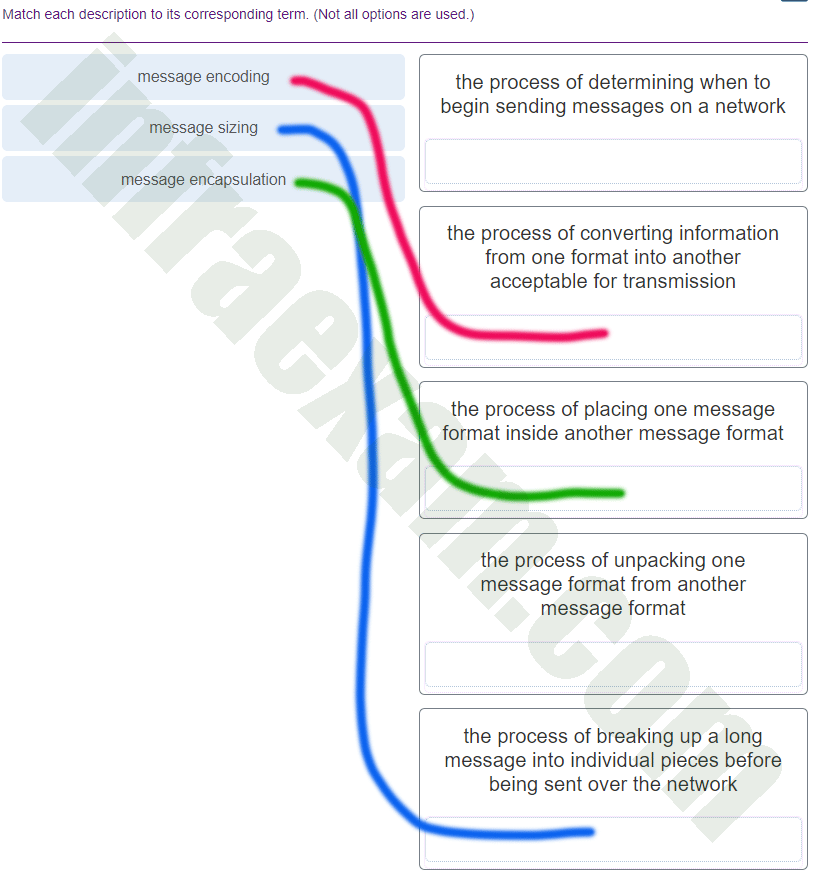
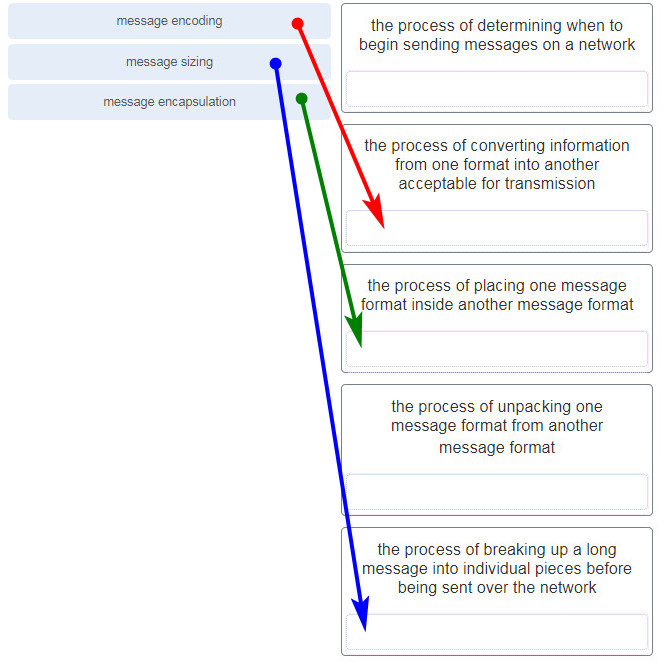
What three requirements are defined by the protocols used in network communcations to allow message transmission across a network? (Choose three.)
- end-device installation
- media selection
- message encoding
- delivery options
- connector specifications
- message size
-
What are two features of ARP? (Choose two.)
- If a device receiving an ARP request has the destination IPv4 address, it responds with an ARP reply.
- When a host is encapsulating a packet into a frame, it refers to the MAC address table to determine the mapping of IP addresses to MAC addresses.
- If no device responds to the ARP request, then the originating node will broadcast the data packet to all devices on the network segment.
- An ARP request is sent to all devices on the Ethernet LAN and contains the IP address of the destination host and its multicast MAC address.
- If a host is ready to send a packet to a local destination device and it has the IP address but not the MAC address of the destination, it generates an ARP broadcast.
Explanation:
When a node encapsulates a data packet into a frame, it needs the destination MAC address. First it determines if the destination device is on the local network or on a remote network. Then it checks the ARP table (not the MAC table) to see if a pair of IP address and MAC address exists for either the destination IP address (if the destination host is on the local network) or the default gateway IP address (if the destination host is on a remote network). If the match does not exist, it generates an ARP broadcast to seek the IP address to MAC address resolution. Because the destination MAC address is unknown, the ARP request is broadcast with the MAC address FFFF.FFFF.FFFF. Either the destination device or the default gateway will respond with its MAC address, which enables the sending node to assemble the frame. If no device responds to the ARP request, then the originating node will discard the packet because a frame cannot be created.
-
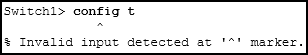
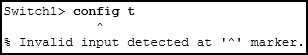
Refer to the exhibit. An administrator is trying to configure the switch but receives the error message that is displayed in the exhibit. What is the problem?
CCNA1 v7 – ITNv7 – Final Exam Answers 06 - The entire command, configure terminal , must be used.
- The administrator must connect via the console port to access global configuration mode.
- The administrator is already in global configuration mode.
- The administrator must first enter privileged EXEC mode before issuing the command.
Answers Explanation & Hints:
In order to enter global configuration mode, the command configure terminal , or a shortened version such as config t , must be entered from privileged EXEC mode. In this scenario the administrator is in user EXEC mode, as indicated by the > symbol after the hostname. The administrator would need to use the enable command to move into privileged EXEC mode before entering the configure terminal command.
-
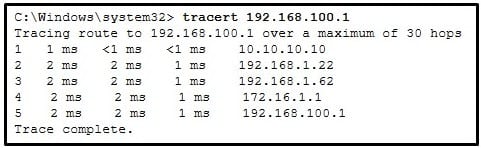
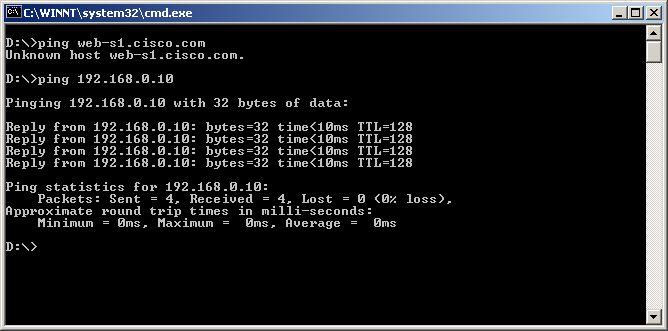
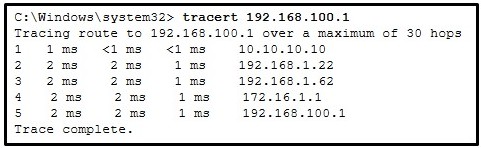
Refer to the exhibit. On the basis of the output, which two statements about network connectivity are correct? (Choose two.)
CCNA1 v7 – ITNv7 – Final Exam Answers 05 - This host does not have a default gateway configured.
- There are 4 hops between this device and the device at 192.168.100.1.
- The average transmission time between the two hosts is 2 milliseconds.
- There is connectivity between this device and the device at 192.168.100.1.
- The connectivity between these two hosts allows for videoconferencing calls.
Explanation:
The output displays a successful Layer 3 connection between a host computer and a host at 19.168.100.1. It can be determined that 4 hops exist between them and the average transmission time is 1 milliseconds. Layer 3 connectivity does not necessarily mean that an application can run between the hosts.
-
What are two characteristics of IP? (Choose two.)
- retransmits packets if errors occur
- guarantees delivery of packets
- does not require a dedicated end-to-end connection
- operates independently of the network media
- re-assembles out of order packets into the correct order at the receiver end
Explanation:
The Internet Protocol (IP) is a connectionless, best effort protocol. This means that IP requires no end-to-end connection nor does it guarantee delivery of packets. IP is also media independent, which means it operates independently of the network media carrying the packets.
-
What will happen if the default gateway address is incorrectly configured on a host?
- The host cannot communicate with hosts in other networks.
- The host cannot communicate with other hosts in the local network.
- A ping from the host to 127.0.0.1 would not be successful.
- The switch will not forward packets initiated by the host.
- The host will have to use ARP to determine the correct address of the default gateway.
Answers Explanation & Hints:
When a host needs to send a message to another host located on the same network, it can forward the message directly. However, when a host needs to send a message to a remote network, it must use the router, also known as the default gateway. This is because the data link frame address of the remote destination host cannot be used directly. Instead, the IP packet has to be sent to the router (default gateway) and the router will forward the packet toward its destination. Therefore, if the default gateway is incorrectly configured, the host can communicate with other hosts on the same network, but not with hosts on remote networks.
-
Users report that the network access is slow. After questioning the employees, the network administrator learned that one employee downloaded a third-party scanning program for the printer. What type of malware might be introduced that causes slow performance of the network?
- spam
- virus
- worm
- phishing
Explanation:
-
A company has a file server that shares a folder named Public. The network security policy specifies that the Public folder is assigned Read-Only rights to anyone who can log into the server while the Edit rights are assigned only to the network admin group. Which component is addressed in the AAA network service framework?
- automation
- authorization
- accounting
- authentication
Explanation:
After a user is successfully authenticated (logged into the server), the authorization is the process of determining what network resources the user can access and what operations (such as read or edit) the user can perform.
-
What are two common causes of signal degradation when using UTP cabling? (Choose two.)
- loss of light over long distances
- low-quality cable or connectors
- low-quality shielding in cable
- installing cables in conduit
- improper termination
-
Which scenario describes a function provided by the transport layer?
- A student has two web browser windows open in order to access two web sites. The transport layer ensures the correct web page is delivered to the correct browser window.
- A student is using a classroom VoIP phone to call home. The unique identifier burned into the phone is a transport layer address used to contact another network device on the same network.
- A corporate worker is accessing a web server located on a corporate network. The transport layer formats the screen so the web page appears properly no matter what device is being used to view the web site.
- A student is playing a short web-based movie with sound. The movie and sound are encoded within the transport layer header.
Explanation:
The source and destination port numbers are used to identify the correct application and window within that application.
-
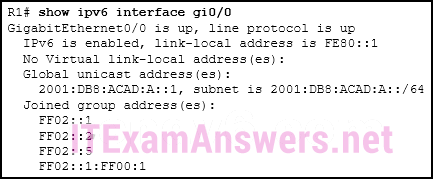
What is the consequence of configuring a router with the ipv6 unicast-routing global configuration command?
- Each router interface will generate an IPv6 link-local address.
- The IPv6 enabled router interfaces begin sending ICMPv6 Router Advertisement messages.
- It statically creates a global unicast address on this router.
- All router interfaces will be automatically activated.
-
Which two protocols operate at the top layer of the TCP/IP protocol suite? (Choose two.)
- POP
- DNS
- IP
- TCP
- Ethernet
- UDP
-
An employee of a large corporation remotely logs into the company using the appropriate username and password. The employee is attending an important video conference with a customer concerning a large sale. It is important for the video quality to be excellent during the meeting. The employee is unaware that after a successful login, the connection to the company ISP failed. The secondary connection, however, activated within seconds. The disruption was not noticed by the employee or other employees.
What three network characteristics are described in this scenario? (Choose three.)- integrity
- scalability
- quality of service
- fault tolerance
- powerline networking
- security
-
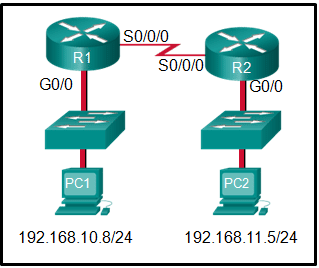
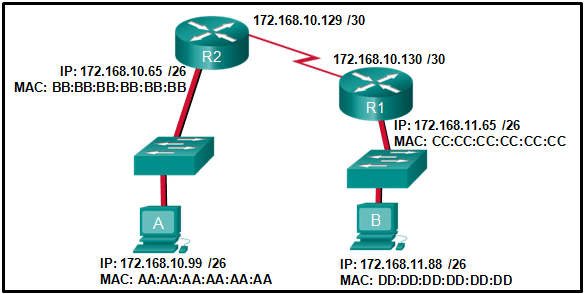
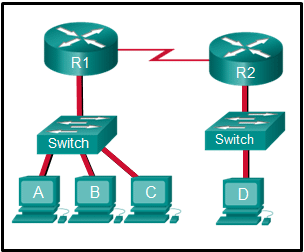
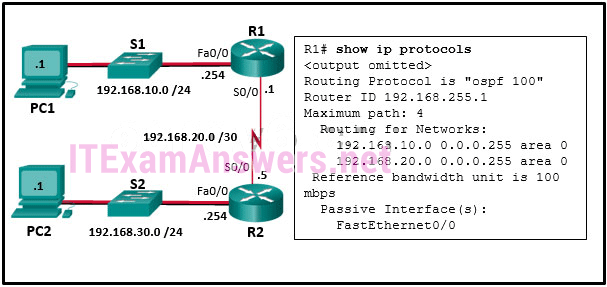
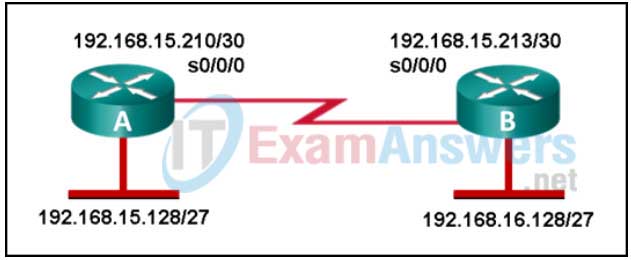
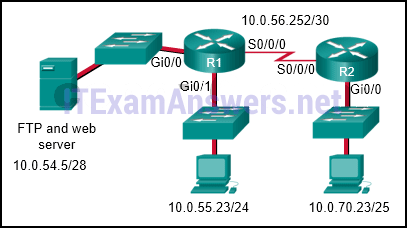
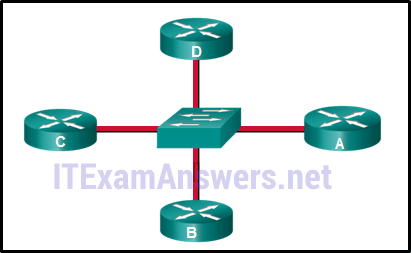
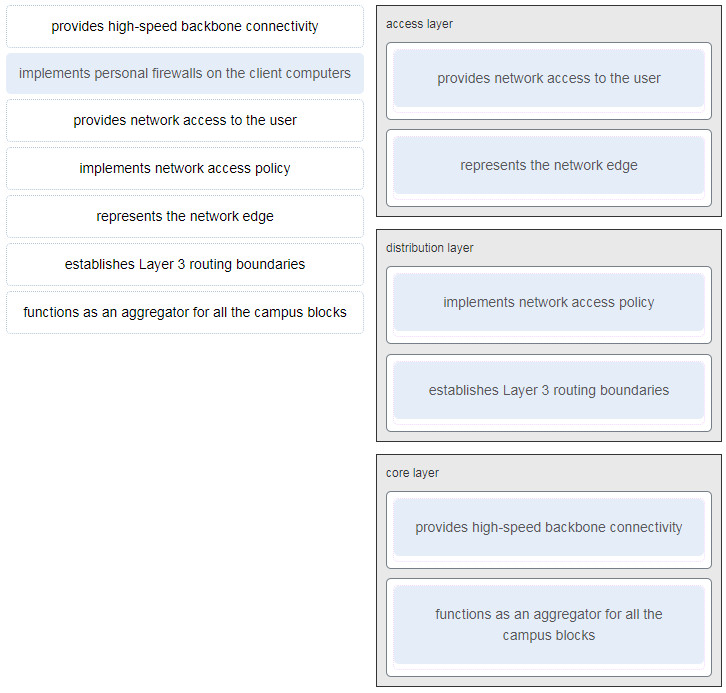
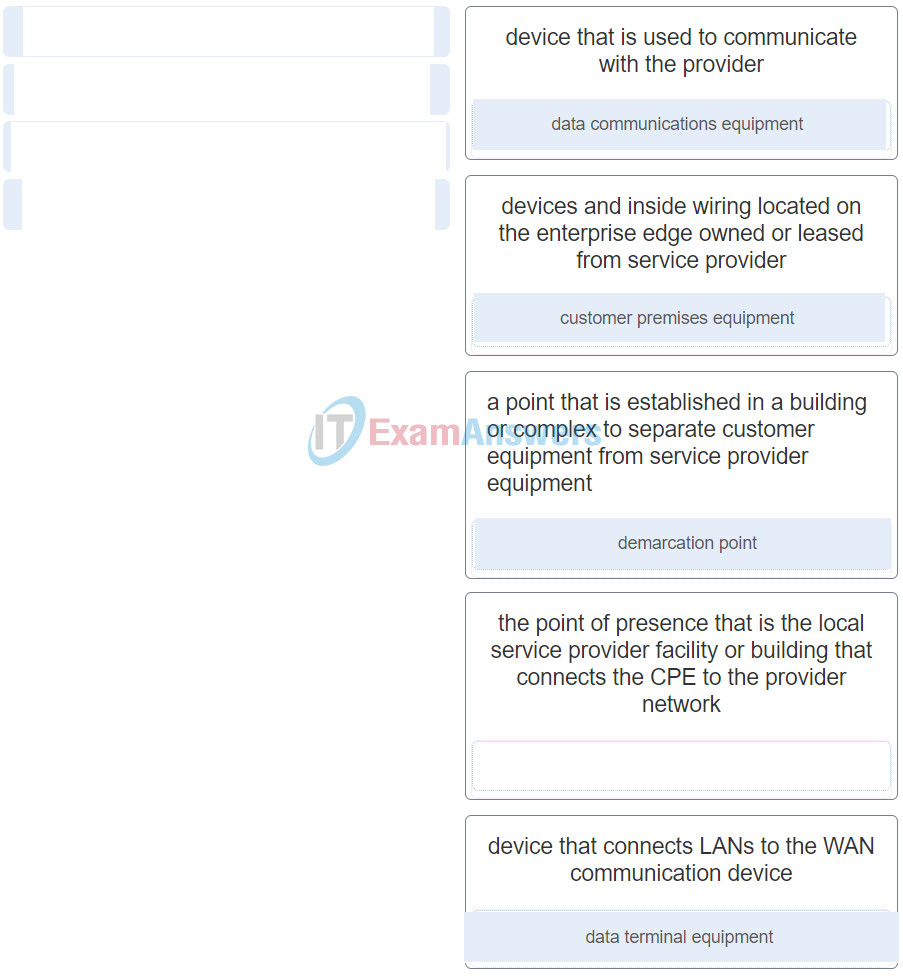
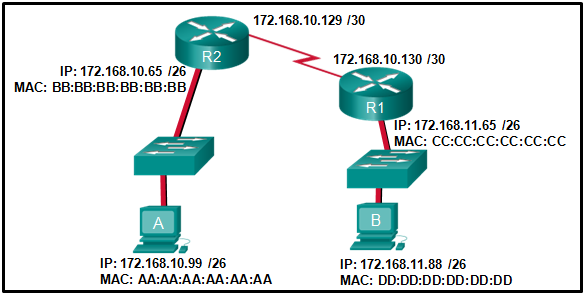
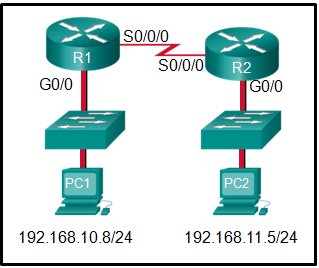
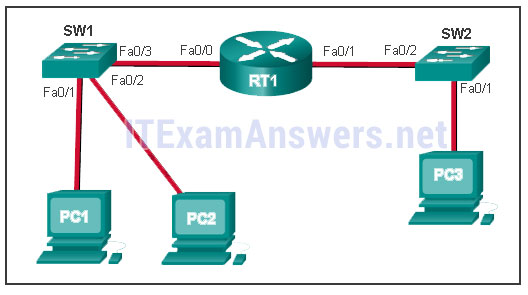
Refer to the exhibit. If PC1 is sending a packet to PC2 and routing has been configured between the two routers, what will R1 do with the Ethernet frame header attached by PC1?
CCNA1 v7 – ITNv7 – Final Exam Answers 04 - open the header and use it to determine whether the data is to be sent out S0/0/0
- open the header and replace the destination MAC address with a new one
- nothing, because the router has a route to the destination network
- remove the Ethernet header and configure a new Layer 2 header before sending it out S0/0/0
Explanation:
When PC1 forms the various headers attached to the data one of those headers is the Layer 2 header. Because PC1 connects to an Ethernet network, an Ethernet header is used. The source MAC address will be the MAC address of PC1 and the destination MAC address will be that of G0/0 on R1. When R1 gets that information, the router removes the Layer 2 header and creates a new one for the type of network the data will be placed onto (the serial link).
-
Which three layers of the OSI model map to the application layer of the TCP/IP model? (Choose three.)
- transport
- application
- network
- session
- data link
- presentation
Explanation:
-
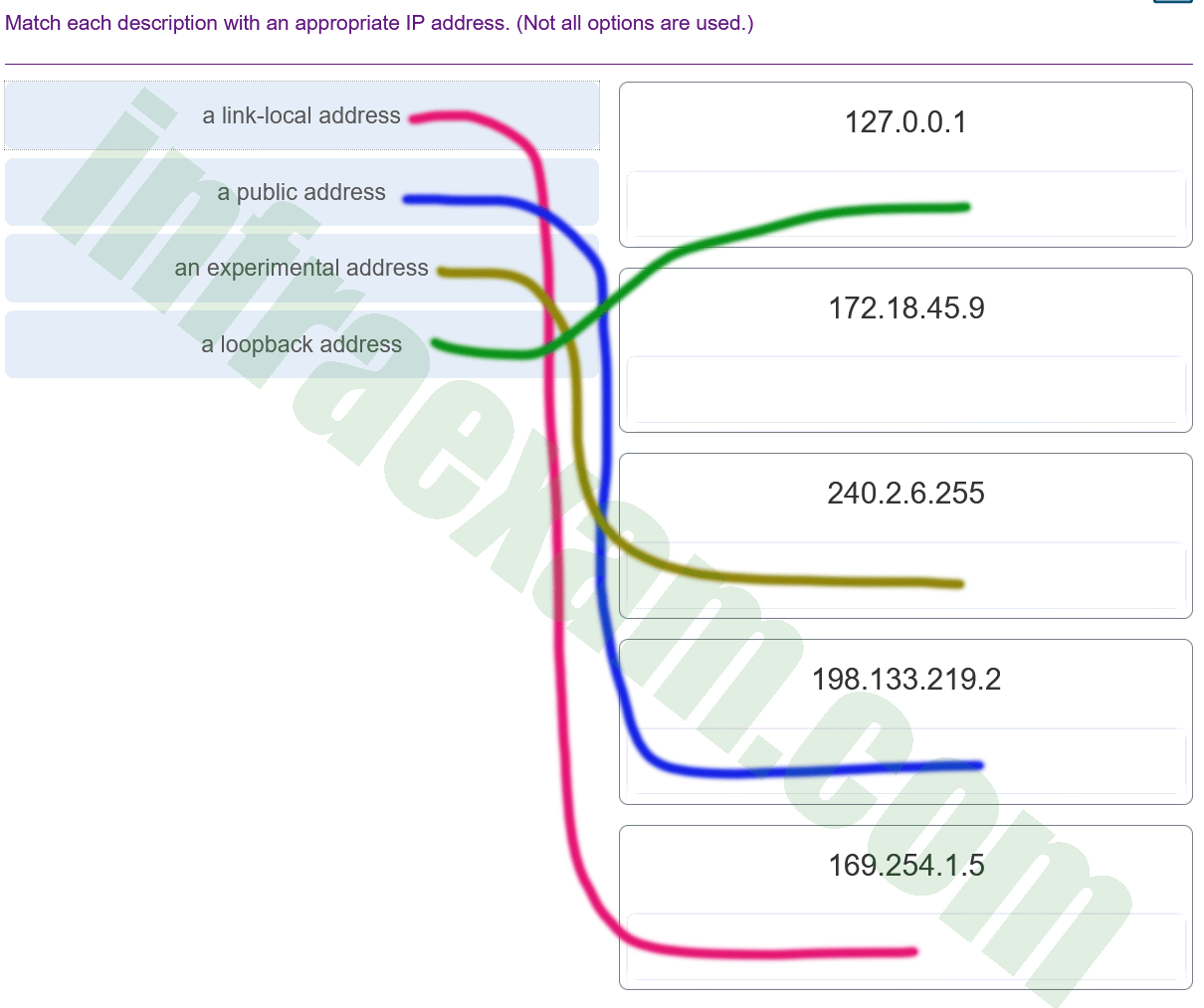
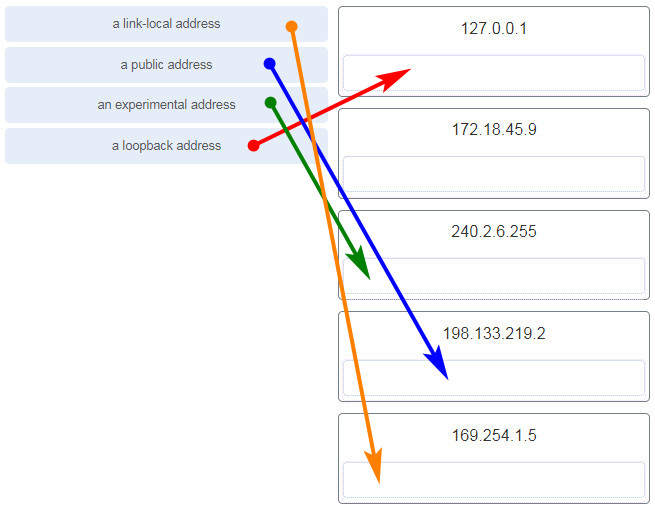
Match each description with an appropriate IP address. (Not all options are used.)
CCNA1 v7 – ITNv7 – Final Exam Answers 02 Explanation:
Link-Local addresses are assigned automatically by the OS environment and are located in the block 169.254.0.0/16. The private addresses ranges are 10.0.0.0/8, 172.16.0.0/12, and 192.168.0.0/16. TEST-NET addresses belong to the range 192.0.2.0/24. The addresses in the block 240.0.0.0 to 255.255.255.254 are reserved as experimental addresses. Loopback addresses belong to the block 127.0.0.0/8.
-
What does the term “attenuation” mean in data communication?
- strengthening of a signal by a networking device
- leakage of signals from one cable pair to another
- loss of signal strength as distance increases
- time for a signal to reach its destination
Answers Explanation & Hints:
Data is transmitted on copper cables as electrical pulses. A detector in the network interface of a destination device must receive a signal that can be successfully decoded to match the signal sent. However, the farther the signal travels, the more it deteriorates. This is referred to as signal attenuation.
-
Which two statements describe how to assess traffic flow patterns and network traffic types using a protocol analyzer? (Choose two.)
- Capture traffic during peak utilization times to get a good representation of the different traffic types.
- Perform the capture on different network segments.
- Only capture WAN traffic because traffic to the web is responsible for the largest amount of traffic on a network.
- Only capture traffic in the areas of the network that receive most of the traffic such as the data center.
- Capture traffic on the weekends when most employees are off work.
Explanation:
Traffic flow patterns should be gathered during peak utilization times to get a good representation of the different traffic types. The capture should also be performed on different network segments because some traffic will be local to a particular segment.
-
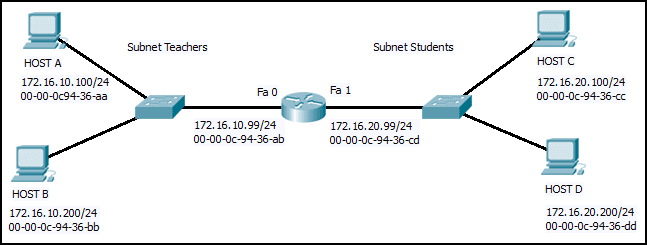
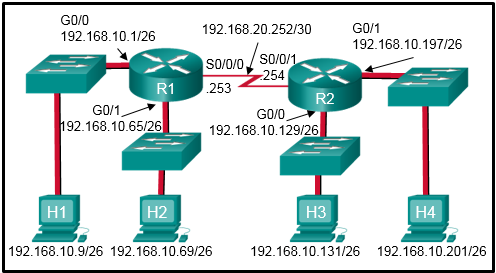
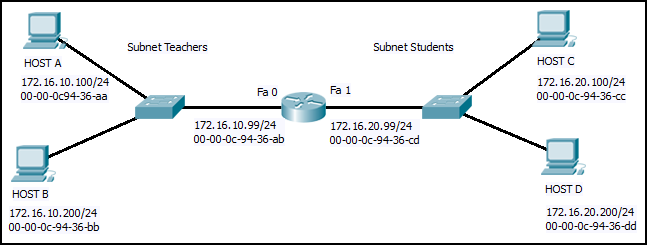
Refer to the exhibit. Host B on subnet Teachers transmits a packet to host D on subnet Students. Which Layer 2 and Layer 3 addresses are contained in the PDUs that are transmitted from host B to the router?
CCNA1 v7 – ITNv7 – Final Exam Answers 03 - Layer 2 destination address = 00-00-0c-94-36-dd
Layer 2 source address = 00-00-0c-94-36-bb
Layer 3 destination address = 172.16.20.200
Layer 3 source address = 172.16.10.200 - Layer 2 destination address = 00-00-0c-94-36-ab
Layer 2 source address = 00-00-0c-94-36-bb
Layer 3 destination address = 172.16.20.200
Layer 3 source address = 172.16.100.200 - Layer 2 destination address = 00-00-0c-94-36-ab
Layer 2 source address = 00-00-0c-94-36-bb
Layer 3 destination address = 172.16.20.200
Layer 3 source address = 172.16.10.200 - Layer 2 destination address = 00-00-0c-94-36-cd
Layer 2 source address = 00-00-0c-94-36-bb
Layer 3 destination address = 172.16.20.99
Layer 3 source address = 172.16.10.200
- Layer 2 destination address = 00-00-0c-94-36-dd
-
Which subnet would include the address 192.168.1.96 as a usable host address?
- 192.168.1.32/27
- 192.168.1.32/28
- 192.168.1.64/29
- 192.168.1.64/26
Explanation:
For the subnet of 192.168.1.64/26, there are 6 bits for host addresses, yielding 64 possible addresses. However, the first and last subnets are the network and broadcast addresses for this subnet. Therefore, the range of host addresses for this subnet is 192.168.1.65 to 192.168.1.126. The other subnets do not contain the address 192.168.1.96 as a valid host address.
-
What are two problems that can be caused by a large number of ARP request and reply messages? (Choose two.)
- A large number of ARP request and reply messages may slow down the switching process, leading the switch to make many changes in its MAC table.
- The ARP request is sent as a broadcast, and will flood the entire subnet.
- Switches become overloaded because they concentrate all the traffic from the attached subnets.
- All ARP request messages must be processed by all nodes on the local network.
- The network may become overloaded because ARP reply messages have a very large payload due to the 48-bit MAC address and 32-bit IP address that they contain.
-
Why would a Layer 2 switch need an IP address?
- to enable the switch to be managed remotely
- to enable the switch to receive frames from attached PCs
- to enable the switch to send broadcast frames to attached PCs
- to enable the switch to function as a default gateway
Answers Explanation & Hints:
A switch, as a Layer 2 device, does not need an IP address to transmit frames to attached devices. However, when a switch is accessed remotely through the network, it must have a Layer 3 address. The IP address must be applied to a virtual interface rather than to a physical interface. Routers, not switches, function as default gateways.
-
How does the service password-encryption command enhance password security on Cisco routers and switches?
- It requires encrypted passwords to be used when connecting remotely to a router or switch with Telnet.
- It encrypts passwords that are stored in router or switch configuration files.
- It requires that a user type encrypted passwords to gain console access to a router or switch.
- It encrypts passwords as they are sent across the network.
Explanation:
The service password-encryption command encrypts plaintext passwords in the configuration file so that they cannot be viewed by unauthorized users.
-
Which two statements are correct in a comparison of IPv4 and IPv6 packet headers? (Choose two.)
- The Destination Address field is new in IPv6.
- The Source Address field name from IPv4 is kept in IPv6.
- The Version field from IPv4 is not kept in IPv6.
- The Time-to-Live field from IPv4 has been replaced by the Hop Limit field in IPv6.
- The Header Checksum field name from IPv4 is kept in IPv6.
-
Which two statements accurately describe an advantage or a disadvantage when deploying NAT for IPv4 in a network? (Choose two.)
- NAT will impact negatively on switch performance.
- NAT causes routing tables to include more information.
- NAT improves packet handling.
- NAT adds authentication capability to IPv4.
- NAT provides a solution to slow down the IPv4 address depletion.
- NAT introduces problems for some applications that require end-to-end connectivity.
-
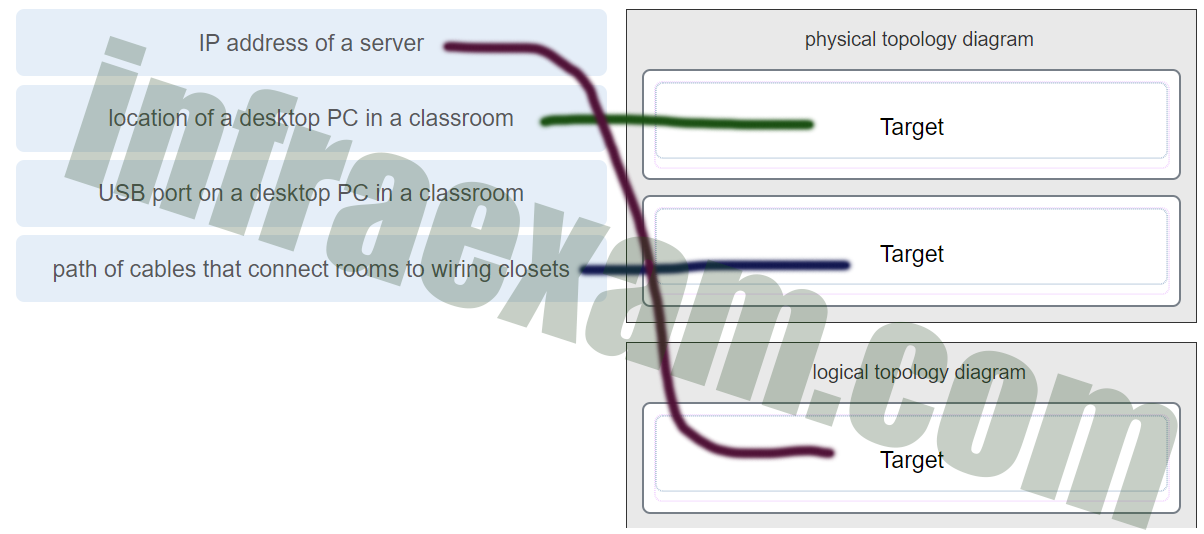
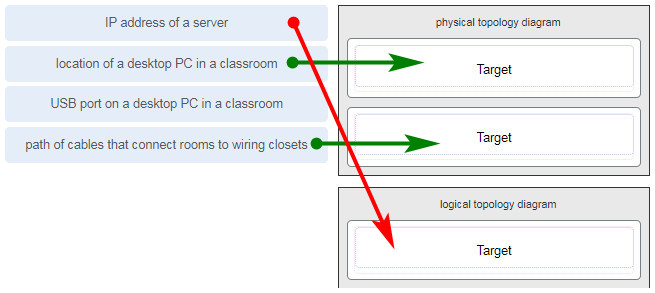
Match each item to the type of topology diagram on which it is typically identified. (Not all options are used.)
CCNA1 v7 Final Exam Answers 003 Explanation:
A logical topology diagram typically depicts the IP addressing scheme and groupings of devices and ports. A physical topology diagram shows how those devices are connected to each other and the network, focusing on the physical locations of intermediary devices, configured ports, and cabling.
-
What service is provided by HTTP?
- An application that allows real-time chatting among remote users.
- Uses encryption to secure the exchange of text, graphic images, sound, and video on the web.
- Allows for data transfers between a client and a file server.
- A basic set of rules for exchanging text, graphic images, sound, video, and other multimedia files on the web.
-
A client packet is received by a server. The packet has a destination port number of 67. What service is the client requesting?
- Telnet
- FTP
- SSH
- DHCP
-
What are the two most effective ways to defend against malware? (Choose two.)
- Implement strong passwords.
- Update the operating system and other application software.
- Install and update antivirus software.
- Implement RAID.
- Implement a VPN.
- Implement network firewalls.
Explanation:
-
An administrator defined a local user account with a secret password on router R1 for use with SSH. Which three additional steps are required to configure R1 to accept only encrypted SSH connections? (Choose three.)
- Configure the IP domain name on the router.
- Enable inbound vty Telnet sessions.
- Configure DNS on the router.
- Generate the SSH keys.
- Generate two-way pre-shared keys.
- Enable inbound vty SSH sessions.
Explanation:
There are four steps to configure SSH support on a Cisco router:
Step 1: Set the domain name.
Step 2: Generate one-way secret keys.
Step 3: Create a local username and password.
Step 4: Enable SSH inbound on a vty line.
-
A host is trying to send a packet to a device on a remote LAN segment, but there are currently no mappings in its ARP cache. How will the device obtain a destination MAC address?
- It will send the frame and use its own MAC address as the destination.
- It will send the frame with a broadcast MAC address.
- It will send an ARP request for the MAC address of the destination device.
- It will send a request to the DNS server for the destination MAC address.
- It will send an ARP request for the MAC address of the default gateway.
-
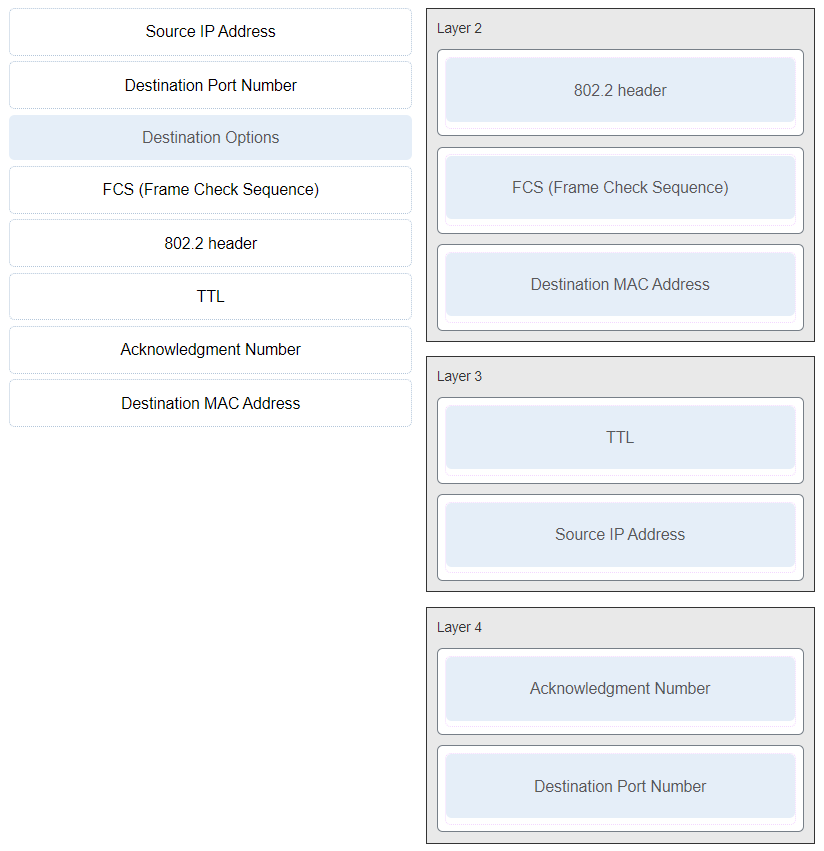
Match the header field with the appropriate layer of the OSI model. (Not all options are used.)
CCNA1 v7 – ITNv7 – Final Exam Answers 03 -
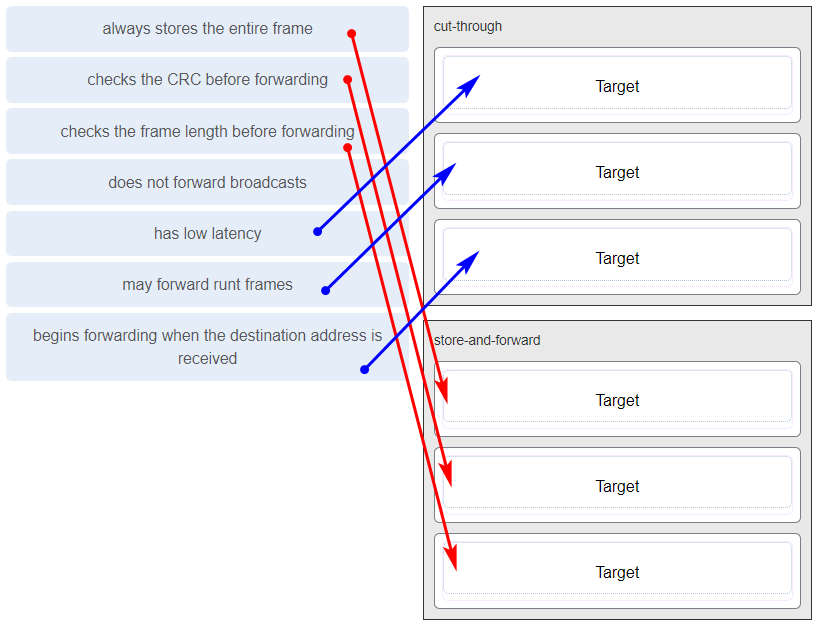
When a switch configuration includes a user-defined error threshold on a per-port basis, to which switching method will the switch revert when the error threshold is reached?
- fast-forward
- cut-through
- store-and-forward
- fragment-free
-
What are proprietary protocols?
- protocols that can be freely used by any organization or vendor
- protocols developed by private organizations to operate on any vendor hardware
- a collection of protocols known as the TCP/IP protocol suite
- protocols developed by organizations who have control over their definition and operation
Explanation:
Proprietary protocols have their definition and operation controlled by one company or vendor. Some of them can be used by different organizations with permission from the owner. The TCP/IP protocol suite is an open standard, not a proprietary protocol.
-
What is an advantage to using a protocol that is defined by an open standard?
- An open standard protocol is not controlled or regulated by standards organizations.
- A company can monopolize the market.
- It encourages competition and promotes choices.
- The protocol can only be run on equipment from a specific vendor.
Explanation:
A monopoly by one company is not a good idea from a user point of view. If a protocol can only be run on one brand, it makes it difficult to have mixed equipment in a network. A proprietary protocol is not free to use. An open standard protocol will in general be implemented by a wide range of vendors.
-
Which type of server relies on record types such as A, NS, AAAA, and MX in order to provide services?
- file
- web
- DNS
Explanation:
-
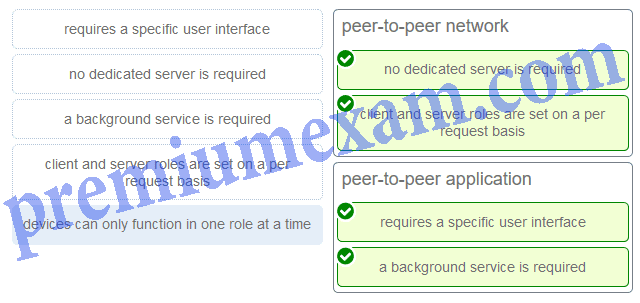
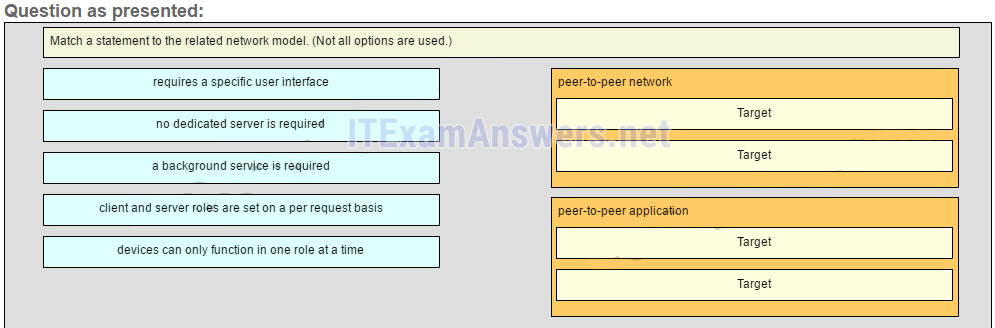
Match a statement to the related network model. (Not all options are used.)
ITN Chapter 10 Exam Answers 02 Explanation:
Peer-to-peer networks do not require the use of a dedicated server, and devices can assume both client and server roles simultaneously on a per request basis. Because they do not require formalized accounts or permissions, they are best used in limited situations. Peer-to-peer applications require a user interface and background service to be running, and can be used in more diverse situations.
-
A network administrator wants to have the same network mask for all networks at a particular small site. The site has the following networks and number of devices:
IP phones – 22 addresses
PCs – 20 addresses needed
Printers – 2 addresses needed
Scanners – 2 addresses neededThe network administrator has deemed that 192.168.10.0/24 is to be the network used at this site. Which single subnet mask would make the most efficient use of the available addresses to use for the four subnetworks?
- 255.255.255.240
- 255.255.255.0
- 255.255.255.192
- 255.255.255.224
- 255.255.255.248
- 255.255.255.252
Explanation:
-
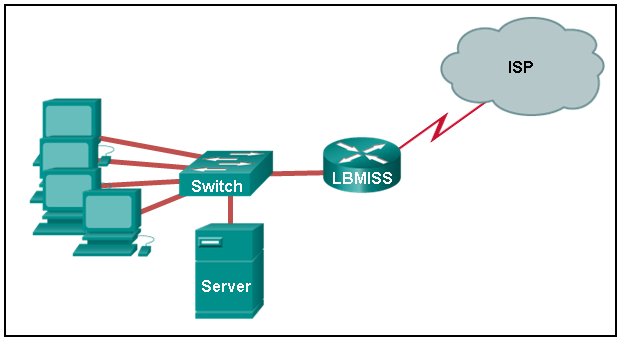
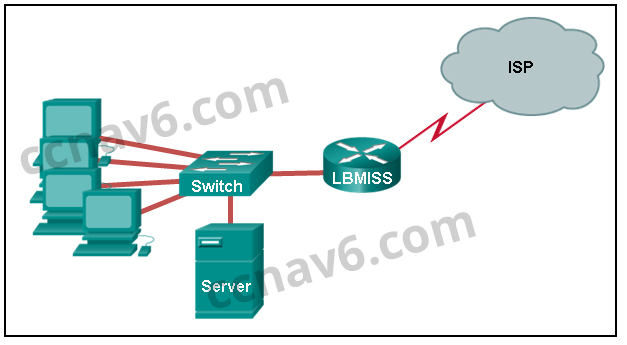
Refer to the exhibit. The network administrator has assigned the LAN of LBMISS an address range of 192.168.10.0. This address range has been subnetted using a /29 prefix. In order to accommodate a new building, the technician has decided to use the fifth subnet for configuring the new network (subnet zero is the first subnet). By company policies, the router interface is always assigned the first usable host address and the workgroup server is given the last usable host address. Which configuration should be entered into the properties of the workgroup server to allow connectivity to the Internet?
CCNA1 v7 – ITNv7 – Final Exam Answers 02 - IP address: 192.168.10.38 subnet mask: 255.255.255.248, default gateway: 192.168.10.33
- IP address: 192.168.10.38 subnet mask: 255.255.255.240, default gateway: 192.168.10.33
- IP address: 192.168.10.254 subnet mask: 255.255.255.0, default gateway: 192.168.10.1
- IP address: 192.168.10.41 subnet mask: 255.255.255.248, default gateway: 192.168.10.46
- IP address: 192.168.10.65 subnet mask: 255.255.255.240, default gateway: 192.168.10.76
Explanation:
-
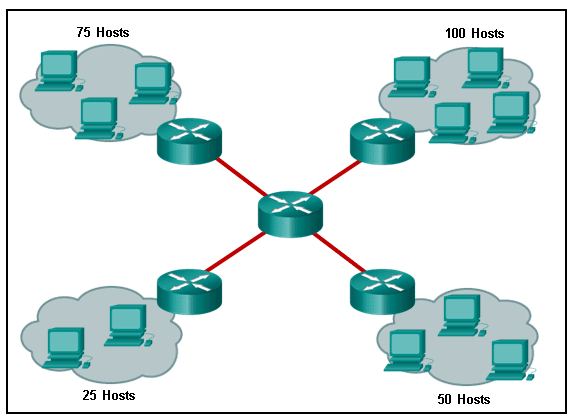
Refer to the exhibit. A network engineer has been given the network address of 192.168.99.0 and a subnet mask of 255.255.255.192 to subnet across the four networks shown. How many total host addresses are unused across all four subnets?
CCNA1 v7 – ITNv7 – Final Exam Answers 01 - 158
- 200
- 224
- 88
- 72
Explanation:
-
What would be the interface ID of an IPv6 enabled interface with a MAC address of 1C-6F-65-C2-BD-F8 when the interface ID is generated by using the EUI-64 process?
- 1E6F:65FF:FEC2:BDF8
- C16F:65FF:FEC2:BDF8
- 0C6F:65FF:FEC2:BDF8
- 106F:65FF:FEC2:BDF8
-
Which information does the show startup-config command display?
- the IOS image copied into RAM
- the bootstrap program in the ROM
- the contents of the saved configuration file in the NVRAM
- the contents of the current running configuration file in the RAM
-
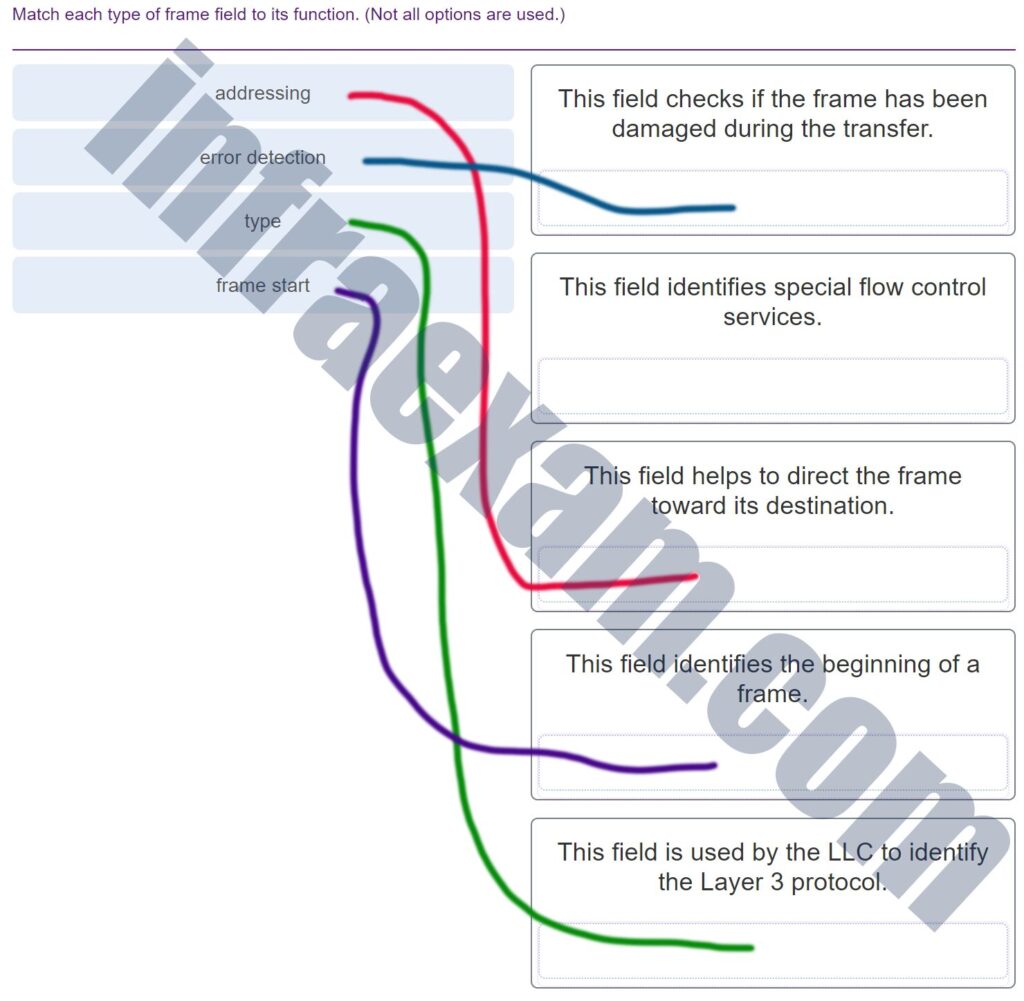
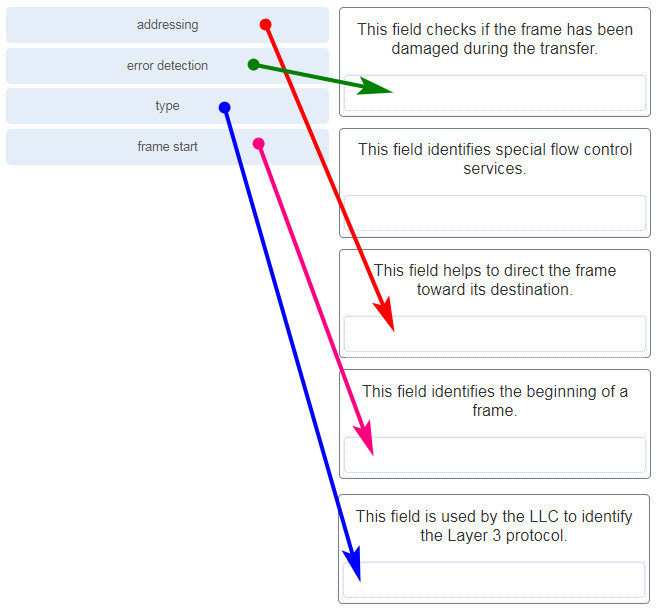
Match each type of frame field to its function. (Not all options are used.)
CCNA1 v7 Final Exam Answers 004 -
What are two primary responsibilities of the Ethernet MAC sublayer? (Choose two.)
- accessing the media
- data encapsulation
- logical addressing
- error detection
- frame delimiting
-
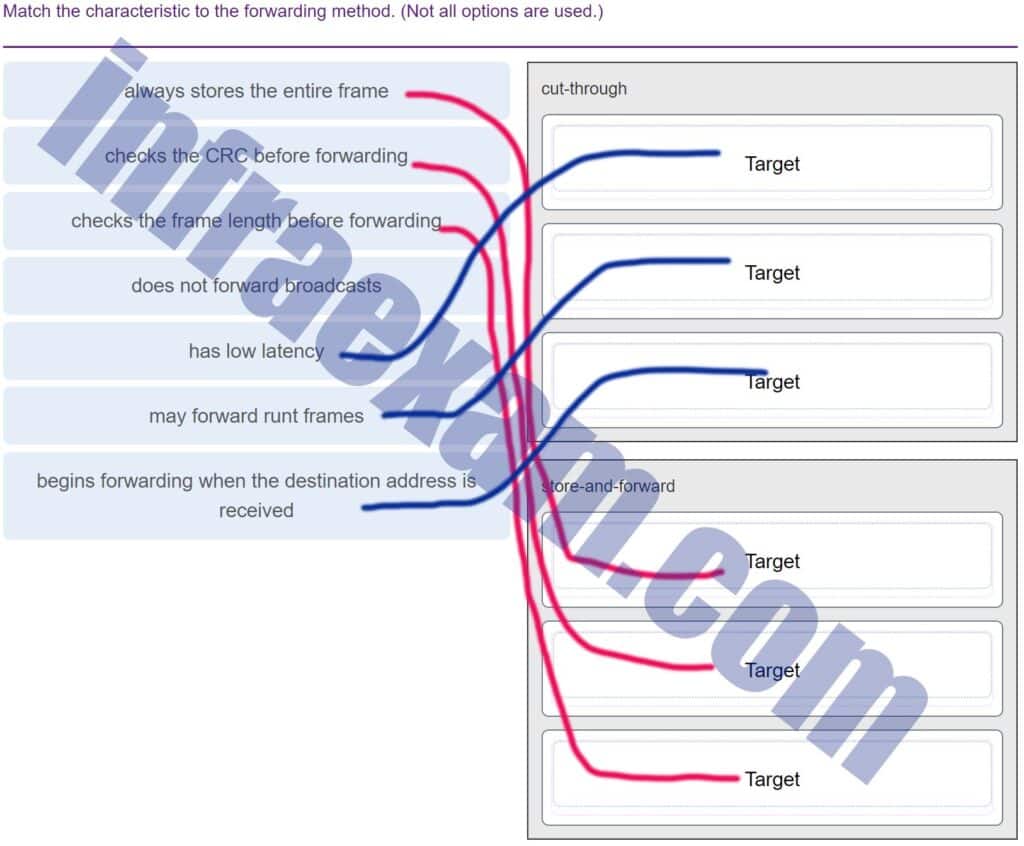
Match the characteristic to the forwarding method. (Not all options are used.)
CCNA1 v7 Final Exam Answers 005 -
Which switching method drops frames that fail the FCS check?
- store-and-forward switching
- ingress port buffering
- cut-through switching
- borderless switching
-
What is an advantage for small organizations of adopting IMAP instead of POP?
- IMAP sends and retrieves email, but POP only retrieves email.
- POP only allows the client to store messages in a centralized way, while IMAP allows distributed storage.
- Messages are kept in the mail servers until they are manually deleted from the email client.
- When the user connects to a POP server, copies of the messages are kept in the mail server for a short time, but IMAP keeps them for a long time.
Explanation:
-
A wired laser printer is attached to a home computer. That printer has been shared so that other computers on the home network can also use the printer. What networking model is in use?
- point-to-point
- client-based
- peer-to-peer (P2P)
- master-slave
Explanation:
-
A network administrator is adding a new LAN to a branch office. The new LAN must support 200 connected devices. What is the smallest network mask that the network administrator can use for the new network?
- 255.255.255.224
- 255.255.255.240
- 255.255.255.192
- 255.255.255.0
-
Which wireless technology has low-power and data rate requirements making it popular in home automation applications?
- ZigBee
- 5G
- Wi-Fi
- LoRaWAN
-
What are two characteristics shared by TCP and UDP? (Choose two.)
- ability to to carry digitized voice
- 3-way handshake
- default window size
- connectionless communication
- port numbering
- use of checksum
Explanation:
-
A client packet is received by a server. The packet has a destination port number of 69. What service is the client requesting?
- DHCP
- SMTP
- TFTP
- DNS
-
What service is provided by Internet Messenger?
- An application that allows real-time chatting among remote users.
- Resolves domain names, such as cisco.com, into IP addresses.
- Uses encryption to provide secure remote access to network devices and servers.
- Allows remote access to network devices and servers.
-
What characteristic describes antispyware?
- a tunneling protocol that provides remote users with secure access into the network of an organization
- a network device that filters access and traffic coming into a network
- applications that protect end devices from becoming infected with malicious software
- software on a router that filters traffic based on IP addresses or applications
-
A network administrator wants to have the same subnet mask for three subnetworks at a small site. The site has the following networks and numbers of devices:
Subnetwork A: IP phones – 10 addresses
Subnetwork B: PCs – 8 addresses
Subnetwork C: Printers – 2 addresses
What single subnet mask would be appropriate to use for the three subnetworks?- 255.255.255.240
- 255.255.255.0
- 255.255.255.248
- 255.255.255.252
Explanation:
-
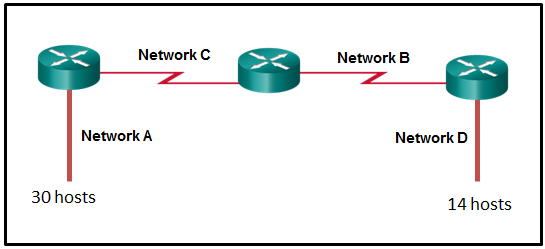
Refer to the exhibit. A company uses the address block of 128.107.0.0/16 for its network. What subnet mask would provide the maximum number of equal size subnets while providing enough host addresses for each subnet in the exhibit?
CCNA1 v7 – ITNv7 – Final Exam Answers 08 - 255.255.255.128
- 255.255.255.224
- 255.255.255.192
- 255.255.255.0
- 255.255.255.240
-
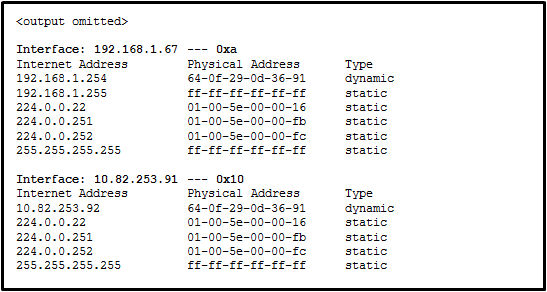
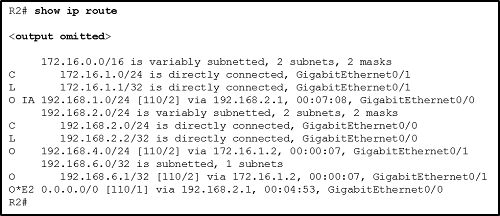
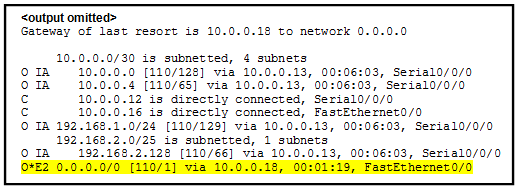
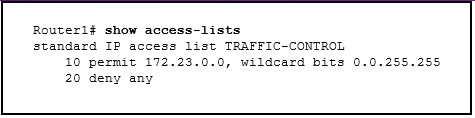
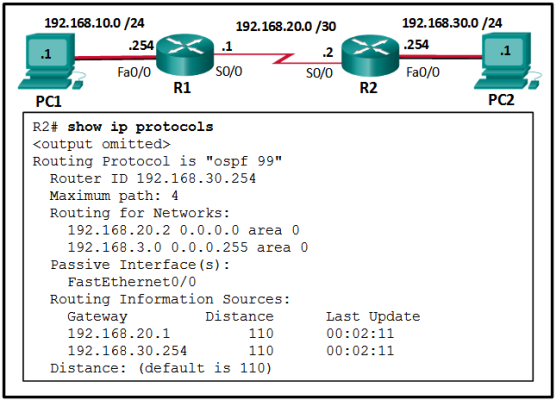
Refer to the exhibit. Which protocol was responsible for building the table that is shown?
CCNA1 v7 – ITNv7 – Final Exam Answers 09 - ARP
- DNS
- DHCP
- ICMP
-
Which two traffic types use the Real-Time Transport Protocol (RTP)? (Choose two.)
- web
- peer to peer
- file transfer
- video
- voice
-
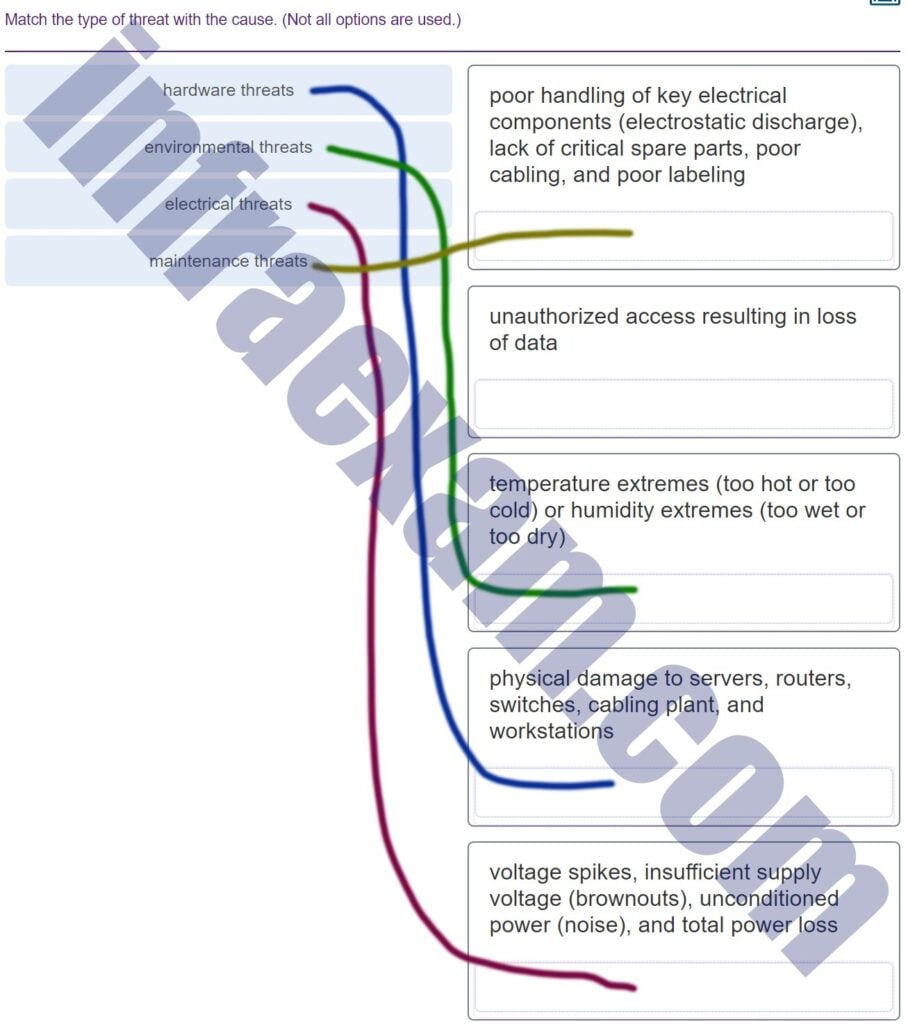
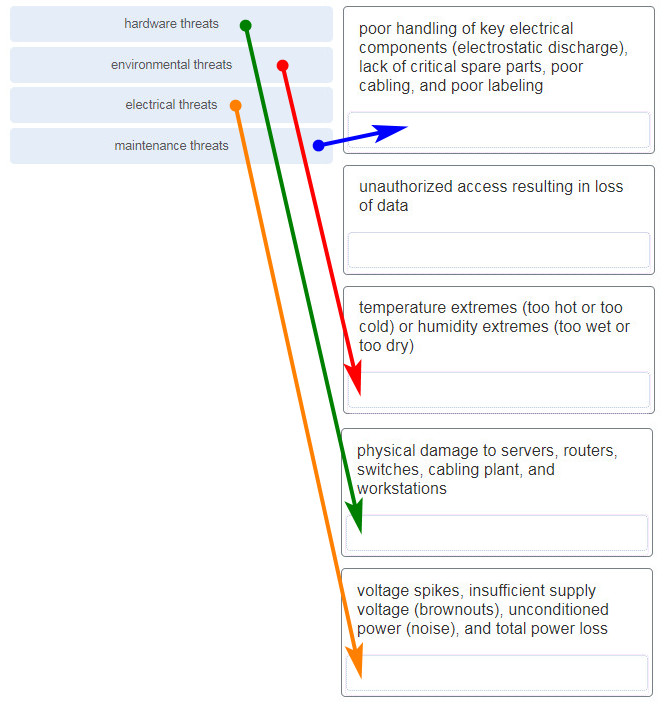
Match the type of threat with the cause. (Not all options are used.)
CCNA1 v7 Final Exam Answers 006 -
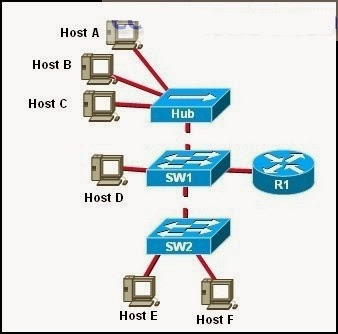
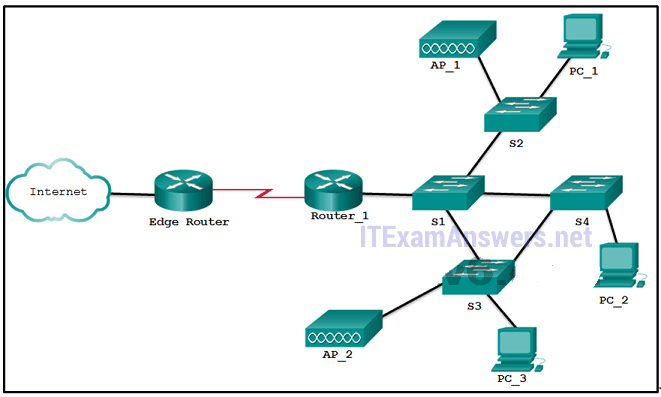
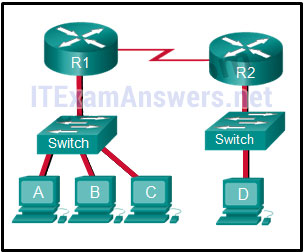
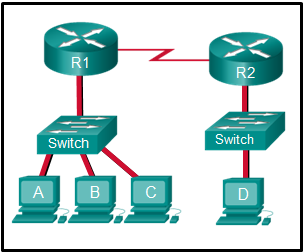
Refer to the exhibit. The switches are in their default configuration. Host A needs to communicate with host D, but host A does not have the MAC address for its default gateway. Which network hosts will receive the ARP request sent by host A?
CCNA1 v7 – ITNv7 – Final Exam Answers 10 - only hosts A, B, C, and D
- only router R1
- only hosts A, B, and C
- only hosts B and C
- only hosts B, C, and router R1
- only host D
Explanation:
-
Which value, that is contained in an IPv4 header field, is decremented by each router that receives a packet?
- Differentiated Services
- Fragment Offset
- Header Length
- Time-to-Live
-
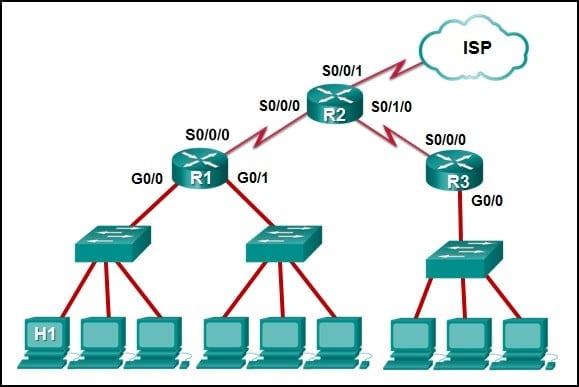
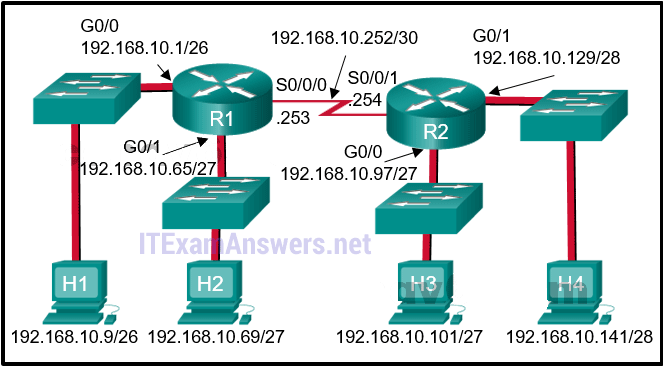
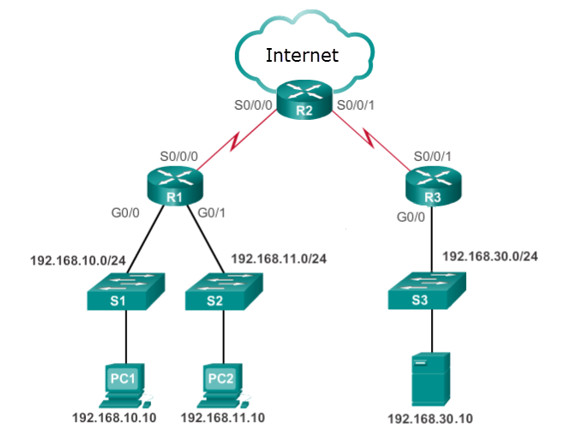
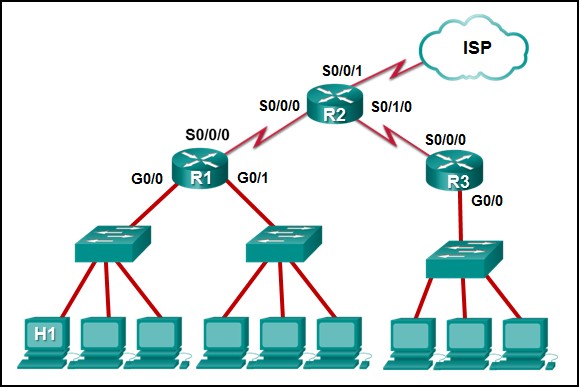
Refer to the exhibit. The IP address of which device interface should be used as the default gateway setting of host H1?
CCNA1 v7 – ITNv7 – Final Exam Answers 11 - R2: S0/0/1
- R1: G0/0
- R2: S0/0/0
- R1: S0/0/0
-
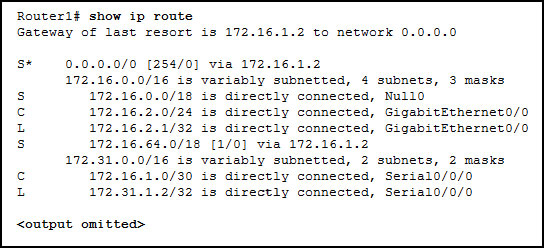
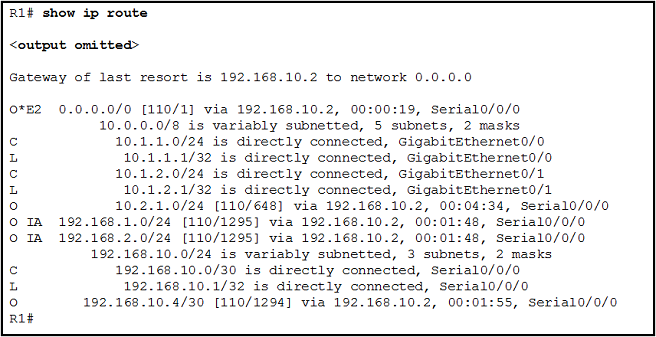
Which two statements describe features of an IPv4 routing table on a router? (Choose two.)
- Directly connected interfaces will have two route source codes in the routing table: C and S .
- The netstat -r command can be used to display the routing table of a router.
- If there are two or more possible routes to the same destination, the route associated with the higher metric value is included in the routing table.
- The routing table lists the MAC addresses of each active interface.
- If a default static route is configured in the router, an entry will be included in the routing table with source code S .
- It stores information about routes derived from the active router interfaces.
-
Three bank employees are using the corporate network. The first employee uses a web browser to view a company web page in order to read some announcements. The second employee accesses the corporate database to perform some financial transactions. The third employee participates in an important live audio conference with other corporate managers in branch offices. If QoS is implemented on this network, what will be the priorities from highest to lowest of the different data types?
- financial transactions, web page, audio conference
- financial transactions, audio conference, web page
- audio conference, financial transactions, web page
- audio conference, web page, financial transactions
Explanation:
-
What is the consequence of configuring a router with the ipv6 unicast-routing global configuration command?
- All router interfaces will be automatically activated.
- Each router interface will generate an IPv6 link-local address.
- The IPv6 enabled router interfaces begin sending ICMPv6 Router Advertisement messages.
- It statically creates a global unicast address on this router.
-
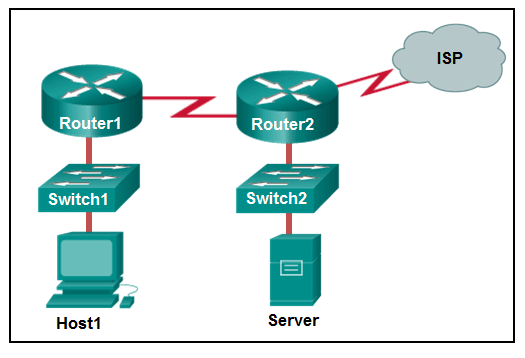
Refer to the exhibit. If Host1 were to transfer a file to the server, what layers of the TCP/IP model would be used?
CCNA1 v7 – ITNv7 – Final Exam Answers 12 - only application, Internet, and network access layers
- only application, transport, network, data link, and physical layers
- application, session, transport, network, data link, and physical layers
- only application and Internet layers
- application, transport, Internet, and network access layers
- only Internet and network access layers
Explanation:
-
The global configuration command ip default-gateway 172.16.100.1 is applied to a switch. What is the effect of this command?
- The switch can communicate with other hosts on the 172.16.100.0 network.
- The switch can be remotely managed from a host on another network.
- The switch will have a management interface with the address 172.16.100.1.
- The switch is limited to sending and receiving frames to and from the gateway 172.16.100.1.
Explanation:
-
What characteristic describes adware?
- a network device that filters access and traffic coming into a network
- an attack that slows or crashes a device or network service
- the use of stolen credentials to access private data
- software that is installed on a user device and collects information about the user
-
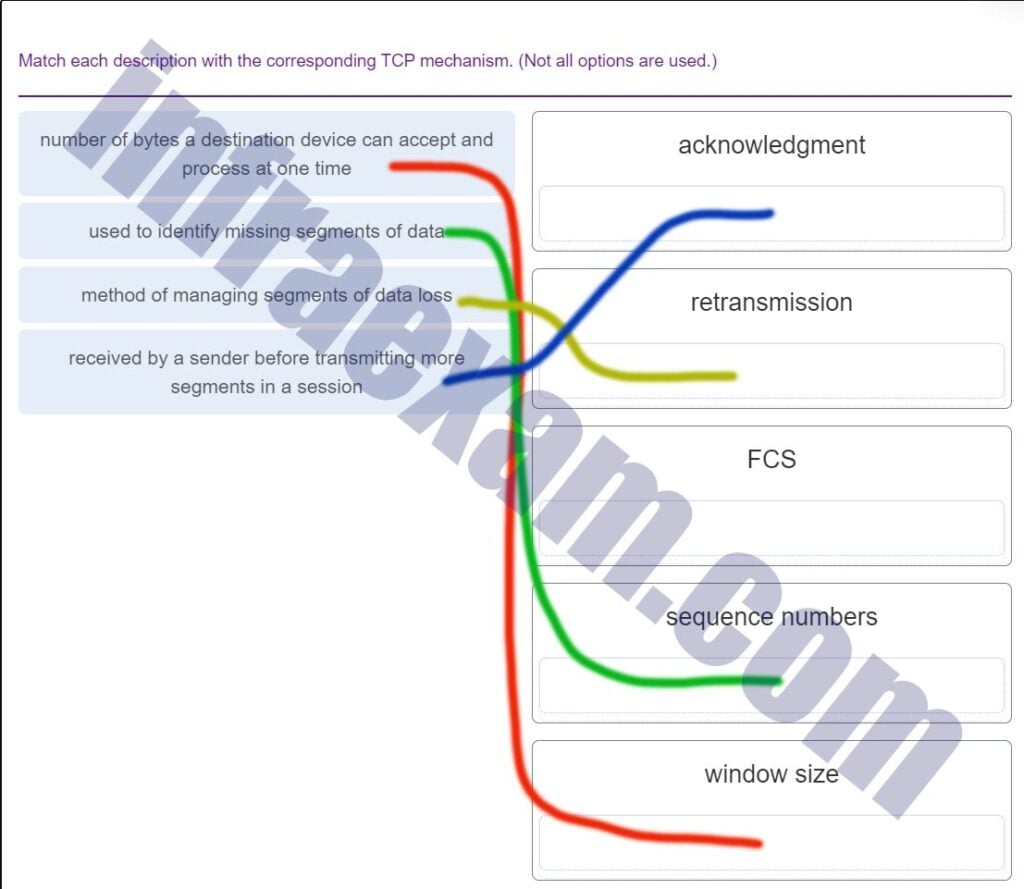
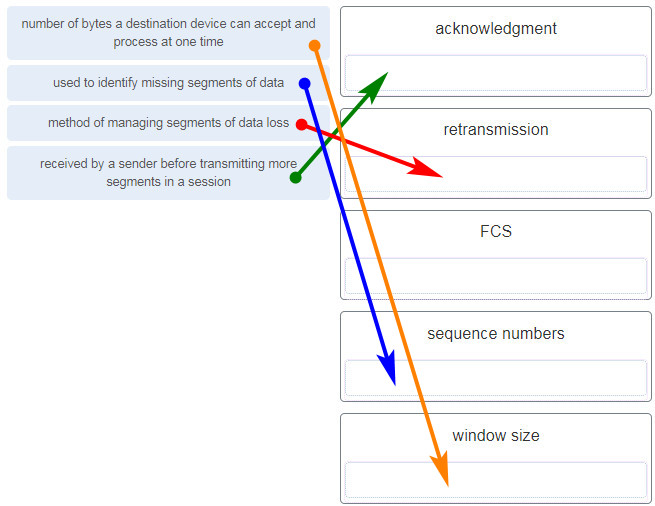
Match each description with the corresponding TCP mechanism. (Not all options are used.)
CCNA1 v7 Final Exam Answers 007 -
What is the purpose of the TCP sliding window?
- to ensure that segments arrive in order at the destination
- to request that a source decrease the rate at which it transmits data
- to inform a source to retransmit data from a specific point forward
- to end communication when data transmission is complete
-
What technique is used with UTP cable to help protect against signal interference from crosstalk?
- terminating the cable with special grounded connectors
- twisting the wires together into pairs
- wrapping a foil shield around the wire pairs
- encasing the cables within a flexible plastic sheath
Explanation:
To help prevent the effects of crosstalk, UTP cable wires are twisted together into pairs. Twisting the wires together causes the magnetic fields of each wire to cancel each other out.
-
A network technician is researching the use of fiber optic cabling in a new technology center. Which two issues should be considered before implementing fiber optic media? (Choose two.)
- Fiber optic cabling requires different termination and splicing expertise from what copper cabling requires.
- Fiber optic cabling requires specific grounding to be immune to EMI.
- Fiber optic cabling is susceptible to loss of signal due to RFI.
- Fiber optic provides higher data capacity but is more expensive than copper cabling.
- Fiber optic cable is able to withstand rough handling.
-
Users are reporting longer delays in authentication and in accessing network resources during certain time periods of the week. What kind of information should network engineers check to find out if this situation is part of a normal network behavior?
- syslog records and messages
- debug output and packet captures
- network configuration files
- the network performance baseline
-
A user is complaining that an external web page is taking longer than normal to load.The web page does eventually load on the user machine. Which tool should the technician use with administrator privileges in order to locate where the issue is in the network?
- ipconfig /displaydns
- nslookup
- tracert
- ping
-
A client packet is received by a server. The packet has a destination port number of 53. What service is the client requesting?
- SSH
- FTP
- Telnet
- DNS
-
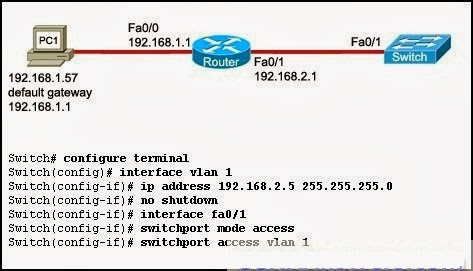
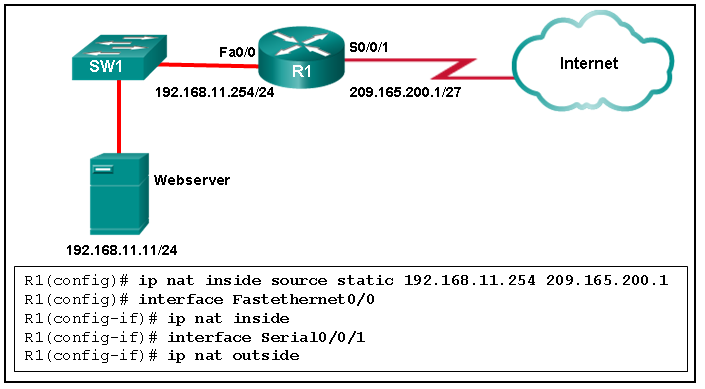
Refer to the exhibit. PC1 issues an ARP request because it needs to send a packet to PC2. In this scenario, what will happen next?
CCNA1 v7 – ITNv7 – Final Exam Answers 13 - RT1 will send an ARP reply with its Fa0/0 MAC address.
- SW1 will send an ARP reply with the PC2 MAC address.
- RT1 will send an ARP reply with the PC2 MAC address.
- SW1 will send an ARP reply with its Fa0/1 MAC address.
- PC2 will send an ARP reply with its MAC address.
Explanation:
When a network device wants to communicate with another device on the same network, it sends a broadcast ARP request. In this case, the request will contain the IP address of PC2. The destination device (PC2) sends an ARP reply with its MAC address.
-
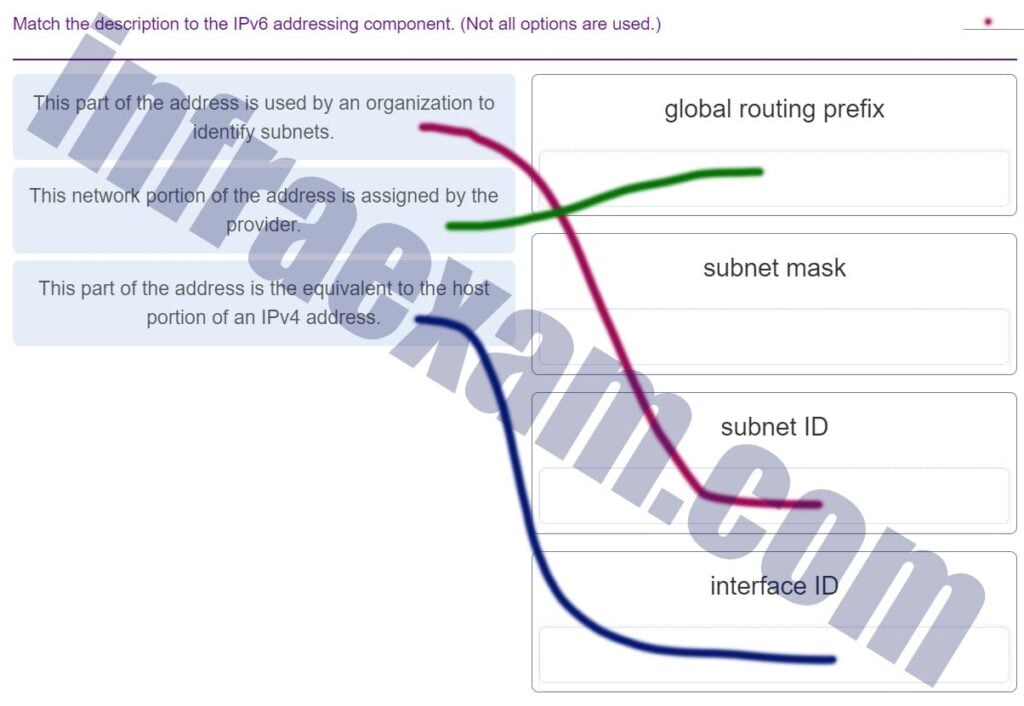
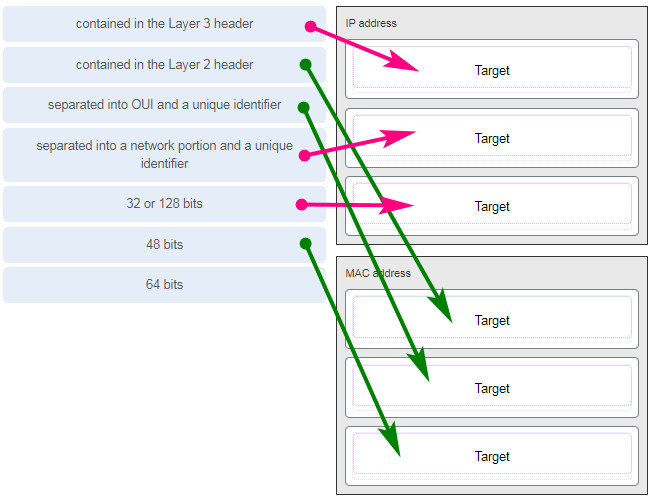
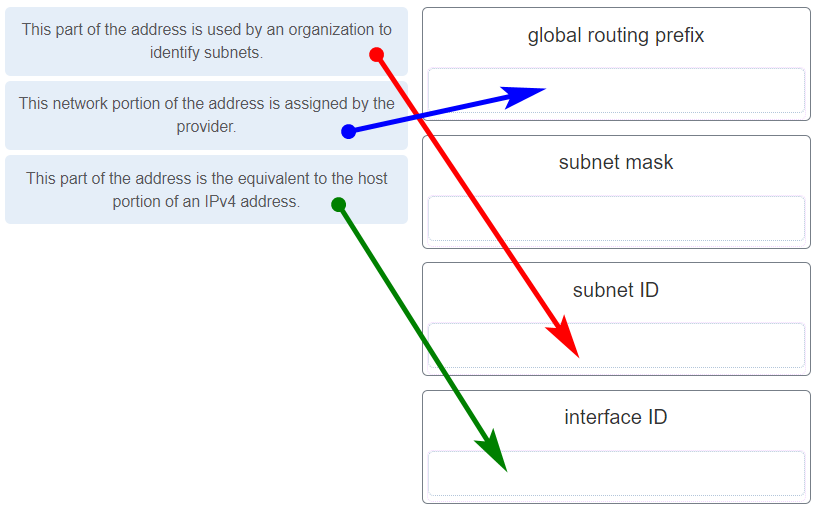
Match the description to the IPv6 addressing component. (Not all options are used.)
CCNA1 v7 Final Exam Answers 008 -
An IPv6 enabled device sends a data packet with the destination address of FF02::2. What is the target of this packet?
- all IPv6 enabled devices on the local link
- all IPv6 DHCP servers
- all IPv6 enabled devices across the network
- all IPv6 configured routers on the local link
-
What are the three parts of an IPv6 global unicast address? (Choose three.)
- subnet ID
- global routing prefix
- interface ID
- subnet mask
- broadcast address
-
What is one main characteristic of the data link layer?
- It generates the electrical or optical signals that represent the 1 and 0 on the media.
- It converts a stream of data bits into a predefined code.
- It shields the upper layer protocol from being aware of the physical medium to be used in the communication.
- It accepts Layer 3 packets and decides the path by which to forward the packet to a remote network.
-
Which type of security threat would be responsible if a spreadsheet add-on disables the local software firewall?
- Trojan horse
- brute-force attack
- DoS
- buffer overflow
Explanation:
A Trojan horse is software that does something harmful, but is hidden in legitimate software code. A denial of service (DoS) attack results in interruption of network services to users, network devices, or applications. A brute-force attack commonly involves trying to access a network device. A buffer overflow occurs when a program attempts to store more data in a memory location than it can hold.
-
What service is provided by HTTPS?
- Allows remote access to network devices and servers.
- Resolves domain names, such as cisco.com, into IP addresses.
- Uses encryption to provide secure remote access to network devices and servers.
- Uses encryption to secure the exchange of text, graphic images, sound, and video on the web.
-
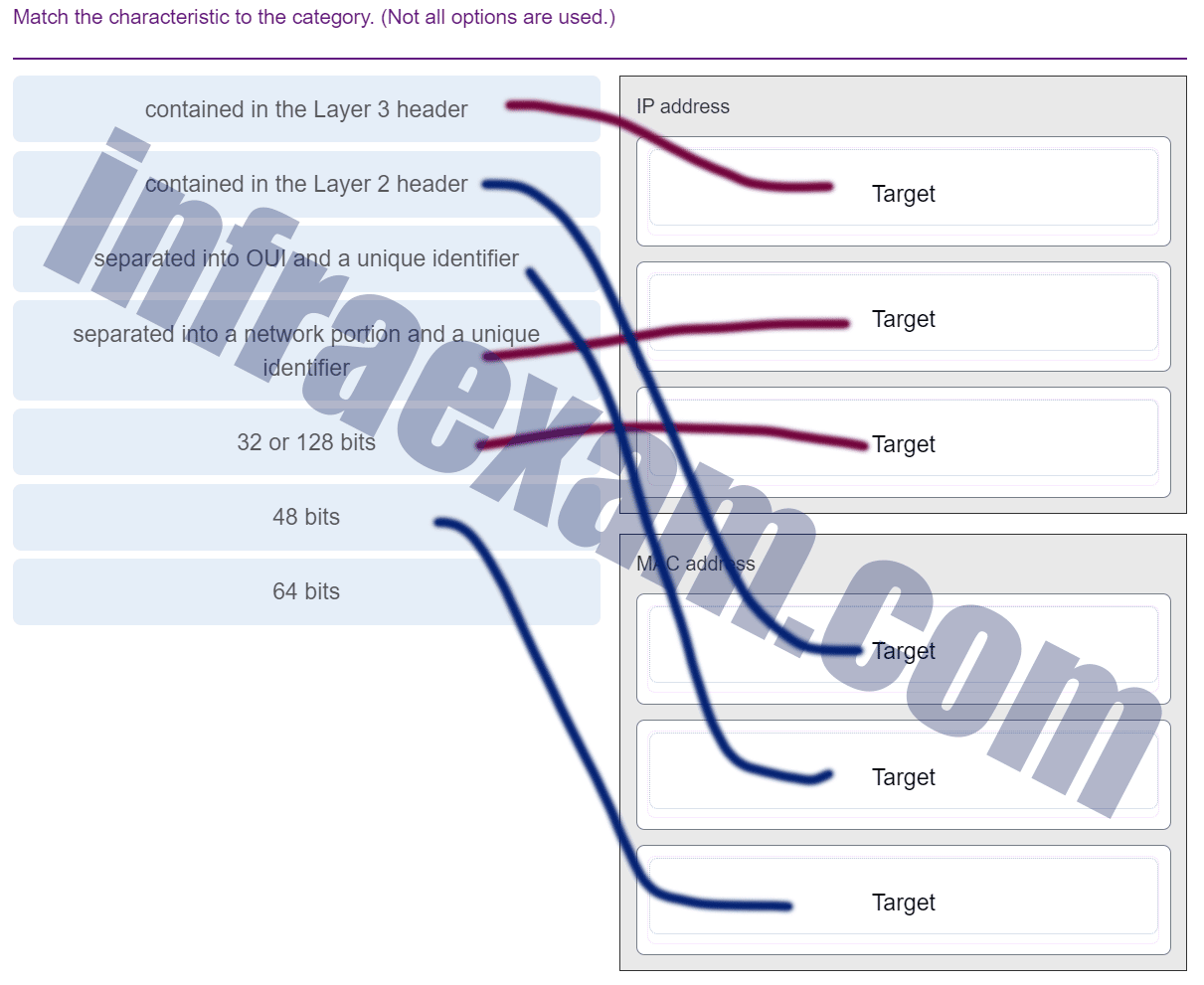
Match the characteristic to the category. (Not all options are used.)
CCNA1 v7 Final Exam Answers 009 -
Refer to the exhibit. If host A sends an IP packet to host B, what will the destination address be in the frame when it leaves host A?
CCNA1 v7 – ITNv7 – Final Exam Answers 14 - 172.168.10.65
- 172.168.10.99
- AA:AA:AA:AA:AA:AA
- CC:CC:CC:CC:CC:CC
- BB:BB:BB:BB:BB:BB
- DD:DD:DD:DD:DD:DD
-
Which two statements are correct about MAC and IP addresses during data transmission if NAT is not involved? (Choose two.)
- Destination MAC addresses will never change in a frame that goes across seven routers.
- A packet that has crossed four routers has changed the destination IP address four times.
- Every time a frame is encapsulated with a new destination MAC address, a new destination IP address is needed.
- Destination and source MAC addresses have local significance and change every time a frame goes from one LAN to another.
- Destination IP addresses in a packet header remain constant along the entire path to a target host.
-
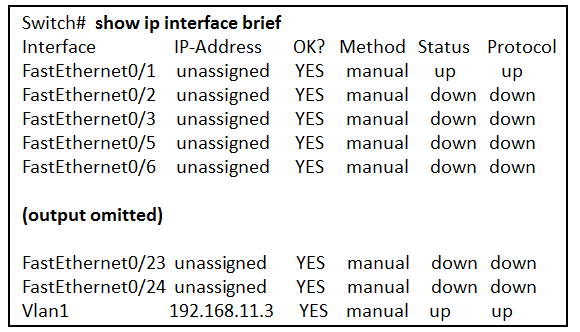
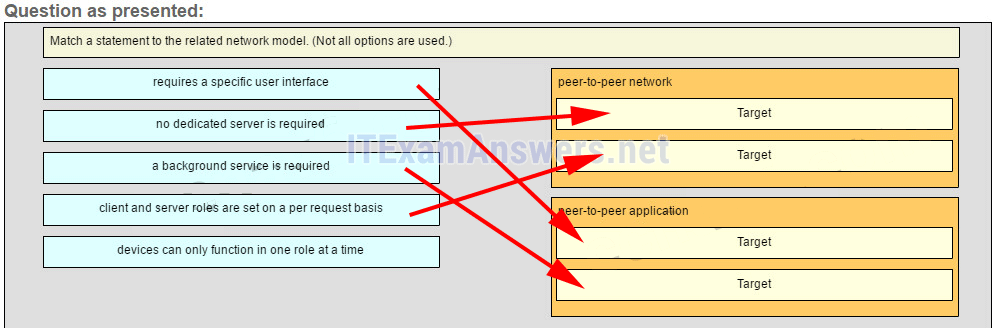
Refer to the exhibit. What three facts can be determined from the viewable output of the show ip interface brief command? (Choose three.)
CCNA1 v7 – ITNv7 – Final Exam Answers 15 - Two devices are attached to the switch.
- The default SVI has been configured.
- The switch can be remotely managed.
- Two physical interfaces have been configured.
- Passwords have been configured on the switch.
- One device is attached to a physical interface.
-
A user is executing a tracert to a remote device. At what point would a router, which is in the path to the destination device, stop forwarding the packet?
- when the values of both the Echo Request and Echo Reply messages reach zero
- when the value in the TTL field reaches zero
- when the router receives an ICMP Time Exceeded message
- when the host responds with an ICMP Echo Reply message
- when the RTT value reaches zero
Explanation:
When a router receives a traceroute packet, the value in the TTL field is decremented by 1. When the value in the field reaches zero, the receiving router will not forward the packet, and will send an ICMP Time Exceeded message back to the source.
-
What are two functions that are provided by the network layer? (Choose two.)
- carrying data between processes that are running on source and destination hosts
- directing data packets to destination hosts on other networks
- providing dedicated end-to-end connections
- placing data on the network medium
- providing end devices with a unique network identifier
-
A network administrator is adding a new LAN to a branch office. The new LAN must support 61 connected devices. What is the smallest network mask that the network administrator can use for the new network?
- 255.255.255.224
- 255.255.255.240
- 255.255.255.192
- 255.255.255.128
-
What characteristic describes spyware?
- a network device that filters access and traffic coming into a network
- software that is installed on a user device and collects information about the user
- an attack that slows or crashes a device or network service
- the use of stolen credentials to access private data
-
What are three commonly followed standards for constructing and installing cabling? (Choose three.)
- pinouts
- tensile strength of plastic insulator
- cable lengths
- connector types
- cost per meter (foot)
- connector color
-
Which connector is used with twisted-pair cabling in an Ethernet LAN?
-
What attribute of a NIC would place it at the data link layer of the OSI model?
- attached Ethernet cable
- TCP/IP protocol stack
- IP address
- RJ-45 port
- MAC address
-
A network administrator needs to keep the user ID, password, and session contents private when establishing remote CLI connectivity with a switch to manage it. Which access method should be chosen?
- AUX
- Telnet
- SSH
- Console
-
A user sends an HTTP request to a web server on a remote network. During encapsulation for this request, what information is added to the address field of a frame to indicate the destination?
- the network domain of the destination host
- the MAC address of the default gateway
- the IP address of the default gateway
- the MAC address of the destination host
-
Which two commands can be used on a Windows host to display the routing table? (Choose two.)
- route print
- show ip route
- netstat -r
- netstat -s
- tracert
Answers Explanation & Hints:
On a Windows host, the route print or netstat -r commands can be used to display the host routing table. Both commands generate the same output. On a router, the show ip route command is used to display the routing table. The netstat –s command is used to display per-protocol statistics. The tracert command is used to display the path that a packet travels to its destination.
-
Match each description with an appropriate IP address. (Not all options are used.)
CCNA1 v7 & v7.02 – ITNv7 – Final Exam Answers 001 -
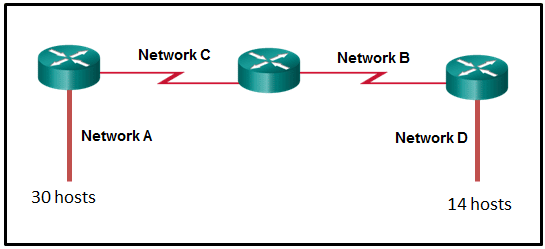
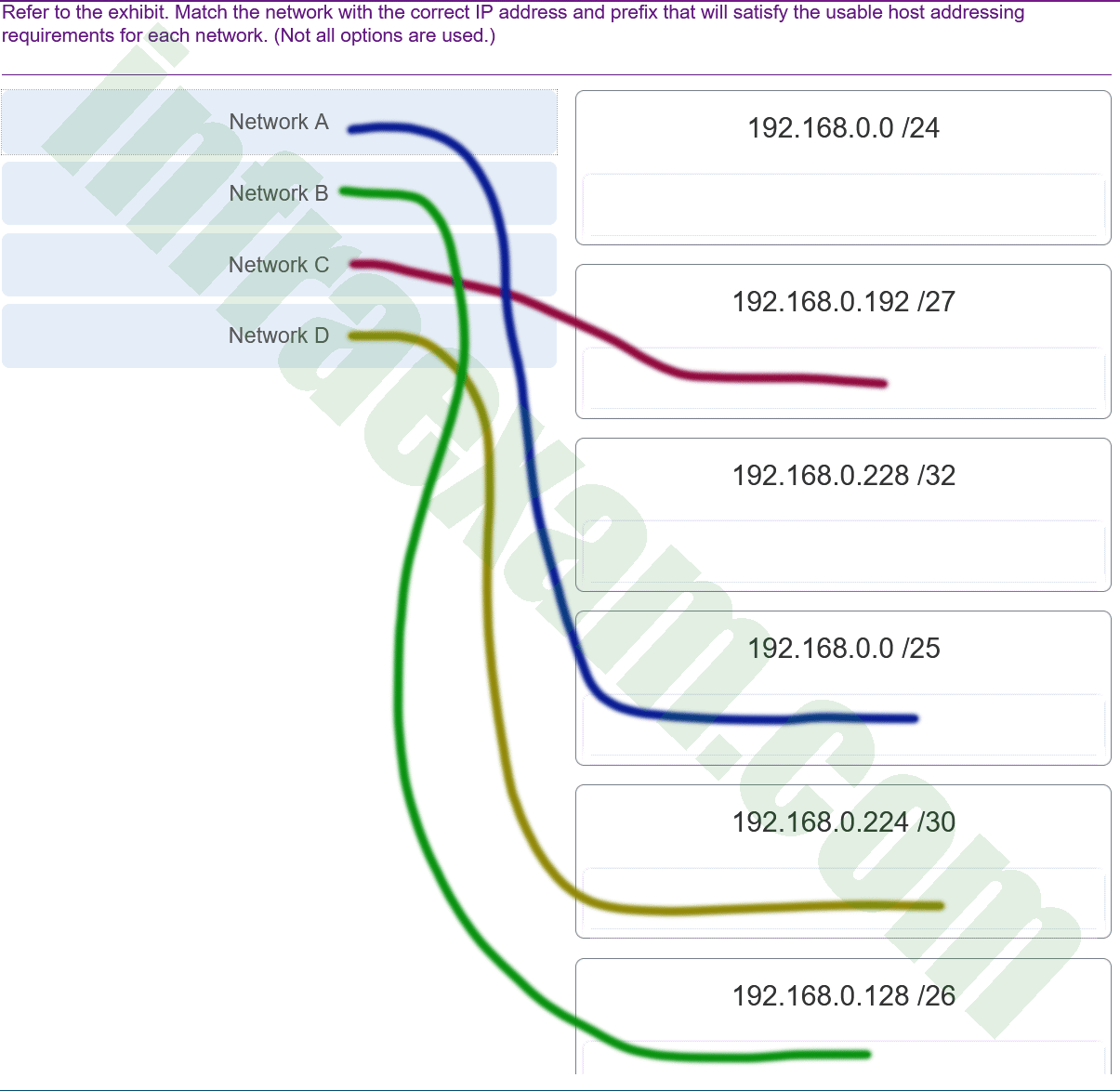
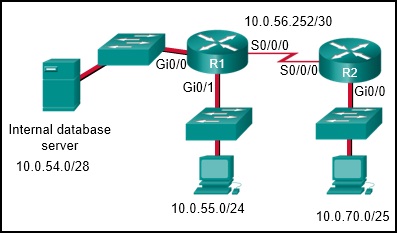
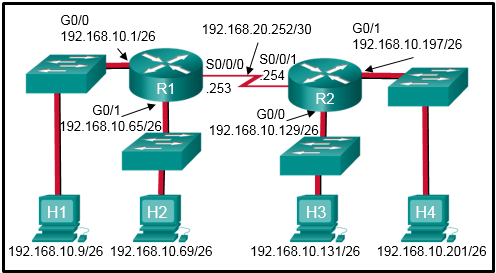
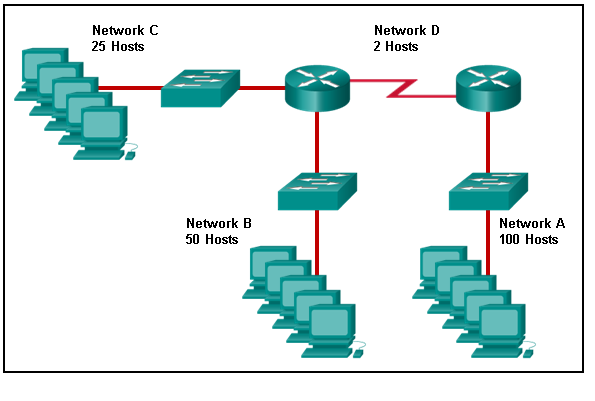
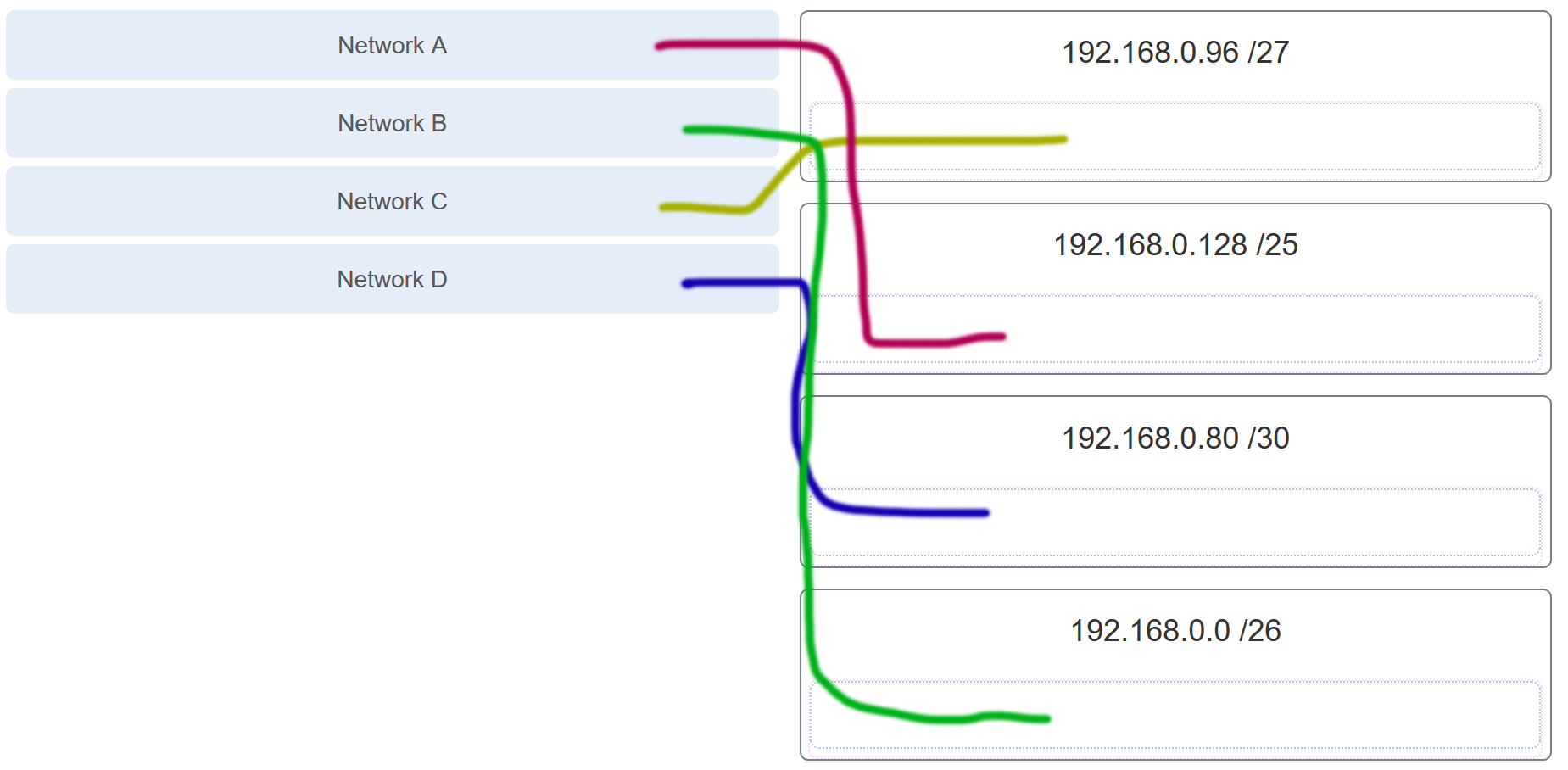
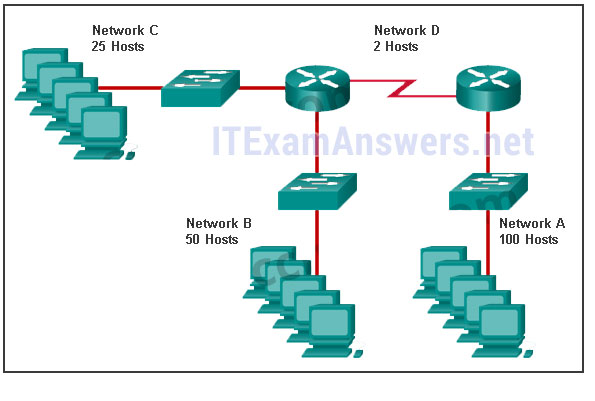
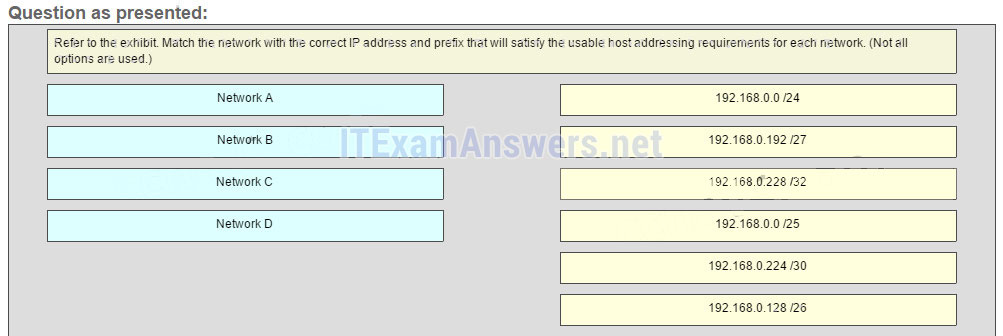
Refer to the exhibit. Match the network with the correct IP address and prefix that will satisfy the usable host addressing requirements for each network. (Not all options are used.)
CCNA1 v7 & v7.02 – ITNv7 – Final Exam Answers 01 CCNA1 v7 & v7.02 – ITNv7 – Final Exam Answers 002 Explanation:
Network A needs to use 192.168.0.0 /25 which yields 128 host addresses.
Network B needs to use 192.168.0.128 /26 which yields 64 host addresses.
Network C needs to use 192.168.0.192 /27 which yields 32 host addresses.
Network D needs to use 192.168.0.224 /30 which yields 4 host addresses. -
A technician with a PC is using multiple applications while connected to the Internet. How is the PC able to keep track of the data flow between multiple application sessions and have each application receive the correct packet flows?
- The data flow is being tracked based on the source port number that is used by each application.
- The data flow is being tracked based on the destination IP address that is used by the PC of the technician.
- The data flow is being tracked based on the source IP address that is used by the PC of the technician.
- The data flow is being tracked based on the destination MAC address of the technician PC.
Explanation:
The source port number of an application is randomly generated and used to individually keep track of each session connecting out to the Internet. Each application will use a unique source port number to provide simultaneous communication from multiple applications through the Internet.
-
A client packet is received by a server. The packet has a destination port number of 80. What service is the client requesting?
- DNS
- HTTP
- DHCP
- SMTP
-
A user is attempting to access http://www.cisco.com/ without success. Which two configuration values must be set on the host to allow this access? (Choose two.)
- source port number
- HTTP server
- source MAC address
- DNS server
- default gateway
-
What method is used to manage contention-based access on a wireless network?
- CSMA/CD
- priority ordering
- CSMA/CA
- token passing
-
What are two ICMPv6 messages that are not present in ICMP for IPv4? (Choose two.)
- Router Advertisement
- Destination Unreachable
- Neighbor Solicitation
- Route Redirection
- Host Confirmation
- Time Exceeded
-
An organization is assigned an IPv6 address block of 2001:db8:0:ca00::/56. How many subnets can be created without using bits in the interface ID space?
- 4096
- 256
- 512
- 1024
-
What subnet mask is needed if an IPv4 network has 40 devices that need IP addresses and address space is not to be wasted?
- 255.255.255.224
- 255.255.255.128
- 255.255.255.240
- 255.255.255.192
- 255.255.255.0
-
A host is trying to send a packet to a device on a remote LAN segment, but there are currently no mappings in the ARP cache. How will the device obtain a destination MAC address?
- It will send an ARP request for the MAC address of the destination device.
- It will send the frame with a broadcast MAC address.
- It will send the frame and use the device MAC address as the destination.
- It will send an ARP request for the MAC address of the default gateway.
- It will send an ARP request to the DNS server for the destination MAC address.
-
What characteristic describes a virus?
- the use of stolen credentials to access private data
- a network device that filters access and traffic coming into a network
- malicious software or code running on an end device
- an attack that slows or crashes a device or network service
-
A disgruntled employee is using some free wireless networking tools to determine information about the enterprise wireless networks. This person is planning on using this information to hack the wireless network. What type of attack is this?
- access
- DoS
- Trojan horse
- reconnaissance
-
What service is provided by POP3?
- Uses encryption to provide secure remote access to network devices and servers.
- Retrieves email from the server by downloading the email to the local mail application of the client.
- Allows remote access to network devices and servers.
- An application that allows real-time chatting among remote users.
-
What command can be used on a Windows PC to see the IP configuration of that computer?
- ipconfig
- show interfaces
- ping
- show ip interface brief
-
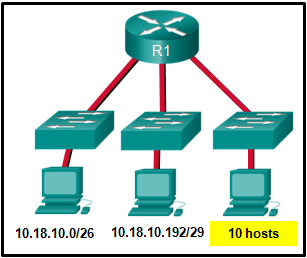
Refer to the exhibit. Which two network addresses can be assigned to the network containing 10 hosts? Your answers should waste the fewest addresses, not reuse addresses that are already assigned, and stay within the 10.18.10.0/24 range of addresses. (Choose two.)
CCNA1 v7 & v7.02 – ITNv7 – Final Exam Answers 02 - 10.18.10.224/27
- 10.18.10.208/28
- 10.18.10.200/27
- 10.18.10.200/28
- 10.18.10.224/28
Answers Explanation & Hints:
Addresses 10.18.10.0 through 10.18.10.63 are taken for the leftmost network. Addresses 192 through 199 are used by the center network. Because 4 host bits are needed to accommodate 10 hosts, a /28 mask is needed. 10.18.10.200/28 is not a valid network number. Two subnets that can be used are 10.18.10.208/28 and 10.18.10.224/28.
-
A client packet is received by a server. The packet has a destination port number of 110. What service is the client requesting?
- DNS
- DHCP
- POP3
- SMTP
-
Which layer of the TCP/IP model provides a route to forward messages through an internetwork?
- transport
- application
- network access
- internet
-
What characteristic describes identity theft?
- a tunneling protocol that provides remote users with secure access into the network of an organization
- the use of stolen credentials to access private data
- software that identifies fast-spreading threats
- software on a router that filters traffic based on IP addresses or applications
-
What two security solutions are most likely to be used only in a corporate environment? (Choose two.)
- intrusion prevention systems
- antivirus software
- antispyware
- strong passwords
- virtual private networks
-
What service is provided by DNS?
- Allows for data transfers between a client and a file server.
- Uses encryption to secure the exchange of text, graphic images, sound, and video on the web.
- A basic set of rules for exchanging text, graphic images, sound, video, and other multimedia files on the web.
- Resolves domain names, such as cisco.com, into IP addresses.
-
Which wireless technology has low-power and low-data rate requirements making it popular in IoT environments?
- Bluetooth
- Zigbee
- WiMAX
- Wi-Fi
Answers Explanation & Hints:
Zigbee is a specification used for low-data rate, low-power communications. It is intended for applications that require short-range, low data-rates and long battery life. Zigbee is typically used for industrial and Internet of Things (IoT) environments such as wireless light switches and medical device data collection.
-
What characteristic describes a VPN?
- software on a router that filters traffic based on IP addresses or applications
- a tunneling protocol that provides remote users with secure access into the network of an organization
- a network device that filters access and traffic coming into a network
- software that identifies fast-spreading threats
-
A network administrator is adding a new LAN to a branch office. The new LAN must support 4 connected devices. What is the smallest network mask that the network administrator can use for the new network?
- 255.255.255.192
- 255.255.255.248
- 255.255.255.240
- 255.255.255.224
-
During the process of forwarding traffic, what will the router do immediately after matching the destination IP address to a network on a directly connected routing table entry?
- switch the packet to the directly connected interface
- discard the traffic after consulting the route table
- look up the next-hop address for the packet
- analyze the destination IP address
-
What service is provided by BOOTP?
- Allows for data transfers between a client and a file server.
- Legacy application that enables a diskless workstation to discover its own IP address and find a BOOTP server on the network.
- Uses encryption to secure the exchange of text, graphic images, sound, and video on the web.
- A basic set of rules for exchanging text, graphic images, sound, video, and other multimedia files on the web.
-
A client packet is received by a server. The packet has a destination port number of 21. What service is the client requesting?
- DHCP
- FTP
- TFTP
- DNS
-
Match each description to its corresponding term. (Not all options are used.)
CCNA1 v7 & v7.02 – ITNv7 – Final Exam Answers 003 -
A technician can ping the IP address of the web server of a remote company but cannot successfully ping the URL address of the same web server. Which software utility can the technician use to diagnose the problem?
- tracert
- netstat
- nslookup
- ipconfig
Explanation:
-
What two ICMPv6 message types must be permitted through IPv6 access control lists to allow resolution of Layer 3 addresses to Layer 2 MAC addresses? (Choose two.)
- echo requests
- router solicitations
- router advertisements
- neighbor advertisements
- echo replies
- neighbor solicitations
-
Refer to the exhibit. The switches have a default configuration. Host A needs to communicate with host D, but host A does not have the MAC address for the default gateway. Which network devices will receive the ARP request sent by host A?
CCNA1 v7 & v7.02 – ITNv7 – Final Exam Answers 03 - only hosts A, B, C, and D
- only hosts A, B, and C
- only host D
- only hosts B, C, and router R1
- only router R1
- only hosts B and C
-
Which two functions are performed at the LLC sublayer of the OSI Data Link Layer to facilitate Ethernet communication? (Choose two.)
- integrates Layer 2 flows between 10 Gigabit Ethernet over fiber and 1 Gigabit Ethernet over copper
- places information in the Ethernet frame that identifies which network layer protocol is being encapsulated by the frame
- implements trailer with frame check sequence for error detection
- applies source and destination MAC addresses to Ethernet frame
- enables IPv4 and IPv6 to utilize the same physical medium
-
Two pings were issued from a host on a local network. The first ping was issued to the IP address of the default gateway of the host and it failed. The second ping was issued to the IP address of a host outside the local network and it was successful. What is a possible cause for the failed ping?
- The default gateway is not operational.
- The default gateway device is configured with the wrong IP address.
- The TCP/IP stack on the default gateway is not working properly.
- Security rules are applied to the default gateway device, preventing it from processing ping requests.
-
What is a benefit of using cloud computing in networking?
- Technology is integrated into every-day appliances allowing them to interconnect with other devices, making them more ‘smart’ or automated.
- Network capabilities are extended without requiring investment in new infrastructure, personnel, or software.
- Home networking uses existing electrical wiring to connect devices to the network wherever there is an electrical outlet, saving the cost of installing data cables.
- End users have the freedom to use personal tools to access information and communicate across a business network.
Answers Explanation & Hints:
-
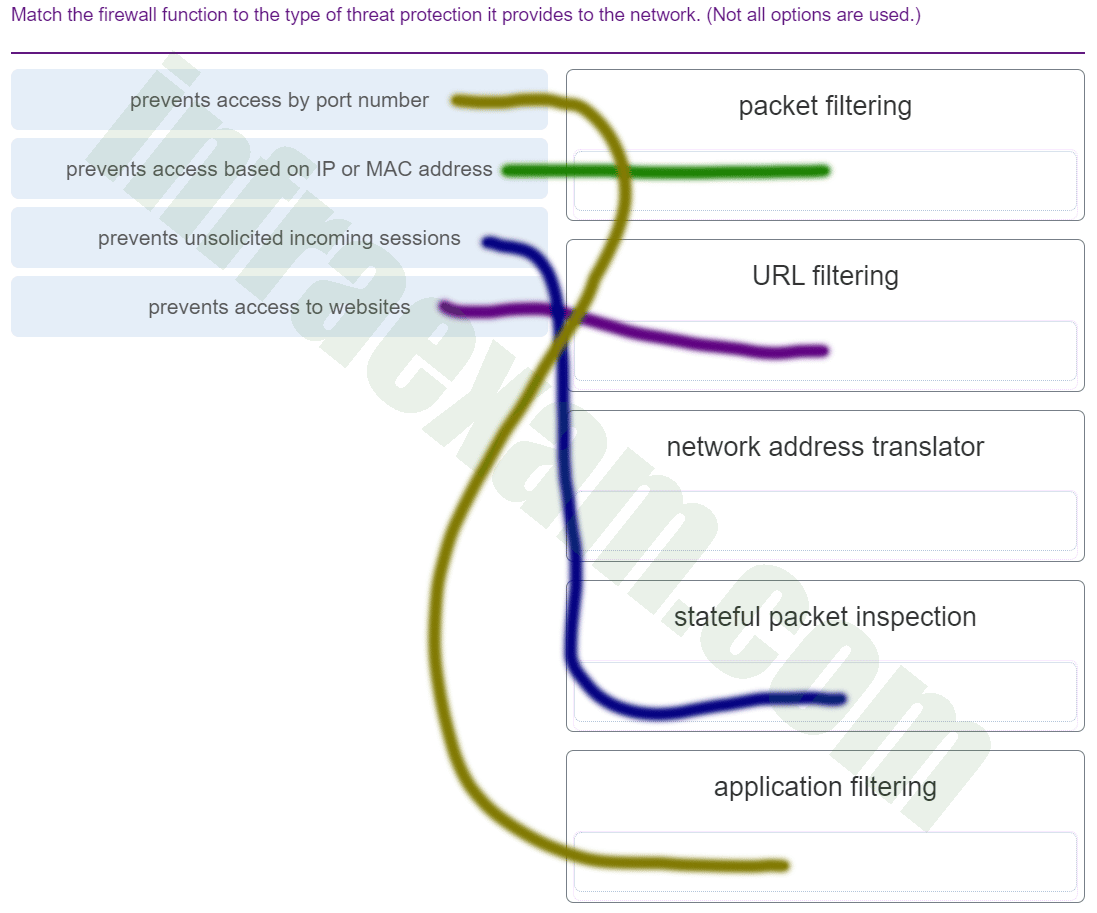
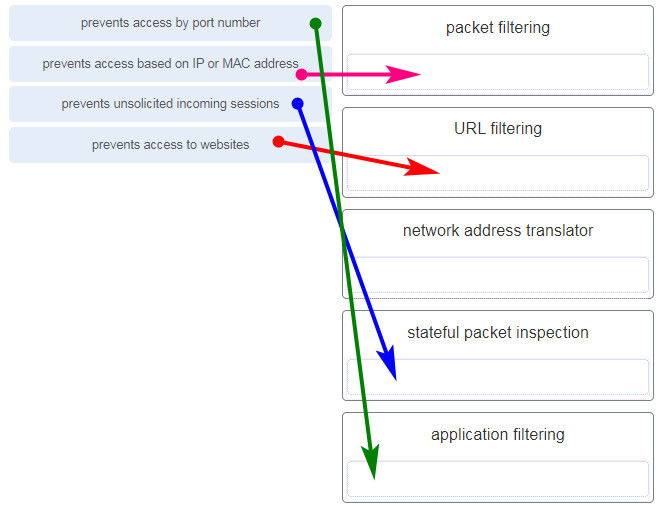
Match the firewall function to the type of threat protection it provides to the network. (Not all options are used.)
CCNA1 v7 & v7.02 – ITNv7 – Final Exam Answers 004 Answers Explanation & Hints:
Application filters prevent access based on Layer 4 port numbers.
Packet filters prevent access based on IP or MAC address.
URL filters prevent access to web site URLs or content.
Stateful packet inspection prevents unsolicited incoming sessions.
Network address translators translate internal IP addresses to to outside IP addresses and do not prevent network attacks. -
What service is provided by SMTP?
- Allows remote access to network devices and servers.
- Uses encryption to provide secure remote access to network devices and servers.
- Allows clients to send email to a mail server and the servers to send email to other servers.
- An application that allows real-time chatting among remote users.
-
A client packet is received by a server. The packet has a destination port number of 22. What service is the client requesting?
- SSH
- DNS
- DHCP
- TFTP
-
Recommend
4.4
43
votes
Article Rating
Final Exam — Выпускной экзамен Cisco.
Внимание! Не все ответы правильные. Задание выполнено на оценку 79,2 — это хорошая оценка. Но старайтесь думать своей головой тоже.
Правильные ответы отмечены знаком +
Согласно политике профилактического обслуживания компании, каждые полгода для каждого компьютера должна создаваться новая точка восстановления. Какие существуют способы создания этой точки восстановления?
Выбрать Пуск > Панель управления > Стандартные > Служебные > Восстановление системы > Создание точки восстановления.
В интерфейсе командной строки ввести restore /cn.
Правой кнопкой мыши щелкнуть Мой компьютер и выбрать Свойства > Восстановление > Создание точки восстановления.
+Выбрать Пуск > Программы > Стандартные > Служебные > Восстановление системы > Создание точки восстановления.
———
После входа в систему компьютера пользователь может просматривать файлы, но не может загружать их. Какое действие может выполнить администратор, чтобы пользователи могли загружать файлы, но не могли удалять их?
Установить уровень разрешений для папки «Чтение».
Установить уровень разрешений для папки «Полный доступ».
+Установить уровень разрешений для файла «Чтение и выполнение».
Установить уровень разрешений для папки «Изменение».
———
В новом офисе смотрителей парка, состоящем из одного помещения, выполняется развертывание беспроводной локальной сети. Офис расположен в самой высокой точке национального парка. После выполнения тестирования сети инженеры сообщают, что сигнал беспроводной сети периодически заглушается какими-то помехами. Каковы две возможные причины искажения сигнала? (Выберите два варианта.)
возвышенность, на которой расположен офис, где была развернута беспроводная сеть
+сотовые телефоны, используемые сотрудниками
+количество беспроводных устройств, используемых в данной беспроводной сети
микроволновая печь
большое количество деревьев вокруг офиса
———
Инженер пытается создать виртуальные машины на компьютере, но хочет убедиться, что физические ресурсы системы, используемые виртуальными машинами, будут находиться под их непосредственным управлением, а не под управлением операционной системы сервера виртуальных машин. Как добиться этого?
+Настроить виртуальные машины с помощью гипервизора, работающего непосредственно с оборудованием.
Настроить виртуальные машины в качестве Windows Virtual PC.
Отключить гиперпоточность в BIOS.
Ограничить емкость оперативной памяти со страничной организацией.
Настроить виртуальные машины с помощью размещенного гипервизора.
———
Инженера просят настроить один жесткий диск для поддержки двух операционных систем и хранения файлов данных в трех отдельных местоположениях диска. Какие настройки разделов поддерживают эти требования?
1 основной, 3 активных, 1 расширенный, 2 логических
+2 основных, 1 активный, 1 расширенный, 3 логических
3 основных, 1 активный, 2 расширенных
2 логических, 2 активных, 3 расширенных
——-
Инженер должен задокументировать текущие настройки всех сетевых устройств в колледже, включая устройства, расположенные на прилегающих территориях. Какой протокол лучше всего использовать для защищенного доступа к сетевым устройствам?
Telnet
FTP
HTTP
+SSH
————
В чем заключаются типичные обязанности инженера первого уровня в центре обработки вызовов?
решение проблемы, предусматривающее вскрытие корпуса компьютера
формирование и передача заказа-наряда на уровень выше и звонок клиенту для получения дополнительной информации
использование ПО удаленного доступа для устранения неисправностей компьютера клиента
+сбор информации при обращении клиента на помощью
——
Каким образом по DSL одновременно передаются телефонные сигналы и сигналы данных?
Каждый сигнал передается на своей частоте.
В DSL для передачи телефонного трафика и трафика данных используются цифровые сигналы.
Каждое подключение осуществляется отдельно.
В DSL используется низкочастотная передача.
————
Каким образом по DSL одновременно передаются телефонные сигналы и сигналы данных?
+Каждый сигнал передается на своей частоте.
В DSL для передачи телефонного трафика и трафика данных используются цифровые сигналы.
Каждое подключение осуществляется отдельно.
В DSL используется низкочастотная передача.
——-
Какая функция характерна для команды ntbackup?
Она может использоваться для восстановления файлов.
+Она используется для создания точек восстановления.
Она используется для создания копии реестра.
Она может запускаться из пакетного файла.
——
Какой режим обеспечения безопасности беспроводных подключений на основании открытых стандартов обеспечивает максимальную защиту?
WPA
LEAP
+WPA2
WEP
——-
В каких условиях требуется сетевой компьютерный кабель типа «витая пара» для прокладки в пленум-полостях?
если требуемая длина кабеля составляет более 91 м
если кабель подключается к главному распределительному отсеку (англ. MDF)
+если кабель прокладывается в межпотолочном пространстве
если кабель устанавливается в монтажный блок в коммутационном шкафу
———-
Пользователь сообщает, что некоторые задания на печать не были напечатаны. Инженер проверяет и замечает, что эти задания застряли в очереди печати. Что следует сделать, чтобы решить эту проблему?
Подключить принтер к регулятору напряжения.
+Отменить задание, отображающее ошибку, которое не дает напечатать другие задания.
Переустановить драйвер принтера.
Отключить кабель данных от принтера и снова подключить его.
———
Какой файл используется для обнаружения и создания информации об аппаратных устройствах, установленных на ноутбук с ОС Windows XP в процессе загрузки?
+NTDETECT.COM
NTLDR
BOOT.INI
NTOSKRNL.EXE
——
Близкого расположения с каким типом оборудования следует избегать при прокладке медных сетевых кабелей во избежание электромагнитных помех?
устройства беспроводной сети
+электродвигатели
беспроводные телефоны
микроволновые печи
——
Клиент расстроен и хочет поговорить с конкретным инженером для немедленного решения проблемы. Этого инженера не будет в офисе еще час. Каков правильный способ обработки этого вызова?
Проигнорировать просьбу клиента и попытаться, с помощью пошагового процесса решения проблемы, перенаправить внимание клиента и решить проблему.
Отослать рассерженного клиента к руководителю.
Сообщить клиенту, что нужного ему инженера в настоящее время нет в офисе, и настоять на том, чтобы попытаться решить проблему без него.
+Предложить клиенту либо попытаться решить проблему немедленно, либо подождать, пока нужный ему инженер не перезвонит ему в течение двух часов.
——
В каких обстоятельствах инженер первого уровня должен передать заказ-наряд на уровень выше?
если инженер не может понять проблему из объяснений клиента
если клиент запрашивает определенного инженера
если клиент оказывается очень осведомленным в технических вопросах
+если для решения проблемы требуется опыт другого инженера
——
Согласно корпоративной политике безопасности, для обмена данными через удаленные соединения используются защищенные туннели. Какая технология шифрования обеспечивает безопасность данных при их передаче по общедоступной сети Интернет, как если бы они передавались по корпоративной локальной сети?
WPA
WEP
VPN
+MD5
———
Какие две операционные системы используются на мобильных устройствах? (Выберите два варианта.)
+IOS
+Android
Apple
Google
MobileOS
——
В ходе аудита было обнаружено, что файлы компании, хранившиеся на персональном сервере бывшего сотрудника, были изменены после того, как этот сотрудник ушел из компании. Что следует сделать для предотвращения несанкционированного доступа к этим файлам в будущем, но так, чтобы другие сотрудники компании могли их использовать?
Удалить учетную запись бывшего сотрудника.
Удалить файлы с сервера.
+Изменить тип учетной записи на гостевой.
Отключить учетную запись бывшего сотрудника.
————
В чем заключается причина отключения широковещательной рассылки имени сети (SSID) и изменение имени сети по умолчанию на беспроводной точке доступа?
Точка доступа прекращает широковещательную рассылку собственного MAC-адреса, предотвращая подключение к сети неавторизованных беспроводных клиентов.
Отключение широковещательной рассылки имени сети освобождает радиочастотный диапазон и увеличивает скорость передачи данных точки доступа.
+Любой пользователь с именем сети по умолчанию может осуществить доступ к точке доступа и изменить ее настройку.
Для подключения к беспроводной сети необходимо вручную настроить имя сети на беспроводных клиентах.
———-
Что из перечисленного ниже является наиболее точным описанием угрозы подмены?
отправка ненормально большого объема данных на удаленный сервер, что не позволяет пользователям осуществлять доступ к службам сервера
создание впечатления, что данные исходят из источника, который на самом деле не является таковым
+перехват трафика между двумя узлами или добавление ложной информации в трафик между двумя узлами
отправка массовой рассылки отдельным пользователям, спискам или доменам с целью нарушения работы электронной почты
——
Инженер пытается устранить неисправность компьютера с 4-летним сроком эксплуатации, который слишком долго загружается, и выясняет, что при каждой загрузке BIOS выполняет обнаружение оборудования. Какое действие поможет решить данную проблему?
+Замена батареи CMOS.
Запуск диспетчера устройств для обнаружения нового оборудования.
Запуск компьютера с помощью последней удачной конфигурации.
Сброс BIOS с помощью перемычки CMOS.
————
От какого критерия питания зависит число внутренних накопителей, установленных на компьютере?
выходное напряжение +5 В постоянного тока
выходное напряжение +20 В постоянного тока
напряжение источника питания
выходное напряжение постоянного тока
входное напряжение переменного тока
+мощность источника питания
———
Каким образом инженер должен проверить все функции системы после подтверждения удаления вируса с компьютера?
Задокументировать проблему и процедуры, выполненные для ее решения.
+Проверить наличие новейших исправлений и обновлений ОС.
Собрать информацию из нескольких источников для четкого определения проблемы.
Поговорить с пользователем для определения причины проблемы.
——
Какая функция материнской платы контролирует количество данных, передаваемых ЦП за один раз?
постоянное запоминающее устройство
корпус с матричным расположением штырьковых выводов
+внешняя шина
инструкции MMX
——
Какой тип атаки на систему безопасности используется, когда хакер звонит в компанию, чтобы получить данные для входа в систему компьютера, представляясь сотрудником?
социотехника
троянская программа
шпионское ПО
рекламное ПО
+фишинг
——
Инженер объясняет клиенту разницу между струйными и лазерными принтерами. Какие два сравнения ему следует использовать? (Выберите два варианта.)
+Струйные принтеры являются менее дорогостоящими в качестве первоначальной покупки по сравнению с лазерными.
В струйных принтерах используется обычная бумага для обеспечения низкой стоимости печати, а в лазерных — более дорогая термобумага.
И лазерный, и струйный принтеры обеспечивают низкое качество изображения.
+Результаты печати лазерного принтера будут сухими, а результаты печати струйного могут быть все еще влажными из-за использования чернил.
Лазерный принтер работает значительно медленнее по сравнению со струйным.
——
Для чего в ноутбуках используются приемы пропускания тактов ЦП?
+для сокращения возможного тепловыделения ЦП
для обеспечения пиковой скорости работы ЦП
для увеличения производительности ЦП
для сохранения заряда аккумулятора путем снижения скорости шины между ЦП и ОЗУ
——
Какие три действия должны выполняться в рамках программы текущего профилактического обслуживания компьютера? (Выберите три варианта).
+удаление неиспользуемых или ненужных программ
увеличение емкости ОЗУ компьютера
+установка необходимых обновлений средств обеспечения безопасности
изменение параметров обозревателя
удаление старой электронной почты
+удаление пыли из входных отверстий вентиляторов, источника питания и периферийных устройств
——
Текущая настройка IP в небольшой компании выполняется вручную и занимает много времени. Из-за увеличения роста сети инженер должен упростить способ настройки IP-адресов рабочих станций. Какая служба поможет упростить задачу настройки IP-адресов рабочих станций?
DHCP
DIPS
ICMP
+APIPA
——
Назовите четыре уровня в эталонной модели TCP/IP.
HTTP, TCP, IP, Ethernet
+прикладной, транспортный, Интернета, сетевого доступа
прикладной, канала данных, сетевой, транспортный
TCP, IP, Ethernet, IEEE
прикладной, представления, сеансовый, транспортный
——-
Какие два действия следует выполнить инженеру службы поддержки при оказании помощи клиентам? (Выберите два варианта.)
Почувствовав какие-либо признаки раздражения клиента, передать его вызов на уровень выше.
Перебить клиентов, если они начнут решать свои собственные проблемы.
+Позволить клиентам закончить объяснение, не задавая дополнительных вопросов.
+Успокоить клиентов, сводя к минимуму их проблемы.
При необходимости поставить звонок клиента на удержание, попросить у клиента разрешения на это.
———
Инженер выполняет обслуживание лазерного принтера. К каким двум деталям принтера не следует прикасаться, поскольку они сохраняют высокое напряжение даже после отключения от источника питания?
+кондиционирующий вал
картридж с тонером
+печатающая головка
провод коротрона
лоток для бумаги
——
Инженер работает над устранением неисправностей компьютера, который не выполняет печать. Инженер предполагает, что драйвер принтера мог устареть, загружает новейший драйвер и устанавливает его. Инженер пытается выполнить печать, но компьютер по-прежнему не печатает. Какое следующее действие инженеру следует выполнить?
Разработать план действий.
Проверить теорию.
Выявить неисправность.
+Разработать новую теорию.
———
Инженер использует функцию сжатия тома служебной программы управления дисками и выполняет разделение раздела. Что следует сделать дальше, чтобы раздел можно было использовать?
Удалить все разделы и выполнить повторную инициализацию диска.
+Создать раздел(ы) в незанятом пространстве.
Преобразовать незанятое пространство в динамический диск.
Форматировать существующий раздел.
———-
Инженер использует функцию сжатия тома служебной программы управления дисками и выполняет разделение раздела. Что следует сделать дальше, чтобы раздел можно было использовать?
Удалить все разделы и выполнить повторную инициализацию диска.
+Создать раздел(ы) в незанятом пространстве.
Преобразовать незанятое пространство в динамический диск.
Форматировать существующий раздел.
————
Какое утверждение содержит правильное сравнение характеристик коаксиального кабеля и кабеля типа «витая пара»?
+Ограниченная пропускная способность коаксиального кабеля делает его более пригодным для использования в локальной сети, чем кабель типа «витая пара».
Из-за наличия одной медной жилы проще устранить неисправность коаксиального кабеля, чем кабеля типа «витая пара».
Коаксиальный кабель дешевле кабеля типа «витая пара».
Физическая установка коаксиального кабеля сложнее установки кабеля типа «неэкранированная витая пара».
—-
Пользователь обновляет драйвер устройства и перезагружает систему. После перезагрузки пользователь успешно выполняет вход в систему, после чего ОС отображает синий экран и происходит сбой. Пользователь нажимает клавишу F8 при перезагрузке и пытается выполнить вход с последней удачной конфигурацией, но получает тот же результат. Почему последняя удачная конфигурация не помогла решить проблему?
Пользователю не удалось запустить chkdsk перед входом в систему.
Файл boot.ini поврежден.
+При успешном входе в систему последняя удачная конфигурация заменяется на текущую.
Пользователю не удалось сохранить параметры CMOS при перезагрузке.
—
Пользователь загружает виджет на телефон Android, однако с удивлением замечает, что в результате прикосновения к виджету загружается приложение. В чем может быть причина этой проблемы?
+Виджет поврежден.
Настройки безопасности ОС Android нарушены.
Виджет связан с приложением, и такое поведение является нормальным.
Пользователь загрузил вирус.
——
Компьютерный инженер выполнил ряд действий для решения проблемы. Некоторые действия не помогли решить проблему, но в конце концов решение было найдено. Какие действия должны быть задокументированы?
только правильное решение, поскольку оно помогло устранить проблему
+все, что было сделано в попытке решить проблему
описание проблемы и ее решения
только неправильные действия, что поможет инженерам не совершать подобных ошибок в будущем
——
Что представляет %USERPROFILE% в пути C:Users%USERPROFILE%AppDataLocalTemp?
местоположение папки «Документы» конкретного пользователя
переменную, установленную администратором для каждого пользователя системы
+переменную среды, установленную операционной системой
фиксированное значение, которое обозначает уровень доступа пользователя к системным файлам
——
Пользователю нужно обновить компоненты ноутбука для увеличения производительности. Какие два компонента пользователь может заменить самостоятельно? (Выберите два варианта.)
+аккумулятор
ЖК-дисплей
ЦП
+ОЗУ
материнскую плату
——
Какое утверждение справедливо для модулей ОЗУ DDR2 и DDR3?
Они обладают разным числом контактов.
+Для них используются различные типы гнезд DIMM на материнской плате.
Для них требуется одинаковая рабочая частота на внешней шине.
Они работают при одинаковом напряжении.
——
Заказчику требуется дополнительная емкость системы хранения на старом компьютере. Что инженеру следует проверить на компьютере, чтобы определить возможность добавления жесткого диска?
генерируемое тепло и требования к вентиляции
версию BIOS
открытое гнездо расширения PCI/PCIe
адекватную емкость ОЗУ
+доступное подключение PATA/SATA
——
Какие две потенциальные угрозы для мобильного устройства связаны с такими действиями, как обеспечение доступа с правами «root» и взлом защиты устройства? (Выберите два варианта.)
Повышение производительности устройства.
+Модифицированная ОС не может надлежащим образом создавать или поддерживать функции организации изолированной среды.
Интерфейс пользователя может быть модифицирован в значительной степени.
Включение некоторых функций, изначально отключенных поставщиком.
+Модифицированная ОС предоставляет пользователям доступ к корневому каталогу.
——
Какие два типа интерфейса позволяют подключать различные внешние компоненты к ноутбукам и настольным ПК без необходимости отключать питание компьютера? (Выберите два варианта.)
PCI
PS/2
PCIe
+USB
+FireWire
——
Инженер планирует обновление операционной системы пользовательского компьютера, в настоящее время работающего под управлением ОС Windows Vista. Поскольку клиенту требуется функция BitLocker, встроенная в ОС Windows Vista, необходимо, чтобы после установки новой операционной системы эта функция оставалась доступна. Какая версия или версии ОС Windows 7 поддерживают эту функцию?
Windows 7 Максимальная, Профессиональная, Домашняя расширенная и Начальная
+Windows 7 Максимальная
Windows 7 Максимальная и Профессиональная
Windows 7 Максимальная, Профессиональная и Домашняя расширенная
—-
Какие три признака NTFS делают эту файловую систему лучше, чем FAT32? (Выберите три варианта).
+шифрование на уровне файлов и папок
размер файла на том 4,17 миллиона
максимальный размер отдельного файла 4 Гбайта
+журналирование
большой размер кластера
параметры разрешений для файлов и для папок
——
Пользователь считает, что файл данных на компьютере с ОС Windows XP поврежден. Какая служебная программа может предоставить максимум информации об этом файле данных?
Msconfig
Regedit
Defrag
+Chkdsk
——
Какие факторы необходимо проверить при выборе и установке нескольких вентиляторов охлаждения в корпусе ПК?
+Установка с правильным направлением воздушного потока.
Одинаковость марки и модели.
Одинаковая скорость работы.
Одинаковая мощность обдува.
——
Какая функция сенсорного экрана мобильного устройства позволит пользователю выполнять масштабирование отображаемых объектов, таких как карты и фотографии?
скольжение
длительное касание
сжатие
+двойное касание
——
Какие две процедуры следует выполнить перед профилактическим обслуживанием ноутбука? (Выберите два варианта.)
+Отключить адаптер питания переменного тока.
Подключить устройства, которые обычно используются в ежедневной работе.
Убедиться, что используется новейшая версия BIOS.
+Извлечь аккумулятор.
Проверить, что были установлены последние обновления операционной системы.
Проверить, что все драйверы являются текущими.
——
Какой метод двухфакторной идентификации требует использования небольшого радиопередающего устройства и ввода пароля для успешной аутентификации?
электронная ключ-карта
+ключ-брелок
смарт-ключ
биометрический считыватель
—-
Инженеру требуется настроить гарнитуру Bluetooth для пользователя компьютера. Какие два действия следует выполнить перед установкой головной гарнитуры? (Выберите два варианта.)
Извлечь аккумулятор.
+Убедиться, что включен переключатель Bluetooth ноутбука.
+Убедиться, что к неокрашенной части ноутбука прикреплен антистатический браслет.
Отключить питание переменного тока.
Включить Bluetooth в настройке параметров BIOS.
——
Компьютер может осуществлять доступ к устройствам, расположенным в той же сети, но не может осуществлять доступ к устройствам в других сетях. В чем состоит вероятная причина этой проблемы?
Кабель неправильно подключен к сетевой плате.
Компьютер имеет недопустимый IP-адрес.
+Компьютер имеет недопустимый адрес шлюза по умолчанию.
Компьютер имеет неправильную маску подсети.
——
После того, как администратор вручную настроил правильное имя сети (SSID) на новом ноутбуке, компьютер все равно не может подключиться к беспроводной сети. Какое дополнительное действие следует выполнить для решения этой проблемы?
Проверить наличие MAC-адреса ноутбука в таблице фильтрации MAC-адресов.
+Перезагрузить беспроводную точку доступа.
Изменить групповую учетную запись пользователя, включив все разрешения для файлов.
Переименовать ноутбук и сбросить пароль пользователя в сети.
——
Раздраженный клиент звонит с жалобой о том, что запланированное обслуживание компьютера заняло больше времени, чем ожидалось. Инженер проверяет заказ-наряд и замечает, что обслуживание выполнялось новым сотрудником. Что инженеру следует ответить?
Убедиться, что теперь компьютер работает нормально.
Объяснить, что для выполнения обслуживания был отправлен неопытный инженер по ремонту.
Поставить звонок на удержание до появления руководителя.
+Выслушать жалобу и извиниться за любые неудобства, доставленные слишком продолжительным обслуживанием компьютера.
——
Инженер выполняет устранение неисправностей принтера, который не печатает из-за постоянного замятия бумаги. Что инженер должен попытаться сделать в первую очередь?
Проверить наличие согнутых штифтов на кабеле принтера.
Проверить подключение кабелей принтера.
Настроить порт принтера.
+Очистить принтер.
——
Какой компонент ноутбука преобразует постоянный ток в переменный, обеспечивая подсветку дисплея?
аккумулятор
+инвертер
подсветка
материнская плата
флуоресцентная лампа с холодным катодом (англ. CCFL)
——
Стало известно, что на компьютерах компании появляются окна с предупреждениями лжеантивирусного ПО. Администратор компьютерных систем составляет уведомление для всех сотрудников с объяснением способов решения этой проблемы. Помимо описания проблемы и рекомендуемой процедуры ее решения, какие два указания также должны быть включены в уведомление? (Выберите два варианта.)
+Не щелкайте никакую точку окна с предупреждением.
Чтобы закрыть окно, нажмите кнопку Отмена в окне.
+Чтобы закрыть окно, используйте сочетание клавиш Alt + F4.
Обновите программное обеспечение для защиты от вредоносного ПО, установленное на компьютере.
Закройте окно, нажав кнопку X в верхнем правом углу.
—-
Какое утверждение об использовании антистатического браслета является верным?
+Антистатический браслет не следует носить при ремонте источника питания.
Для оптимального заземления зажим должен быть присоединен к окрашенной части корпуса компьютера.
Антистатический браслет не следует использовать вместе с антистатическим ковриком.
Металлическая часть браслета не должна соприкасаться с кожей.
——
Согласно политике профилактического обслуживания компании, каждые полгода для каждого компьютера должна создаваться новая точка восстановления. Какие существуют способы создания этой точки восстановления?
Выбрать Пуск > Панель управления > Стандартные > Служебные > Восстановление системы > Создание точки восстановления.
В интерфейсе командной строки ввести restore /cn.
Правой кнопкой мыши щелкнуть Мой компьютер и выбрать Свойства > Восстановление > Создание точки восстановления.
+Выбрать Пуск > Программы > Стандартные > Служебные > Восстановление системы > Создание точки восстановления.
New Version:
How to find: Press “Ctrl + F” in the browser and fill in whatever wording is in the question to find that question/answer. If the question is not here, find it in Questions Bank.
NOTE: If you have the new question on this test, please comment Question and Multiple-Choice list in form below this article. We will update answers for you in the shortest time. Thank you! We truly value your contribution to the website.
1. The network administrator wants to configure a switch to pass VLAN update information to other switches in the domain but not update its own local VLAN database. Which two steps should the administrator perform to achieve this? (Choose two.)
- Reset the VTP counters.
- Configure the switch with the same VTP domain name as other switches in the network.
- Configure the VTP mode of the switch to transparent.
- Configure VTP version 1 on the switch.
- Verify that the switch has a higher configuration revision number.
Besides the VTP domain name and mode needing to be configured, the switch must connect to other switches in the same VTP domain through a trunk in order to transmit/receive VTP information.
2. Which statement describes the Autonomous System number that is used in EIGRP?
- It identifies the priority of the networks to be included in update packets.
- It defines the reliability of the EIGRP routing protocol.
- It is associated with the global Autonomous System number that is assigned by IANA.
- It specifies the EIGRP routing process on a router.
The AS number identifies the EIGRP routing process, and multiple AS numbers can be configured on a router to facilitate multiple EIGRP processes running on a network. The AS number is not associated with the global Autonomous System number that is assigned by IANA, because EIGRP is an interior gateway protocol. The reliability of EIGRP and the priority of networks that are included in updates are not linked to AS numbers.
3. Refer to the exhibit. Which switch will be the root bridge after the election process is complete?
- S1
- S2
- S3
- S4
The root bridge is determined by the lowest bridge ID, which consists of the priority value and the MAC address. Because the priority values of all of the switches are identical, the MAC address is used to determine the root bridge. Because S2 has the lowest MAC address, S2 becomes the root bridge.
4. Refer to the exhibit. A network administrator is configuring PVST+ for the three switches. What will be a result of entering these commands?
- S1 will set the priority value for VLAN 20 to 24596.
- S2 will set the priority value for VLAN 10 to 24576.
- S1 will set the priority value for VLAN 10 to 0.
- S3 will set the priority value for VLAN 30 to 8192.
In PVST+ configuration, the spanning-tree vlan vlan-id root primary global configuration mode command will set the priority for the switch to the predefined value of 24,576 or to the highest multiple of 4,096, less than the lowest bridge priority detected on the network. The spanning-tree vlan vlan-id root secondary global configuration mode command will set the priority for the switch to the predefined value of 28,672. Because S1 is configured with the priority value of 12,288 for VLAN 30, S3 has to be configured with the priority value of 8,192 (highest multiple of 4,096 but lower than 12,288) to become the root bridge for VLAN 30.
5. By default, how often does a Cisco switch that is using RSTP send out BPDU frames?
- every 2 seconds
- every 4 seconds
- every 5 seconds
- every 10 seconds
6. Refer to the exhibit. Why did R1 and R2 not establish an adjacency?
- The IPv4 address of Fa0/0 interface of R1 has a wrong IP address.
- The AS number does not match on R1 and R2.
- The automatic summarization is enabled on R1 and R2.
- There is no network command for the network 192.168.1.0/24 on R1.
To establish adjacency, both routers must be configured with the same AS number. The network 192.168.0.0 .0.0.255.255 command issued on R1 includes all networks from 192.168.0.0 to 192.168.255.255. Therefore, the network 192.168.1.0/24 is also included.
7. What address type will OSPFv3 use to form adjacencies to neighboring routers?
- the all OSPF router multicast
- the link-local address of the interface
- the all-link router multicast
- the global unicast of the interface
OSPF neighbor adjacencies are formed using the link-local address of the interfaces that are connecting to neighboring routers.
8. Which OSPF LSA type is only used in multiaccess and NBMA networks?
- type 1
- type 2
- type 3
- type 4
OSPF type 2 LSAs are only flooded on multiaccess and NBMA networks where a designated router is elected. The type 2 LSA is created by the designated router and advertises the router ID of the designated router to other OSPF routers.
9. Which dynamic routing protocol uses hop count to calculate metric value?
- EIGRP
- IS-IS
- OSPF
- RIP
Different routing protocols uses different metrics to calculate the best path through the routed network. RIP uses hop count, EIGRP uses bandwidth and delay, and OSPF uses cost.
10. What is the default percentage of interface bandwidth that EIGRP is allowed to use for exchanging EIGRP messages?
- 50%
- 10%
- 25%
- 100%
By default, EIGRP is able to use up to 50 percent of the bandwidth on an interface for EIGRP messages.
11. How does implementing STP allow for a scalable network design?
- It prevents local traffic from propagating to other parts of the network.
- It eliminates Layer 2 loops from redundant links.
- It filters broadcasts and other undesirable traffic from the network.
- It provides failover services when duplicate network equipment is used.
Spanning Tree Protocol (STP) supports the design of a scalable network by preventing Layer 2 loops where redundant switch paths are implemented.
12. Refer to the exhibit. Which address will R1 use as the source address for all OSPFv3 messages that will be sent to neighbors?
- FF02::5
- FE80::1
- 2001:DB8:ACAD:A::1
- FF02::1
All OSPFv3 messages are sourced from the link-local IPv6 address of an interface. Link local addresses use the prefix FE80::/10.
13. Which wildcard mask would be used to advertise the 192.168.5.96/27 network as part of an OSPF configuration?
- 0.0.0.32
- 0.0.0.31
- 255.255.255.224
- 255.255.255.223
The wildcard mask can be found by subtracting the subnet mask from 255.255.255.255.
14. Refer to the exhibit. A network administrator has configured OSPFv2 on the two Cisco routers as shown. The routers are unable to form a neighbor adjacency. What should be done to fix the problem?
- Add the command network 192.168.30.0 0.0.0.255 area 0 on router R1.
- Change the IP address on S0/0 of router R2 to 192.168.20.2.
- Remove the FastEthernet0/0 passive interface configuration on router R1.
- Add the command network 192.168.20.1 0.0.0.0 area 0 on router R1.
In order to form OSPFv2 neighbor adjacencies, two connected router interfaces must share the same subnet. Router R2 is shown in the topology with an IP address of 192.168.20.5 and does not exist on the same subnet as the 192.168.20.1 /30 IP address of S0/0 on router R1.
15. What is one reason to use the ip ospf priority command when the OSPF routing protocol is in use?
- to activate the OSPF neighboring processto
- streamline and speed up the convergence process
- to influence the DR/BDR election process
- to provide a backdoor for connectivity during the convergence process
The OSPF priority can be set to a number between 0 and 255. The higher the number set, the more likely the router becomes the DR. A priority 0 stops a router from participating in the election process and the router does not become a DR or a BDR.
16. Refer to the exhibit. A Layer 3 switch routes for three VLANs and connects to a router for Internet connectivity. Which two configurations would be applied to the switch? (Choose two.)
- (config)# ip routing
- (config)# interface fastethernet0/4
(config-if)# switchport mode trunk - (config)# interface vlan 1
(config-if)# ip address 192.168.1.2 255.255.255.0
(config-if)# no shutdown - (config)# interface gigabitethernet 1/1
(config-if)# no switchport
(config-if)# ip address 192.168.1.2 255.255.255.252 - (config)# interface gigabitethernet1/1
(config-if)# switchport mode trunk
The no switchport command allows a switch port to be assigned an IP address. The port is a routed port at that point. The ip routing command enables routing for a switch. Use the interface vlan x command on the switch to configure routing for any VLAN that is attached to the switch, including the management VLAN. No management VLAN is shown in this scenario, but the commands interface vlan 5 and interface vlan 6, along with an appropriate IP address and subnet mask for each VLAN, would be used on the switch in the exhibit. There is no need to add an IP address or use the no shutdown command on VLAN 1 because VLAN 1 is not used in this design and because VLAN 1 is “up and up” by default.
17. Refer to the exhibit. A network administrator has issued the show ip eigrp neighbors command. What can be concluded from the output?
- An EIGRP neighbor with IP address 10.10.10.14 is connected to R1 via serial interface 0/1/0.
- There is no incoming EIGRP message at this moment.
- The first EIGRP neighbor R1 learned about has the IP address 10.10.10.2.
- If R1 does not receive a Hello packet in 4 seconds from the neighbor with IP 10.10.10.18, it will declare the neighbor is down.
With the show ip eigrp neighbors command, the output includes:
H column – Lists the neighbors in the order that they were learned.
Address – IPv4 address of the neighbor.
Interface – Local interface on which this Hello packet was received.
Hold – Current hold time. When a Hello packet is received, this value is reset to the maximum hold time for that interface, and then counts down to zero. If zero is reached, the neighbor is considered down.
Queue Count – Should always be zero. If more than zero, then EIGRP packets wait to be sent.
In the output shown, the neighbor router with IP 10.10.10.2 was the first neighbor learned by router R1.
18. Refer to the exhibit. Which command will configure unequal-cost load balancing with EIGRP on the HQ router?
- maximum-paths 1
- maximum-paths 2
- variance 2
- variance 1
The maximum-paths command is used to configure equal-cost load balancing with EIGRP. The variance command is used to configure unequal-cost load balancing, but the default variance is 1. If the variance is set to 1, only routes with the same metric as the successor are installed in the local routing table. So, to configure unequal-cost load balancing, the variance 2 command should be used.
19. Refer to the exhibit. Based on the command output shown, what is the status of the EtherChannel?
- The EtherChannel is down as evidenced by the protocol field being empty.
- The EtherChannel is in use and functional as indicated by the SU and P flags in the command output.
- The EtherChannel is partially functional as indicated by the P flags for the FastEthernet ports.
- The EtherChannel is dynamic and is using ports Fa0/10 and Fa0/11 as passive ports.
The command output shows the port channel as SU, which means Layer 2 and in use; and the FastEthernet 0/10 and 0/11 interfaces are bundled in port-channel as indicated by the P flag. Configuring the EtherChannel using the channel-group 1 mode on command will cause the Protocol field in the command output to be empty.
20. Which function is provided by EtherChannel?
- enabling traffic from multiple VLANs to travel over a single Layer 2 link
- creating one logical link by using multiple physical links between two LAN switches
- dividing the bandwidth of a single link into separate time slots
- spreading traffic across multiple physical WAN links
EtherChannel technology allows the grouping, or aggregating, of several Fast Ethernet or Gigabit switch ports into one logical channel.
21. Which OSPFv3 function works differently from OSPFv2?
- election process
- metric calculation
- authentication
- hello mechanism
- OSPF packet types
Both versions of OSPF use the same five basic packet types, the cost metric, and the DR/BDR election process. Hello packets are used in both versions to build adjacencies. OSPFv3, however, uses advanced encryption and authentication features that are provided by IPsec, while OSPFv2 uses either plain text or MD5 authentication.
22. What are two requirements to be able to configure an EtherChannel between two switches? (Choose two.)
- All interfaces need to be assigned to different VLANs.
- Different allowed ranges of VLANs must exist on each end.
- The interfaces that are involved need to be contiguous on the switch.
- All the interfaces need to be working in the same duplex mode.
- All the interfaces need to work at the same speed.
All interfaces in the EtherChannel bundle must be assigned to the same VLAN or be configured as a trunk. If the allowed range of VLANs is not the same, the interfaces do not form an EtherChannel even when set to auto or desirable mode.
23. On what type of OSPF router is interarea route summarization configured?
- intra-area routers
- ASBRs
- ABRs
- backbone routers
Interarea summarization is manually configured on Area Border Routers (ABRs). Because ABRs connect multiple areas, it is these routers that would summarize routes before injecting them into another area. ASBRs are configured with external route summarization. Backbone and intra-area routers have all interfaces in a single area and are not able to summarize routes into other areas.
24. Which three steps should be taken before moving a Cisco switch to a new VTP management domain? (Choose three.)
- Configure the switch with the name of the new management domain.
- Reset the VTP counters to allow the switch to synchronize with the other switches in the domain.
- Select the correct VTP mode and version.
- Download the VTP database from the VTP server in the new domain.
- Reboot the switch.
- Configure the VTP server in the domain to recognize the BID of the new switch.
When adding a new switch to a VTP domain, it is critical to configure the switch with a new domain name, the correct VTP mode, VTP version number, and password. A switch with a higher revision number can propagate invalid VLANs and erase valid VLANs thus preventing connectivity for multiple devices on the valid VLANs.
25. Which two commands are used in the implementation of a dynamic IPv4 routing protocol? (Choose two.)
- lineip route
- network
- router
- interface
In order to implement RIP, EIGRP, or OSPF, configuration begins by typing router protocol. An example would be router ospf 1. In IPv4, network statements are added for each directly connected network that is participating in the dynamic routing protocol. An example would be network 192.168.10.0 0.0.0.255 area 0.
26. What is the reason for a network engineer to alter the default reference bandwidth parameter when configuring OSPF?
- to force that specific link to be used in the destination route
- to more accurately reflect the cost of links greater than 100 Mb/s
- to enable the link for OSPF routing
- to increase the speed of the link
By default, Fast Ethernet, Gigabit, and 10 Gigabit Ethernet interfaces all have a cost of 1. Altering the default reference bandwidth alters the cost calculation, allowing each speed to be more accurately reflected in the cost.
27. Which technology is an open protocol standard that allows switches to automatically bundle physical ports into a single logical link?
- LACP
- PAgP
- DTP
- Multilink PPP
LACP, or Link Aggregation Control Protocol, is defined by IEEE 802.3ad and is an open standard protocol. LACP allows switches to automatically bundle switch ports into a single logical link to increase bandwidth. PAgP, or Port Aggregation Protocol, performs a similar function, but it is a Cisco proprietary protocol. DTP is Dynamic Trunking Protocol and is used to automatically and dynamically build trunks between switches. Multilink PPP is used to load-balance PPP traffic across multiple serial interfaces.
28. Refer to the exhibit. The partial configuration that is shown was used to configure router on a stick for VLANS 10, 30, and 50. However, testing shows that there are some connectivity problems between the VLANs. Which configuration error is causing this problem?
- There is no IP address configured for the FastEthernet 0/0 interface.
- The wrong VLAN has been configured on subinterface Fa0/0.50.
- A configuration for the native VLAN is missing.
- The VLAN IP addresses should belong to the same subnet.
According to the configuration shown, the router was configured to use the wrong VLAN (500 instead of 50) on subinterface Fa0/0.50. This will prevent devices that are configured on VLAN 50 from communicating with subinterface Fa0/0.50. When configuring subinterfaces, the Fa0/0 interface has to be configured with no IP address, and each subinterface has to be assigned to a different subnet.
29. Refer to the exhibit. A network administrator issues the show ip protocols command. Based on the exhibited output, what can be concluded?
- The EIGRP K values are default values.
- R1 receives routes to the network 192.168.1.0/24 and 10.0.0.0/24.
- Up to 4 routes of different metric values to the same destination network will be included in the routing table.
- The no auto-summary command is not applied for the EIGRP operation.
The output indicates that the K values are in default (K1=1, K2=0, K3=1, K4=0, K5=0). The no auto-summary command is used since automatic summarization is not in effect. R1 is advertising the 192.168.1.0 and 10.0.0.0 networks, not receiving advertisements about them. Up to 4 equal metric paths to the same destination network will be included in the routing table since the metric variance parameter is set to 1.
30. Which two statements are characteristics of routed ports on a multilayer switch? (Choose two.)
- In a switched network, they are mostly configured between switches at the core and distribution layers.
- They are not associated with a particular VLAN.
- The interface vlan command has to be entered to create a VLAN on routed ports.
- They are used for point-to-multipoint links.
- They support subinterfaces, like interfaces on the Cisco IOS routers.
Routed ports are physical ports that act similarly to a router interface. They are not associated with a particular VLAN, they do not support subinterfaces, and they are used for point-to-point links. In a switched network, they are mostly configured between switches at the core and distribution layers. To configure routed ports, the no switchport interface command has to be used on the appropriate ports.
31. Which action should be taken when planning for redundancy on a hierarchical network design?
- Implement STP PortFast between the switches on the network.
- Immediately replace a nonfunctioning module, service, or device on a network.
- Purchase backup equipment for every network device at the distribution layer.
- Add alternate physical paths for data to traverse the network.
One method of implementing redundancy is path redundancy, which means installing alternate physical paths for data to traverse the network. Redundant links in a switched network support high availability and can be used for load balancing, thus reducing congestion on the network.
32. Refer to the exhibit. Suppose that routers B, C, and D have a default priority, and router A has a priority 0. Which conclusion can be drawn from the DR/BDR election process?
- Router A will become the DR and router D will become the BDR.
- If the priority of router C is changed to 255, then it will become the DR.
- If the DR fails, the new DR will be router B.
- If a new router with a higher priority is added to this network, it will become the DR.
If the priority is set to 0, the router is not capable of becoming the DR, so router A cannot be the DR. OSPF DR and BDR elections are not preemptive. If a new router with a higher priority or higher router ID is added to the network after the DR and BDR election, the newly added router does not take over the DR or the BDR role.
33. A network administrator is troubleshooting the EIGRP routing between two routers, R1 and R2. The problem is found to be that only some, but not all networks attached to R1 are listed in the routing table of router R2. What should the administrator investigate on router R1 to determine the cause of the problem?
- Do the network commands include all the networks to be advertised?
- Does the hello interval setting match the hello interval on R2?
- Does the AS number match the AS number on R2?
- Is the interface connected to R2 configured as a passive interface?
The fact that some networks appear in the routing table of R2 indicates that there is basic EIGRP communication between R1 and R2. This excludes the possibility of AS number mismatch and the interface between R1 and R2 being passive. Hello interval timers between EIGRP routers do not have to match. The administrator needs to make sure that the network commands cover all networks attached to R1 that should be advertised.
34. Where does EIGRP maintain the list of feasible successors?
- the routing table
- the neighbor table
- the topology table
- the link-state database
EIGRP maintains a topology table that contains all of the routes learned from EIGRP neighbors. The routes will include successors and feasible successors.
35. Refer to the exhibit. On which router or routers would a default route be statically configured in a corporate environment that uses single area OSPF as the routing protocol?
- ISP
- R0-A
- ISP and R0-A
- R0-A, R0-B, and R0-C
- R0-B and R0-C
- ISP, R0-A, R0-B, and R0-C
The default route is applied to the router that connects to the Internet, or R0-A. R0-A then distributes that default route using the OSPF routing protocol.
36. Refer to the exhibit. What will Router1 do if it receives packets that are destined to network 172.16.4.0/24?
- forward the packets to the gateway of last resort
- drop the packets
- send the packets to network 0.0.0.0
- send the packets out interface GigabitEthernet 0/0
In this example Router1 does not have a specific route to the172.16.4.0/24 network. Because the 172.16.4.0/24 network falls within the 172.16.0.0/18 summary network route to Null0, this route will be chosen. As a consequence, Router1 will drop the packets destined for the 172.16.4.0/24network. The reason for Router1 not using the default route is that the Null0 route has a longer matching network mask.
37. In a large enterprise network, which two functions are performed by routers at the distribution layer? (Choose two.)
- connect users to the network
- provide a high-speed network backbone
- connect remote networks
- provide Power over Ethernet to devices
- provide data traffic security
In a large enterprise network, the provision of a high-speed network backbone is a function of the core layer. Access layer switches connect users to the network and provide Power over Ethernet to devices. Distribution layer routers provide data traffic security and connections to other networks.
38. Which two metric weights are set to one by default when costs in EIGRP are being calculated? (Choose two.)
- k6
- k4
- k2
- k1
- k5
- k3
By default, k1 and k3 are set to one and k2, k4, and k5 are set to zero during cost calculation by the EIGRP process. There is no k6 value.
39. Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.
Which message was displayed on the web server?
- Work done!
- Congratulations!
- You’ve made it!
- Wonderful work!
The three routers R1, R2 and R3 implement EIGRP as the routing protocol. There are two discontiguous networks with no connectivity between them. Automatic summarization is enabled by default on routers R1 and R2, and this is causing a routing problem between discontiguous networks. The solution is to issue the no auto-summary command on each router:
R1(config)# router eigrp 100
R1(conf-router)# no auto-summary
R2(config)# router eigrp 100
R2(conf-router)# no auto-summary
After these commands are issued, PC1 is able to access the web server and the message displayed is “You’ve made it!”.
40. An administrator is troubleshooting an adjacency issue between two OSPFv3 routers. Which two neighbor states indicate a stable adjacency between the routers? (Choose two.)
- 2way
- full
- loading
- exstart
- exchange
The full and 2way states are two stable OSPF adjacency types.
41. What is the function of ASICs in a multilayer switch??
- They prevent Layer 2 loops by disabling redundant links between switches.
- They provide power to devices such as IP phones and wireless access points through Ethernet ports.
- They streamline forwarding of IP packets in a multilayer switch by bypassing the CPU.
- They aggregate multiple physical switch ports into a single logical port.
ASICs are application-specific integrated circuits and they allow a multilayer switch to forward IP packets without calling on the CPU to make routing decisions. By using ASICs a switch can forward IP packets almost as fast as it can forward Layer 2 frames.
42. Which two VTP modes allow for the creation, modification, and deletion of VLANs on the local switch? (Choose two.)
- client
- server
- slave
- master
- distribution
- transparent
The three VTP modes are server, client, and transparent. In server VTP mode, the switch can create, modify, and delete VLANs and send this information on to other switches that are in the same VTP domain. Switches in transparent VTP mode can do the same except that information is not transmitted to other switches.
43. Which is a link-state routing protocol?
- OSPF
- EIGRP
- BGP
- RIP
IS-IS is a link state IGP routing protocol that supports classless routing. It is commonly used by ISPs and carriers.
44. Refer to the exhibit. The routing table on R2 does not include all networks that are attached to R1. The network administrator verifies that the network statement is configured to include these two networks. What is a possible cause of the issue?
- The AS number does not match between R1 and R2.
- The network statements should include the wild card mask.
- The interfaces that are connected to these two networks are configured as passive interfaces.
- The no auto-summary command is missing in the R1 configuration.
The fact that R2 has a route to 172.18.100.0 from R1 indicates that EIGRP is functioning, which excludes the issue of an AS number not matching. The issue is that both sides have a network within the Class B 172.16.0.0/16 network. Therefore, automatic network summarization must be disabled by the no auto-summary command. If this command is not used, the network statement with a wild card mask will not have effect. The passive interface, if configured, will prevent EIGRP updates from entering the two networks, but not prevent R1 from advertising them to R2.
45. Which type of OSPF LSA represents an external route and is propagated across the entire OSPF domain?
- type 1
- type 2
- type 3
- type 4
- type 5
Type 5 LSAs are used for external routes and are generated by an ASBR. They are forwarded into other areas by ABRs.
46. Refer to the exhibit. What are three results for the DR and BDR elections for the given topologies? (Choose three.)
- R3 is DR for segment A.
- R3 is BDR for segment A.
- R2 is BDR for segment A.
- R1 is DR for segment A.
- R5 is BDR for segment B.
- R4 is DR for segment B.
Without ties between them, the elections took place based only on interface priorities.
47. Refer to the exhibit. What can be concluded about network 192.168.1.0 in the R2 routing table?
- This network was learned through summary LSAs from an ABR.
- This network is directly connected to the interface GigabitEthernet0/0.
- This network should be used to forward traffic toward external networks.
- This network has been learned from an internal router within the same area.
n a routing table, the designation O IA means the entry was learned from an interarea LSA that was generated from an ABR. The C label indicates a network that is directly connected to an interface on the router. The O label indicates a network that is advertised by another router in the same area. The label O*E2 indicates an external network. In this case, the network designation of 0.0.0.0/0 indicates that this external network is the default route for all traffic that is destined for external networks.
48. Refer to the exhibit. A network administrator has connected two switches together using EtherChannel technology. If STP is running, what will be the end result?
- The resulting loop will create a broadcast storm.
- STP will block one of the redundant links.
- The switches will load balance and utilize both EtherChannels to forward packets.
- Both port channels will shutdown.
Cisco switches support two protocols for negotiating a channel between two switches: LACP and PAgP. PAgP is Cisco-proprietary. In the topology shown, the switches are connected to each other using redundant links. By default, STP is enabled on switch devices. STP will block redundant links to prevent loops.
49. What are two reasons to implement passive interfaces in the EIGRP configuration of a Cisco router? (Choose two.)
- to provide increased network security
- to exclude interfaces from load balancingto shut down unused interfaces
- to mitigate attacks coming from the interfaces
- to avoid unnecessary update traffic
Two primary reasons for implementing passive interfaces in EIGRP routing are to suppress unnecessary update traffic, such as when an interface is a LAN interface with no other routers connected, and to increase security controls, such as preventing unknown rogue routing devices from receiving EIGRP updates.
50. Which model and which two characteristics would be more likely to be considered in purchasing an access layer switch, as compared to buying switches that operate at the other layers of the Cisco hierarchical design model? (Choose three.)
- Catalyst 4500X
- EtherChannel
- PoE
- Catalyst 2960
- number of ports
- RSTP
Access layer switches are cheaper and do not have as many ports or features as the switches that work at the distribution or core layers. The number of ports that are needed depends on the number of wired devices in the area. Access layer switches tend to be fixed configuration switches that have a set number of ports. Ports on access layer switches tend to operate at 100 or 1000 Mb/s. Switches that operate at all three design layers are capable of EtherChannel and RSTP. The Catalyst 4500X model switch is used at the core design layer.
51. What is the order of packet types used by an OSPF router to establish convergence?
- LSU, LSAck, Hello, DBD, LSR
- Hello, DBD, LSR, LSU, LSAck
- Hello, LSAck, LSU, LSR, DBD
- LSAck, Hello, DBD, LSU, LSR
An OSPF router progresses in this order to convergence, using the following packets:
1. Hello packet, used for OSPF election and establishing neighbor adjacencies
2. DBD packet, used to synchronize databases with neighbors
3. LSR packet, used to request more information in synchronizing databases
4. LSU packet, used to send link-state updates to neighbors
5. LSAck packet, used to acknowledge receipt of an LSU
52. What two STP features are incorporated into Rapid PVST+? (Choose two.)
- BackboneFast
- loop guard
- BPDU filter
- UplinkFast
- BPDU guard
- PortFast
Because Rapid PVST+ is a Cisco enhancement of RSTP, it will support PortFast, BPDU guard, BPDU filter, root guard, and loop guard. Uplink fast and Backbone fast are incorporated into the protocol.
53. Which feature of the EIGRP routing protocol can provide fast re-convergence without DUAL recomputation in the event of a route failure?
- having a route in the passive state
- having a feasible successor route
- having a route in the active state
- having a successor route
EIGRP avoids DUAL recomputation of routes whenever possible by maintaining a list of backup routes (feasible successors) in the topology table already determined to be loop-free. If the primary route (the successor route, which is in the passive state) in the routing table fails, the best backup route is immediately added to the routing table. A route in the active state is in the process of being recomputed by DUAL.
54. What is the function of STP in a scalable network?
- It combines multiple switch trunk links to act as one logical link for increased bandwidth.
- It decreases the size of the failure domain to contain the impact of failures.
- It protects the edge of the enterprise network from malicious activity.
- It disables redundant paths to eliminate Layer 2 loops.
STP is an important component in a scalable network because it allows redundant physical connections between Layer 2 devices to be implemented without creating Layer 2 loops. STP prevents Layer 2 loops from forming by disabling interfaces on Layer 2 devices when they would create a loop.
55. As the network administrator you have been asked to implement EtherChannel on the corporate network. What does this configuration consist of?
- providing redundant devices to allow traffic to flow in the event of device failure
- grouping two devices to share a virtual IP address
- providing redundant links that dynamically block or forward traffic
- grouping multiple physical ports to increase bandwidth between two switches
EtherChannel is utilized on a network to increase speed capabilities by grouping multiple physical ports into one or more logical EtherChannel links between two switches. STP is used to provide redundant links that dynamically block or forward traffic between switches. FHRPs are used to group physical devices to provide traffic flow in the event of failure.
56. Refer to the exhibit. If the switch has been configured for PVST+ mode, what command output would replace the question marks?
- ieee
- pvst+
- pvst
- rstp
Even though PVST+ mode is Cisco proprietary, the command output shows as ieee. In Rapid-PVST mode, the command output shows as simply rstp.
57. Refer to the exhibit. An administrator attempts to configure EIGRP for IPv6 on a router and receives the error message that is shown. Which command must be issued by the administrator before EIGRP for IPv6 can be configured?
- ipv6 unicast-routing
- eigrp router-id 100.100.100.100
- ipv6 eigrp 100
- no shutdown
- ipv6 cef
Before EIGRP for IPv6 can be configured on a router, routing for IPv6 must be configured. This is accomplished by issuing the global configuration command ipv6 unicast-routing.
58. For troubleshooting missing EIGRP routes on a router, what three types of information can be collected using the show ip protocols command? (Choose three.)
- any ACLs that are affecting the EIGRP routing process
- any interfaces that are enabled for EIGRP authentication
- the local interface that is used to establish an adjacency with EIGRP neighbors
- the IP addresses that are configured on adjacent routers
- networks that are unadvertised by the EIGRP routing protocol
- any interfaces on the router that are configured as passive
The show ip protocols command verifies whether automatic summarization is being used on the local router, whether any interfaces on the local router are configured as passive interfaces, whether a network is not advertised to EIGRP neighbors, and whether any ACLs are applied to EIGRP.
59. In which IOS CLI mode must a network administrator issue the maximum-paths command to configure load balancing in EIGRP?
- router configuration mode
- privileged mode
- interface configuration mode
- global configuration mode
The maximum-paths command must be issued in the router configuration mode to load balance up to 32 routes.
60. A network engineer is configuring a LAN with a redundant first hop to make better use of the available network resources. Which protocol should the engineer implement?
- GLBP
- HSRP
- VRRP
- FHRP
Gateway Load Balancing Protocol (GLBP) provides load sharing between a group of redundant routers while also protecting data traffic from a failed router or circuit.
61. Match the step sequence to the multiarea OSPF route calculation process. (Not all options are used.)
62. Match the switched LAN problem to the correct symptom. (Not all options are used.)
63. Match the port state with its condition. (Not all options are used.)
- The port does not participate in spanning tree and does not forward frames. –> disabled
- The port receives BPDU frames but does not forward frames. –> blocking
- The port prepares to participate in frame forwarding and begins to populate the MAC address table. –> learning
- The port receives BPDU frames and transmits its own BPDU frames in preparing to participate in the active topology. –> (none)
Older Version:
64. Which technological factor determines the impact of a failure domain?
- the number of layers of the hierarchical network
- the number of users on the access layer
- the role of the malfunctioning device
- the forwarding rate of the switches used on the access layer
65. Which routing protocol is able to scale for large networks and utilizes non-backbone areas for expansion?
- EIGRP
- BGP
- OSPF
- RIPv2
66. What are two reasons to install a single 48-port fixed configuration switch, rather than two 24-port fixed configuration switches, in a wiring closet that supports two classrooms? (Choose two.)
- more power provided to each port
- more ports available for end devices
- higher uplink speeds
- reduced power and space requirements
- reduced number of VLANs/broadcast domains
67. In the Cisco hierarchical design model, which layer is more likely to have a fixed configuration switch than the other layers?
- distribution
- transport
- internet
- access
- core
68. What are two requirements when using out-of-band configuration of a Cisco IOS network device? (Choose two.)
- HTTP access to the device
- a terminal emulation client
- Telnet or SSH access to the device
- a direct connection to the console or AUX port
- a connection to an operational network interface on the device
Explanation: A connection to an operational network interface on the device, and Telnet, SSH, or HTTP access are required for in-band management of Cisco IOS networking devices.
69. Which port role is assigned to the switch port that has the lowest cost to reach the root bridge?
- root port
- non-designated port
- designated port
- disabled port
70. Refer to the exhibit. A network administrator is verifying the bridge ID and the status of this switch in the STP election. Which statement is correct based on the command output?
- The bridge priority of Switch_2 has been lowered to a predefined value to become the root bridge.
- The bridge priority of Switch_2 has been lowered to a predefined value to become the backup root bridge.
- The STP instance on Switch_2 is failing due to no ports being blocked and all switches believing they are the root.
- The STP instance on Switch_2 is using the default STP priority and the election is based on Switch_2 MAC address.
71. When the show spanning-tree vlan 33 command is issued on a switch, three ports are shown in the forwarding state. In which two port roles could these interfaces function while in the forwarding state? (Choose two.)
- disabled
- designated
- root
- alternate
- blocked
72. A network administrator is analyzing first-hop router redundancy protocols. What is a characteristic of VRRPv3?
- VRRPv3 is Cisco proprietary.
- It supports IPv6 and IPv4 addressing.
- It works together with HSRP.
- It allows load balancing between routers.
Explanation: VRRPv3 is a non-proprietary, first-hop router redundancy protocol. It provides features for both IPv4 and IPv6 addressing. HSRP and GLBP are both Cisco-proprietary protocols. GLBP provides load balancing between a group of redundant routers.
73. Refer to the exhibit. Which switching technology would allow data to be transmitted over each access layer switch link and prevent the port from being blocked by spanning tree due to the redundant link?
- EtherChannel
- HSRP
- PortFast
- trunking
74. A network administrator has configured an EtherChannel between two switches that are connected via four trunk links. If the physical interface for one of the trunk links changes to a down state, what happens to the EtherChannel?
- The EtherChannel will transition to a down state.
- Spanning Tree Protocol will recalculate the remaining trunk links.
- The EtherChannel will remain functional.
- Spanning Tree Protocol will transition the failed physical interface into forwarding mode.
75. What are two advantages of EtherChannel? (Choose two.)
- Configuring the EtherChannel interface provides consistency in the configuration of the physical links.
- Load balancing occurs between links configured as different EtherChannels.
- EtherChannel uses upgraded physical links to provide increased bandwidth.
- Spanning Tree Protocol views the physical links in an EtherChannel as one logical connection.
- Spanning Tree Protocol ensures redundancy by transitioning failed interfaces in an EtherChannel to a forwarding state.
76. When a range of ports is being configured for EtherChannel, which mode will configure LACP on a port only if the port receives LACP packets from another device?
- active
- auto
- desirable
- passive
Explanation: The command channel-group mode active enables LACP unconditionally, and the command channel-group mode passive enables LACP only if the port receives an LACP packet from another device. The command channel-group mode desirable enables PAgP unconditionally, and the command channel-group mode auto enables PAgP only if the port receives a PAgP packet from another device.
77. Which two parameters must match on the ports of two switches to create a PAgP EtherChannel between the switches? (Choose two.)
- MAC address
- speed
- VLAN information
- PAgP mode
- port ID
78. When EtherChannel is configured, which mode will force an interface into a port channel without exchanging aggregation protocol packets?
- active
- auto
- on
- desirable
79. Which IOS 12.4 software package integrates full features, including voice, security, and VPN capabilities, for all routing protocols?
- Advanced Security
- Advanced IP Services
- Advanced Enterprise Services
- Service Provider Services
80. What is the major release number in the IOS image name c1900-universalk9-mz.SPA.152-3.T.bin?
- 2
- 3
- 15
- 52
- 1900
81. Which statement describes a difference between the IOS 15.0 extended maintenance release and a standard maintenance release?
- They consist of two separate parallel trains.
- The extended maintenance release will deliver new IOS features as soon as they are available.
- The standard maintenance release enables faster IOS feature delivery than the extended maintenance release does.
- A new standard maintenance release will synchronize with the latest extended maintenance release before the extended is made available.
82. When a router is powered on, where will the router first search for a valid IOS image to load by default?
- RAM
- ROM
- flash memory
- NVRAM
83. A network engineer is upgrading the Cisco IOS image on a 2900 series ISR. What command could the engineer use to verify the total amount of flash memory as well as how much flash memory is currently available?
- show flash0:
- show version
- show interfaces
- show startup-config
84. A network administrator configures a router with the command sequence:R1(config)# boot system tftp://c1900-universalk9-mz.SPA.152-4.M3.bin
R1(config)# boot system rom
What is the effect of the command sequence?
- On next reboot, the router will load the IOS image from ROM.
- The router will copy the IOS image from the TFTP server and then reboot the system.
- The router will load IOS from the TFTP server. If the image fails to load, it will load the IOS image from ROM.
- The router will search and load a valid IOS image in the sequence of flash, TFTP, and ROM.
85. Beginning with the Cisco IOS Software Release 15.0, which license is a prerequisite for installing additional technology pack licenses?
- IPBase
- DATA
- UC
- SEC
86. Which three software packages are available for Cisco IOS Release 15.0?
- DATA
- IPVoice
- Security
- Enterprise Services
- Unified Communications
- Advanced IP Services
87. When a customer purchases a Cisco IOS 15.0 software package, what serves as the receipt for that customer and is used to obtain the license as well?
- Software Claim Certificate
- End User License Agreement
- Unique Device Identifier
- Product Activation Key
88. Which command would a network engineer use to find the unique device identifier of a Cisco router?
- show version
- show license udi
- show running-configuration
- license install stored-location-url
89. A newly hired network engineer wants to use a 2911 router from storage. What command would the technician use to verify which IOS technology licenses have been activated on the router?
- show flash0:
- show interfaces
- show license
- show startup-config
- show version
90. Which command is used to configure a one-time acceptance of the EULA for all Cisco IOS software packages and features?
- license save
- show license
- license boot module module-name
- license accept end user agreement
91. How long is the evaluation license period for Cisco IOS Release 15.0 software packages?
- 15 days
- 30 days
- 60 days
- 180 days
92. What is the purpose of a T train release in Cisco IOS 15?
- It is used for long-term maintenance, enabling customers to qualify, deploy, and remain on the release for an extended period.
- It provides regular bug fix maintenance rebuilds, plus critical fix support for network-affecting bugs.
- It provides premium packages and enables additional IOS software feature combinations that address more complex network requirements.
- It specifies advanced IP services features such as advanced security and service provider packages.
93. What code in the Cisco IOS 15 image filename c1900-universalk9-mz.SPA.153-3.M.bin indicates that the file is digitally signed by Cisco?
- SPA
- universalk9
- M
- mz
94. A network technician is troubleshooting problems with a router that is running IOS 15. Which command will display the features activated for the licenses that are installed on the router?
- show flash0:
- show license
- show startup-config
- show version
95. Which wireless network topology would be used by network engineers to provide a wireless network for an entire college building?
- ad hoc
- hotspot
- infrastructure
- mixed mode
96. In wireless networks what is a disadvantage of using mixed mode on an AP?
- Only 802.11n wireless NICs can attach to the AP.
- Devices must be closer to the AP due to the limited distance range.
- The wireless network operates slower if one device uses an older standard wireless NIC.
- No encryption can be used by the AP or by the wireless NIC that is attached to the AP.
97. When would a network engineer configure an access point with channel bonding?
- when security is an issue
- when more throughput is needed
- when older wireless NICs are being used
- when trunking is enabled between the access point and switch
98. Which method of wireless authentication is currently considered to be the strongest?
- WEP
- WPA
- WPA2
- open
- shared key
Explanation: WPA2 can use the AES encryption standard, which is currently the strongest method of encrypting wireless data.
99. What is a wireless security mode that requires a RADIUS server to authenticate wireless users?
- enterprise
- personal
- shared key
- WEP
100. A laptop cannot connect to a wireless access point. Which two troubleshooting steps should be taken first? (Choose two.)
- Ensure that the wireless NIC is enabled.
- Ensure that the laptop antenna is attached.
- Ensure that the wireless SSID is chosen.
- Ensure that the correct network media is selected.
- Ensure that the NIC is configured for the proper frequency.
101. A network engineer is troubleshooting a newly deployed wireless network that is using the latest 802.11 standards. When users access high bandwidth services such as streaming video, the wireless network performance is poor. To improve performance the network engineer decides to configure a 5 Ghz frequency band SSID and train users to use that SSID for streaming media services. Why might this solution improve the wireless network performance for that type of service?
- The 5 GHz band has a greater range and is therefore likely to be interference-free.
- Requiring the users to switch to the 5 GHz band for streaming media is inconvenient and will result in fewer users accessing these services.
- The 5 GHz band has more channels and is less crowded than the 2.4 GHz band, which makes it more suited to streaming multimedia.
- The only users that can switch to the 5 GHz band will be those with the latest wireless NICs, which will reduce usage.
102. Refer to the exhibit. How did this router learn of the highlighted route in the routing table?
- by entering the router configuration mode command default-information originate
- by entering the global configuration mode command ip route 0.0.0.0 0.0.0.0 interface-type interface-number
- by entering the global configuration mode command ip route 0.0.0.0 0.0.0.0 ip-address
- by receiving an update from another OSPF router that is running another routing protocol
- by receiving an update from another OSPF router that has the default-information originate command configured
Explanation: On the router that connects to the Internet, a default route (quad zero route) is normally entered as well as the default-information originate command. As a result of this configuration, other OSPF routers receive the default route and install it into the routing table as an external route.
103. Refer to the exhibit. What are two consequences of issuing the displayed commands? (Choose two.)
- The routing update information is protected against being falsified.
- The routing table of R2 will be secured.
- The key is encrypted with the MD5 hashing algorithm.
- OSPF routes will get priority over EIGRP routes going into the routing table.
- The overhead of OSPF information exchange will reduce.
104. What does an OSPF area contain?
- routers that share the same router ID
- routers whose SPF trees are identical
- routers that have the same link-state information in their LSDBs
- routers that share the same process ID
105. Refer to the exhibit. Why are some of the entries marked O IA?
- They correspond to entries that are learned from other areas.
- They correspond to entries that are learned from other routing protocols.
- They represent summary routes that are internal to the area.
- They are default routes that are learned from other routing protocols.
106. In which mode is the area area-id range address mask command issued when multiarea OSPF summarization is being configured?
- global configuration mode
- router configuration mode
- interface configuration mode of area 0 interfaces
- interface configuration mode of all participating interfaces
107. Refer to the exhibit. What two pieces of information could be determined by a network administrator from this output? (Choose two.)
- R1 is participating in multiarea OSPF.
- The OSPF process number that is being used is 0.
- Interface Fa0/1 is not participating in the OSPF process.
- R1 is the distribution point for the routers that are attached to the 10.0.0.4 network.
- The metric that will be installed in the routing table for the 10.0.0.0 route will be 65 (64+1).
108. Refer to the exhibit. Two routers have been configured to use EIGRP. Packets are not being forwarded between the two routers. What could be the problem?
- EIGRP does not support VLSM.
- The routers were not configured to monitor neighbor adjacency changes.
- The default bandwidth was used on the routers.
- An incorrect IP address was configured on a router interface.
109. Which command can be issued on a router to display information about the successors and feasible successors for a destination network when EIGRP is used as the routing protocol?
- show ip protocols
- show ip eigrp topology
- show ip eigrp interfaces
- show ip eigrp neighbors
110. A network administrator is configuring the authentication for EIGRP routing. The administrator enters these commands:R1(config)# key chain THE_KEY
R1(config-keychain)# key 1
R1(config-keychain-key)# key-string key123What is the next step necessary to enable the authentication for EIGRP routing?
- Configure the priority of authentication algorithms to be used.
- Configure the authentication on all interfaces that are participating in EIGRP.
- Configure an ACL to identify the networks that are participating in EIGRP.
- Configure the authentication in the router eigrp as-number configuration mode.
111. What are three characteristics of the Cisco IOS Software Release 12.4T train? (Choose three.)
- It requires the activation of a license.
- It has a number of embedded technology packages.
- It is updated with new features and hardware support.
- It is derived from the Cisco IOS Software Release 12.4 Mainline train.
- It has extended maintenance new feature releases approximately every 16 to 20 months.
- It receives regular software fixes that are synchronized with the 12.4 Mainline train.
112. If a company wants to upgrade a Cisco 2800 router from IOS 12.4T, what IOS should be recommended for a stable router platform?
- 12.5T
- 13.1T
- 14.0
- 15.1M
113. A router has been removed from the network for maintenance. A new Cisco IOS software image has been successfully downloaded to a server and copied into the flash of the router. What should be done before placing the router back into service?
- Back up the new image.
- Copy the running configuration to NVRAM.
- Delete the previous version of the Cisco IOS software from flash.
- Restart the router and verify that the new image starts successfully.
114. Which step supports disaster recovery and should be performed first when upgrading an IOS system image on a Cisco router?
- Delete the current image from flash memory.
- Copy the current image from the router to a TFTP server.
- Use the boot system command to configure the router to load the new image.
- Configure the router to load the new image from the TFTP server.
115. Refer to the exhibit. A network engineer is preparing to upgrade the IOS system image on a Cisco 2901 router. Based on the output shown, how much space is available for the new image?
- 25574400 bytes
- 249856000 bytes
- 221896413 bytes
- 33591768 bytes
116. The customer of a networking company requires VPN connectivity for workers who must travel frequently. To support the VPN server, the customer router must be upgraded to a new Cisco IOS software version with the Advanced IP Services feature set. What should the field engineer do before copying the new IOS to the router?
- Set the router to load the new IOS image file directly from the TFTP server on the next reboot.
- Delete the currently installed IOS by using the erase flash: command, and reload the router.
- Issue the show running-configuration command to determine the features of the currently installed IOS image file.
- Issue the show version and the show flash commands to ensure that the router has enough memory and file space to support the new IOS image.
117. Match each OSPF LSA description with its type. (Not all options are used.)
118. Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.Why are users in the OSPF network not able to access the Internet?
- The default route is not redistributed correctly from router R1 by OSPF.
- The interface that is connected to the ISP router is down.
- The OSPF network statements are misconfigured on routers R2 and R3.
- The OSPF timers that are configured on routers R1, R2, and R3 are not compatible.
- The network statement is misconfigured on router R1.
119. Which command will start the process to bundle two physical interfaces to create an EtherChannel group via LACP?
- channel-group 2 mode auto
- interface port-channel 2
- channel-group 1 mode desirable
- interface range GigabitEthernet 0/4 – 5
120. What statement describes a Cisco IOS image with the “universalk9_npe” designation for Cisco ISR G2 routers?
- It is an IOS version that, at the request of some countries, removes any strong cryptographic functionality.
- It is an IOS version that provides only the IPBase feature set.
- It is an IOS version that offers all of the Cisco IOS Software feature sets.
- t is an IOS version that can only be used in the United States of America.
121. Fill in the blank. Do not use abbreviations.
The license ” install” flash0:seck9-C1900-SPE150_K9-FAB12340099.xml command will restore the specified saved Cisco IOS Release 15 license to a router.
122. Refer to the exhibit. Match the components of the IOS image name to their description. (Not all options are used.)
Place the options in the following order:
specifying the feature set -> universalk9
minor release number -> 1
where the image runs and if the file is compressed -> mz
platform on which the image runs -> c1900
– not scored –
maintanence release and rebuild number -> M4
new feature release number -> 4
file extension -> bin
major release number -> 15
123. Match the description to the Cisco IOS category. (Not all options apply.)
Place the options in the following order:
technology train
[+] branches from another train
[+] has the latest features
mainline train
[#] possibly is 12.4
[#] contains mostly bug fixes
124. Refer to the exhibit. 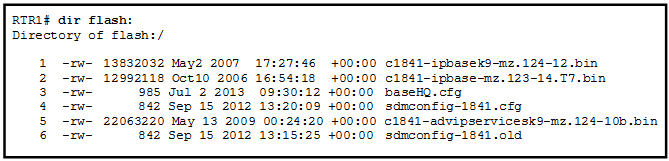
- The router selects the second Cisco IOS image because it is the smallest IOS image.
- The router selects an image depending on the boot system command in the configuration.
- The router selects the third Cisco IOS image because it contains the advipservicesk9 image.
- The router selects the third Cisco IOS image because it is the most recent IOS image.
- The router selects an image depending on the value of the configuration register.
125. In addition to IPBase, what are the three technology packs that are shipped within the universal Cisco IOS Software Release 15 image? (Choose three.)
- Advanced IP Services
- SP Services
- Unified Communications
- Security
- DATA
126. Which two conditions should the network administrator verify before attempting to upgrade a Cisco IOS image using a TFTP server? (Choose two.)
- Verify the name of the TFTP server using the show hosts command.
- Verify that the TFTP server is running using the tftpdnld command.
- Verify that the checksum for the image is valid using the show version command.
- Verify connectivity between the router and TFTP server using the ping command.
- Verify that there is enough flash memory for the new Cisco IOS image using the show flash command.
127. Which three images are considered premium software packages for Cisco IOS Release 12.4? (Choose three.)
- IP Voice
- Enterprise Base
- Advanced Security
- Enterprise Services
- Advanced IP Services
- Advanced Enterprise Services
128. What are two reasons to enable OSPF routing protocol authentication on a network? (Choose two.)
- to prevent data traffic from being redirected and then discarded
- to ensure faster network convergence
- to provide data security through encryption
- to prevent redirection of data traffic to an insecure link
- to ensure more efficient routing
The reason to configure OSPF authentication is to mitigate against routing protocol attacks like redirection of data traffic to an insecure link, and redirection of data traffic to discard it. OSPF authentication does not provide faster network convergence, more efficient routing, or encryption of data traffic.
129. While attending a conference, participants are using laptops for network connectivity. When a guest speaker attempts to connect to the network, the laptop fails to display any available wireless networks. The access point must be operating in which mode?
- active
- passive
- mixed
- open
130. What is the purpose of issuing the ip ospf message-digest-key key md5 password command and the area area-id authentication message-digest command on a router?
- to facilitate the establishment of neighbor adjacencies
- to encrypt OSPF routing updates
- to enable OSPF MD5 authentication on a per-interface basis
- to configure OSPF MD5 authentication globally on the router
131. Refer to the exhibit. Which destination MAC address is used when frames are sent from the workstation to the default gateway?
- MAC addresses of both the forwarding and standby routers
- MAC address of the forwarding router
- MAC address of the standby router
- MAC address of the virtual router
132. A network technician is attempting to upgrade an IOS system image on a Cisco 1941 router. Which command should the technician issue to verify the presence of sufficient free space in flash for the new image on the router that is being upgraded?
- show file system
- show flash0:
- show running-config
- show version
133. Which statement describes a characteristic of a Cisco Enterprise Architecture module?
- Server Farm and Data Center Module are submodules of the Enterprise Edge module.
- The Enterprise Campus only consists of the core layer of the campus infrastructure.
- The Enterprise Edge consists of the Internet, VPN, and WAN modules connecting the enterprise with the service provider’s network.
- The Service Provider Edge provides QoS, policy reinforcement, service levels, and security.
134. Match the step number to the sequence of stages that occur during the HSRP failover process. (Not all options are used.)
Last Updated on May 20, 2021 by
Cisco CCNA 1 ITN v6.0 final Exam Answers Routing and Switching (R&S) Introduction to Networks (ITN) (Version 6.00) collection year 2017, 2018 and 2019 Full 100%. CCNA 1 has been know as ITN. The following are the questions exam answers. Guarantee Passed 100%. CCNA 1 v6.0 final exam answers has some new update from the old version 5.1. You can review all final Exam Answers. You will get passed scored 100% with this version 6.0. Good Luck for Cisco Netacad ITN v6.0 Exam!
Noted: There are 3 forms of Final Exam. In this page we have collected all 3 forms. You will random from these question which 55 to 60 questions.
-
Recommend
From year to year, Cisco has updated many versions with difference questions. The latest version is version 6.0 in 2018. What is your version? It depends on your instructor creating your class. We recommend you to go thought all version if you are not clear. While you take online test with netacad.com, You may get random questions from all version. Each version have 1 to 10 different questions or more. After you review all questions, You should practice with our online test system by go to «Online Test» link below.
| Version 5.02 | Version 5.1 | Version 6.0 | Online Assessment |
| Final Exam | Final Exam | Final Exam | Online A, Online B, Online C |
| CCNA2 Pretest Exam | |||
| Pretest Exam | Pretest Exam | Pretest Exam | Online Test |
March, 2019 New Update for CCNA 1 v6.0 Final Exam
-
What is an example of a top-level domain?
- www.cisco.com
- cisco.com
- .com
- root.cisco.com
Explanation:
Top-level domains represent a country or type of organization, such as .com or .edu.
-
What is a characteristic of multicast messages?
- They are sent to a select group of hosts.
- They are sent to all hosts on a network.
- They must be acknowledged.
- They are sent to a single destination.
Explanation:
Multicast is a one-to-many type of communication. Multicast messages are addressed to a specific multicast group.
-
A network technician suspects that a particular network connection between two Cisco switches is having a duplex mismatch. Which command would the technician use to see the Layer 1 and Layer 2 details of a switch port?
- show interfaces
- show running-config
- show ip interface brief
- show mac-address-table
Explanation:
The show interfaces command can be used on both routers and switches to see speed, duplex, media type, MAC address, port type, and other Layer 1/Layer 2-related information.
-
Where are Cisco IOS debug output messages sent by default?
- memory buffers
- vty lines
- Syslog server
- console line
Explanation:
Debug messages, like other IOS log messages, are sent to the console line by default. Sending these messages to the terminal lines requires the terminal monitor command.
-
Which command can an administrator issue on a Cisco router to send debug messages to the vty lines?
- terminal monitor
- logging console
- logging buffered
- logging synchronous
Explanation:
Debug messages, like other IOS log messages, are sent to the console line by default. Sending these messages to the terminal lines requires the terminal monitor command.
-
What is one indication that a Windows computer did not receive an IPv4 address from a DHCP server?
- The computer cannot ping 127.0.0.1.
- Windows displays a DHCP timeout message.
- The computer receives an IP address that starts with 169.254.
- The computer cannot ping other devices on the same network with IP addresses in the 169.254.0.0/16 range.
Explanation:
When a Windows PC cannot communicate with an IPv4 DHCP server, the computer automatically assigns an IP address in the 169.254.0.0/16 range. Any other device on the same network that receives an address in the same range is reachable.
-
What source IP address does a router use by default when the traceroute command is issued?
- the highest configured IP address on the router
- a loopback IP address
- the IP address of the outbound interface
- the lowest configured IP address on the router
Explanation:
When sending an echo request message, a router will use the IP address of the exit interface as the source IP address. This default behavior can be changed by using an extended ping and specifying a specific source IP address.
-
A user is unable to reach the web site when typing http://www.cisco.com in a web browser, but can reach the same site by typing http://72.163.4.161. What is the issue?
- default gateway
- DHCP
- DNS
- TCP/IP protocol stack
Explanation:
Domain Name Service (DNS) is used to translate a web address to an IP address. The address of the DNS server is provided via DHCP to host computers.
-
What is a characteristic of a fault tolerant network?
- a network that protects confidential information from unauthorized access
- a network that can expand quickly to support new users and applications without impacting the performance of the service delivered to existing users
- a network that supports a mechanism for managing congestion and ensuring reliable delivery of content to all users
- a network that recovers quickly when a failure occurs and depends on redundancy to limit the impact of a failure
Explanation:
Fault tolerant networks limit the impact of a failure because the networks are built in a way that allows for quick recovery when such a failure occurs. These networks depend on multiple or redundant paths between the source and destination of a message.
A scalable network can expand quickly to support new users and applications without impacting the performance of the service being delivered to existing users.
Quality of service (QoS) is a mechanism for managing congestion and ensuring reliable delivery of content to all users.
-
Three bank employees are using the corporate network. The first employee uses a web browser to view a company web page in order to read some announcements. The second employee accesses the corporate database to perform some financial transactions. The third employee participates in an important live audio conference with other corporate managers in branch offices. If QoS is implemented on this network, what will be the priorities from highest to lowest of the different data types?
- audio conference, financial transactions, web page
- financial transactions, web page, audio conference
- audio conference, web page, financial transactions
- financial transactions, audio conference, web page
Explanation:
QoS mechanisms enable the establishment of queue management strategies that enforce priorities for different categories of application data. Thus, this queuing enables voice data to have priority over transaction data, which has priority over web data.
-
What is a benefit of using cloud computing in networking?
- End users have the freedom to use personal tools to access information and communicate across a business network.
- Network capabilities are extended without requiring investment in new infrastructure, personnel, or software.
- Technology is integrated into every-day appliances allowing them to interconnect with other devices, making them more ‘smart’ or automated.
- Home networking uses existing electrical wiring to connect devices to the network wherever there is an electrical outlet, saving the cost of installing data cables.
Explanation:
Cloud computing extends IT’s capabilities without requiring investment in new infrastructure, training new personnel, or licensing new software. These services are available on-demand and delivered economically to any device anywhere in the world without compromising security or function. BYOD is about end users having the freedom to use personal tools to access information and communicate across a business or campus network. Smart home technology is integrated into every-day appliances allowing them to interconnect with other devices, making them more ‘smart’ or automated. Powerline networking is a trend for home networking that uses existing electrical wiring to connect devices to the network wherever there is an electrical outlet, saving the cost of installing data cables.
-
What is the function of the shell in an OS?
- It interacts with the device hardware.
- It interfaces between the users and the kernel.
- It provides dedicated firewall services.
- It provides the intrusion protection services for the device.
Explanation:
Most operating systems contain a shell and a kernel. The kernel interacts with the hardware and the shell interfaces between the kernel and the users.
-
Which connection provides a secure CLI session with encryption to a Cisco switch?
- a console connection
- an AUX connection
- a Telnet connection
- an SSH connection
Explanation:
A CLI session using Secure Shell (SSH) provides enhanced security because SSH supports strong passwords and encryption during the transport of session data. The other methods support authentication but not encryption.
-
A network technician is attempting to configure an interface by entering the following command: SanJose(config)# ip address 192.168.2.1 255.255.255.0. The command is rejected by the device. What is the reason for this?
- The command is being entered from the wrong mode of operation.
- The command syntax is wrong.
- The subnet mask information is incorrect.
- The interface is shutdown and must be enabled before the switch will accept the IP address.
Explanation:
The wrong mode of operation is being used. The CLI prompt indicates that the mode of operation is global configuration. IP addresses must be configured from interface configuration mode, as indicated by the SanJose(config-if)# prompt.
-
An administrator uses the Ctrl-Shift-6 key combination on a switch after issuing the ping command. What is the purpose of using these keystrokes?
- to restart the ping process
- to interrupt the ping process
- to exit to a different configuration mode
- to allow the user to complete the command
Explanation:
To interrupt an IOS process such as ping or traceroute, a user enters the Ctrl-Shift-6 key combination. Tab completes the remainder of parameters or arguments within a command. To exit from configuration mode to privileged mode use the Ctrl-Z keystroke. CTRL-R will redisplay the line just typed, thus making it easier for the user to press Enter and reissue the ping command.
-
Refer to the exhibit. A network administrator is configuring access control to switch SW1. If the administrator uses a console connection to connect to the switch, which password is needed to access user EXEC mode?
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 001 - letmein
- secretin
- lineconin
- linevtyin
Explanation:
Telnet accesses a network device through the virtual interface configured with the line VTY command. The password configured under this is required to access the user EXEC mode. The password configured under the line console 0 command is required to gain entry through the console port, and the enable and enable secret passwords are used to allow entry into the privileged EXEC mode.
-
On which switch interface would an administrator configure an IP address so that the switch can be managed remotely?
- FastEthernet0/1
- VLAN 1
- vty 0
- console 0
Explanation:
Interface VLAN 1 is a virtual interface on a switch, called SVI (switch virtual interface). Configuring an IP address on the default SVI, interface VLAN 1, will allow a switch to be accessed remotely. The VTY line must also be configured to allow remote access, but an IP address cannot be configured on this line.
-
What protocol is responsible for controlling the size of segments and the rate at which segments are exchanged between a web client and a web server?
- TCP
- IP
- HTTP
- Ethernet
Explanation:
TCP is a Layer 4 protocol of the OSI model. TCP has several responsibilities in the network communication process. It divides large messages into smaller segments which are more efficient to send across the network. It also controls the size and rate of segments exchanged between clients and servers.
-
What is an advantage to using a protocol that is defined by an open standard?
- A company can monopolize the market.
- The protocol can only be run on equipment from a specific vendor.
- An open standard protocol is not controlled or regulated by standards organizations.
- It encourages competition and promotes choices.
Explanation:
A monopoly by one company is not a good idea from a user point of view. If a protocol can only be run on one brand, it makes it difficult to have mixed equipment in a network. A proprietary protocol is not free to use. An open standard protocol will in general be implemented by a wide range of vendors.
-
What are two benefits of using a layered network model? (Choose two.)
- It assists in protocol design.
- It speeds up packet delivery.
- It prevents designers from creating their own model.
- It prevents technology in one layer from affecting other layers.
- It ensures a device at one layer can function at the next higher layer.
Explanation:
Some vendors have developed their own reference models and protocols. Today, if a device is to communicate on the Internet, the device must use the TCP/IP model. The benefits of using a layered model are as follows:
- assists in protocol design
- fosters competition between vendors
- prevents a technology that functions at one layer from affecting any other layer
- provides a common language for describing network functionality
- helps in visualizing the interaction between each layer and protocols between each layer
-
Which two OSI model layers have the same functionality as two layers of the TCP/IP model? (Choose two.)
- data link
- network
- physical
- session
- transport
Explanation:
The OSI transport layer is functionally equivalent to the TCP/IP transport layer, and the OSI network layer is equivalent to the TCP/IP internet layer. The OSI data link and physical layers together are equivalent to the TCP/IP network access layer. The OSI session layer (with the presentation layer) is included within the TCP/IP application layer.
-
Which name is assigned to the transport layer PDU?
- bits
- data
- frame
- packet
- segment
Explanation:
Application data is passed down the protocol stack on its way to be transmitted across the network media. During the process, various protocols add information to it at each level. At each stage of the process, a PDU (protocol data unit) has a different name to reflect its new functions. The PDUs are named according to the protocols of the TCP/IP suite:
- Data – The general term for the PDU used at the application layer.
- Segment – transport layer PDU
- Packet – network layer PDU
- Frame – data link layer PDU
- Bits – A physical layer PDU used when physically transmitting data over the medium
-
A network administrator is troubleshooting connectivity issues on a server. Using a tester, the administrator notices that the signals generated by the server NIC are distorted and not usable. In which layer of the OSI model is the error categorized?
- presentation layer
- network layer
- physical layer
- data link layer
Explanation:
The NIC has responsibilities in both Layer 1 and Layer 2. The NIC encodes the frame as a series of signals that are transmitted onto the local media. This is the responsibility of the physical layer of the OSI model. The signal could be in the form of electrical, optical, or radio waves.
-
A network administrator is measuring the transfer of bits across the company backbone for a mission critical financial application. The administrator notices that the network throughput appears lower than the bandwidth expected. Which three factors could influence the differences in throughput? (Choose three.)
- the amount of traffic that is currently crossing the network
- the sophistication of the encapsulation method applied to the data
- the type of traffic that is crossing the network
- the latency that is created by the number of network devices that the data is crossing
- the bandwidth of the WAN connection to the Internet
- the reliability of the gigabit Ethernet infrastructure of the backbone
Explanation:
Throughput usually does not match the specified bandwidth of physical links due to multiple factors. These factors include, the amount of traffic, type of traffic, and latency created by the network devices the data has to cross.
-
What is a characteristic of UTP cabling?
- cancellation
- cladding
- immunity to electrical hazards
- woven copper braid or metallic foil
Explanation:
Cladding and immunization from electrical hazards are characteristics for fiber-optic cabling. A woven copper braid or metallic foil is used as a shield for the inner coaxial cable conductor. Cancellation is a property of UTP cabling where two wires are located adjacent to one another so each magnetic field cancels out the adjacent magnetic field.
-
What are two characteristics of fiber-optic cable? (Choose two.)
- It is not affected by EMI or RFI.
- Each pair of cables is wrapped in metallic foil.
- It combines the technique of cancellation, shielding, and twisting to protect data.
- It typically contains 4 pairs of fiber-optic wires.
- It is more expensive than UTP cabling is.
Explanation:
Fiber-optic cabling supports higher bandwidth than UTP for longer distances. Fiber is immune to EMI and RFI, but costs more, requires more skill to install, and requires more safety precautions.
-
What is a characteristic of the LLC sublayer?
- It provides the logical addressing required that identifies the device.
- It provides delimitation of data according to the physical signaling requirements of the medium.
- It places information in the frame allowing multiple Layer 3 protocols to use the same network interface and media.
- It defines software processes that provide services to the physical layer.
Explanation:
The Logical Link Control (LLC) defines the software processes that provide services to the network layer protocols. The information is placed by LLC in the frame and identifies which network layer protocol is being used for the frame. This information allows multiple Layer 3 protocols, such as IPv4 and IPv6, to utilize the same network interface and media.
-
A network team is comparing physical WAN topologies for connecting remote sites to a headquarters building. Which topology provides high availability and connects some, but not all, remote sites?
- mesh
- partial mesh
- hub and spoke
- point-to-point
Explanation:
Partial mesh topologies provide high availability by interconnecting multiple remote sites, but do not require a connection between all remote sites. A mesh topology requires point-to-point links with every system being connected to every other system. A point-to-point topology is where each device is connected to one other device. A hub and spoke uses a central device in a star topology that connects to other point-to-point devices.
-
What method is used to manage contention-based access on a wireless network?
- CSMA/CD
- priority ordering
- CSMA/CA
- token passing
Explanation:
Carrier sense multiple access with collision avoidance (CSMA/CA) is used with wireless networking technology to mediate media contention. Carrier sense multiple access with collision detection (CSMA/CD) is used with wired Ethernet technology to mediate media contention. Priority ordering and token passing are not used (or not a method) for media access control.
-
What are the three primary functions provided by Layer 2 data encapsulation? (Choose three.)
- error correction through a collision detection method
- session control using port numbers
- data link layer addressing
- placement and removal of frames from the media
- detection of errors through CRC calculations
- delimiting groups of bits into frames
- conversion of bits into data signals
Explanation:
Through the framing process, delimiters are used to identify the start and end of the sequence of bits that make up a frame. Data link layer addressing is added to enable a frame to be delivered to a destination node. A cyclic redundancy check (CRC) field is calculated on every bit and added to the frame. If the CRC value contained in the arriving frame is the same as the one the receiving node creates, the frame will be processed.
-
What will a host on an Ethernet network do if it receives a frame with a destination MAC address that does not match its own MAC address?
- It will discard the frame.
- It will forward the frame to the next host.
- It will remove the frame from the media.
- It will strip off the data-link frame to check the destination IP address.
Explanation:
In an Ethernet network, each NIC in the network checks every arriving frame to see if the destination MAC address in the frame matches its own MAC address. If there is no match, the device discards the frame. If there is a match, the NIC passes the frame up to the next OSI layer.
-
Which frame forwarding method receives the entire frame and performs a CRC check to detect errors before forwarding the frame?
- cut-through switching
- store-and-forward switching
- fragment-free switching
- fast-forward switching
Explanation:
Fast-forward and fragment-free switching are variations of cut-through switching, which begins to forward the frame before the entire frame is received.
-
Refer to the exhibit. If host A sends an IP packet to host B, what will the destination address be in the frame when it leaves host A?
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 002 - DD:DD:DD:DD:DD:DD
- 172.168.10.99
- CC:CC:CC:CC:CC:CC
- 172.168.10.65
- BB:BB:BB:BB:BB:BB
- AA:AA:AA:AA:AA:AA
Explanation:
When a host sends information to a distant network, the Layer 2 frame header will contain a source and destination MAC address. The source address will be the originating host device. The destination address will be the router interface that connects to the same network. In the case of host A sending information to host B, the source address is AA:AA:AA:AA:AA:AA and the destination address is the MAC address assigned to the R2 Ethernet interface, BB:BB:BB:BB:BB:BB.
-
What addresses are mapped by ARP?
- destination MAC address to a destination IPv4 address
- destination IPv4 address to the source MAC address
- destination IPv4 address to the destination host name
- destination MAC address to the source IPv4 address
Explanation:
ARP, or the Address Resolution Protocol, works by mapping a destination MAC address to a destination IPv4 address. The host knows the destination IPv4 address and uses ARP to resolve the corresponding destination MAC address.
-
What are two services provided by the OSI network layer? (Choose two.)
- performing error detection
- routing packets toward the destination
- encapsulating PDUs from the transport layer
- placement of frames on the media
- collision detection
Explanation:
The OSI network layer provides several services to allow communication between devices:
- addressing
- encapsulation
- routing
- de-encapsulation
Error detection, placing frames on the media, and collision detection are all functions of the data ink layer.
-
What are two functions of NVRAM? (Choose two.)
- to store the routing table
- to retain contents when power is removed
- to store the startup configuration file
- to contain the running configuration file
- to store the ARP table
Explanation:
NVRAM is permanent memory storage, so the startup configuration file is preserved even if the router loses power.
-
Refer to the exhibit. What will be the result of entering this configuration the next time a network administrator connects a console cable to the router and no additional commands have been entered?
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 003 - The administrator will be required to enter Cisco123.
- The administrator will be required to enter Cisco234.
- The administrator will be required to enter Cisco789.
- The administrator will be presented with the R1> prompt.
Explanation:
Until both the password password and the login commands are entered in console line configuration mode, no password is required to gain access to enable mode.
-
What is the dotted decimal representation of the IPv4 address 11001011.00000000.01110001.11010011?
- 192.0.2.199
- 198.51.100.201
- 203.0.113.211
- 209.165.201.223
Explanation:
Each section (octet) contains eight binary digits. Each digit represents a specific value (128, 64, 32, 16, 8, 4, 2, and 1). Everywhere there is a 1, the specific value is relevant. Add all relevant values in a particular octet to obtain the decimal value. For example binary 11001011 equals 203 in decimal.
-
What are three characteristics of multicast transmission? (Choose three.)
- The source address of a multicast transmission is in the range of 224.0.0.0 to 224.0.0.255.
- A single packet can be sent to a group of hosts.
- Multicast transmission can be used by routers to exchange routing information.
- Routers will not forward multicast addresses in the range of 224.0.0.0 to 224.0.0.255.
- Computers use multicast transmission to request IPv4 addresses.
- Multicast messages map lower layer addresses to upper layer addresses.
Explanation:
Broadcast messages consist of single packets that are sent to all hosts on a network segment. These types of messages are used to request IPv4 addresses, and map upper layer addresses to lower layer addresses. A multicast transmission is a single packet sent to a group of hosts and is used by routing protocols, such as OSPF and RIPv2, to exchange routes. The address range 224.0.0.0 to 224.0.0.255 is reserved for link-local addresses to reach multicast groups on a local network.
-
What are the three ranges of IP addresses that are reserved for internal private use? (Choose three.)
- 10.0.0.0/8
- 64.100.0.0/14
- 127.16.0.0/12
- 172.16.0.0/12
- 192.31.7.0/24
- 192.168.0.0/16
Explanation:
The private IP address blocks that are used inside companies are as follows:
- 10.0.0.0 /8 (any address that starts with 10 in the first octet)
- 172.16.0.0 /12 (any address that starts with 172.16 in the first two octets through 172.31.255.255)
- 192.168.0.0 /16 (any address that starts with 192.168 in the first two octets)
-
What purpose does NAT64 serve in IPv6?
- It converts IPv6 packets into IPv4 packets.
- It translates private IPv6 addresses into public IPv6 addresses.
- It enables companies to use IPv6 unique local addresses in the network.
- It converts regular IPv6 addresses into 64-bit addresses that can be used on the Internet.
- It converts the 48-bit MAC address into a 64-bit host address that can be used for automatic host addressing.
Explanation:
NAT64 is typically used in IPv6 when networks are being transitioned from IPv4 to IPv6. It allows the IPv6 networks to connect to IPv4 networks (such as the Internet), and works by translating the IPv6 packets into IPv4 packets.
-
What is the most compressed representation of the IPv6 address 2001:0000:0000:abcd:0000:0000:0000:0001?
- 2001:0:abcd::1
- 2001:0:0:abcd::1
- 2001::abcd::1
- 2001:0000:abcd::1
- 2001::abcd:0:1
Explanation:
The IPv6 address 2001:0000:0000:abcd:0000:0000:0000:0001 in its most compressed format would be 2001:0:0:abcd::1. The first two hextets of zeros would each compress to a single zero. The three consecutive hextets of zeros can be compressed to a double colon ::. The three leading zeros in the last hextet can be removed. The double colon :: can only be used once in an address.
-
Which range of link-local addresses can be assigned to an IPv6-enabled interface?
- FEC0::/10
- FDEE::/7
- FE80::/10
- FF00::/8
Explanation:
Link-local addresses are in the range of FE80::/10 to FEBF::/10. The original IPv6 specification defined site-local addresses and used the prefix range FEC0::/10, but these addresses were deprecated by the IETF in favor of unique local addresses. FDEE::/7 is a unique local address because it is in the range of FC00::/7 to FDFF::/7. IPv6 multicast addresses have the prefix FF00::/8.
-
How many valid host addresses are available on an IPv4 subnet that is configured with a /26 mask?
- 254
- 190
- 192
- 62
- 64
Explanation:
When a /26 mask is used, 6 bits are used as host bits. With 6 bits, 64 addresses are possible, but one address is for the subnet number and one address is for a broadcast. This leaves 62 addresses that can be assigned to network devices.
-
A site administrator has been told that a particular network at the site must accommodate 126 hosts. Which subnet mask would be used that contains the required number of host bits?
- 255.255.255.0
- 255.255.255.128
- 255.255.255.224
- 255.255.255.240
Explanation:
The subnet mask of 255.255.255.0 has 8 host bits. The mask of 255.255.255.128 results in 7 host bits. The mask of 255.255.255.224 has 5 host bits. Finally, 255.255.255.240 represents 4 host bits.
-
Which subnet would include the address 192.168.1.96 as a usable host address?
- 192.168.1.64/26
- 192.168.1.32/27
- 192.168.1.32/28
- 192.168.1.64/29
Explanation:
For the subnet of 192.168.1.64/26, there are 6 bits for host addresses, yielding 64 possible addresses. However, the first and last subnets are the network and broadcast addresses for this subnet. Therefore, the range of host addresses for this subnet is 192.168.1.65 to 192.168.1.126. The other subnets do not contain the address 192.168.1.96 as a valid host address.
-
Which statement is true about variable-length subnet masking?
- Each subnet is the same size.
- The size of each subnet may be different, depending on requirements.
- Subnets may only be subnetted one additional time.
- Bits are returned, rather than borrowed, to create additional subnets.
Explanation:
In variable-length subnet masking, bits are borrowed to create subnets. Additional bits may be borrowed to create additional subnets within the original subnets. This may continue until there are no bits available to borrow.
-
Which scenario describes a function provided by the transport layer?
- A student is using a classroom VoIP phone to call home. The unique identifier burned into the phone is a transport layer address used to contact another network device on the same network.
- A student is playing a short web-based movie with sound. The movie and sound are encoded within the transport layer header.
- A student has two web browser windows open in order to access two web sites. The transport layer ensures the correct web page is delivered to the correct browser window.
- A corporate worker is accessing a web server located on a corporate network. The transport layer formats the screen so the web page appears properly no matter what device is being used to view the web site.
Explanation:
The source and destination port numbers are used to identify the correct application and window within that application.
-
A user opens three browsers on the same PC to access www.cisco.com to search for certification course information. The Cisco web server sends a datagram as a reply to the request from one of the web browsers. Which information is used by the TCP/IP protocol stack in the PC to identify which of the three web browsers should receive the reply?
- the destination IP address
- the destination port number
- the source IP address
- the source port number
Explanation:
Each web browser client application opens a randomly generated port number in the range of the registered ports and uses this number as the source port number in the datagram that it sends to a server. The server then uses this port number as the destination port number in the reply datagram that it sends to the web browser. The PC that is running the web browser application receives the datagram and uses the destination port number that is contained in this datagram to identify the client application.
-
What are two ways that TCP uses the sequence numbers in a segment? (Choose two.)
- to identify missing segments at the destination
- to reassemble the segments at the remote location
- to specify the order in which the segments travel from source to destination
- to limit the number of segments that can be sent out of an interface at one time
- to determine if the packet changed during transit
-
Which two tasks are functions of the presentation layer? (Choose two.)
- compression
- addressing
- encryption
- session control
- authentication
Explanation:
The presentation layer deals with common data format. Encryption, formatting, and compression are some of the functions of the layer. Addressing occurs in the network layer, session control occurs in the session layer, and authentication takes place in the application or session layer.
-
What is a key characteristic of the peer-to-peer networking model?
- wireless networking
- social networking without the Internet
- network printing using a print server
- resource sharing without a dedicated server
Explanation:
The peer-to-peer (P2P) networking model allows data, printer, and resource sharing without a dedicated server.
-
A technician can ping the IP address of the web server of a remote company but cannot successfully ping the URL address of the same web server. Which software utility can the technician use to diagnose the problem?
- tracert
- ipconfig
- netstat
- nslookup
Explanation:
Traceroute (tracert) is a utility that generates a list of hops that were successfully reached along the path from source to destination.This list can provide important verification and troubleshooting information. The ipconfig utility is used to display the IP configuration settings on a Windows PC. The Netstat utility is used to identify which active TCP connections are open and running on a networked host. Nslookup is a utility that allows the user to manually query the name servers to resolve a given host name. This utility can also be used to troubleshoot name resolution issues and to verify the current status of the name servers.
-
Which domain name would be an example of a top-level domain?
- www.cisco.com
- cisco.com
- .com
- root.cisco.com
-
Explanation:
Top-level domains represent a country or type of organization, such as .com or .edu.
-
A PC obtains its IP address from a DHCP server. If the PC is taken off the network for repair, what happens to the IP address configuration?
- The configuration is permanent and nothing changes.
- The address lease is automatically renewed until the PC is returned.
- The address is returned to the pool for reuse when the lease expires.
- The configuration is held by the server to be reissued when the PC is returned.
Explanation:
When a DCHP address is issued to a host, it is for a specific lease time. Once the lease expires, the address is returned to the DHCP pool.
-
A wireless host needs to request an IP address. What protocol would be used to process the request?
- FTP
- HTTP
- DHCP
- ICMP
- SNMP
Explanation:
The DHCP protocol is used to request, issue, and manage IP addressing information. CSMA/CD is the access method used with wired Ethernet. ICMP is used to test connectivity. SNMP is used with network management and FTP is used for file transfer.
-
Which example of malicious code would be classified as a Trojan horse?
- malware that was written to look like a video game
- malware that requires manual user intervention to spread between systems
- malware that attaches itself to a legitimate program and spreads to other programs when launched
- malware that can automatically spread from one system to another by exploiting a vulnerability in the target
Explanation:
A Trojan horse is malicious code that has been written specifically to look like a legitimate program. This is in contrast to a virus, which simply attaches itself to an actual legitimate program. Viruses require manual intervention from a user to spread from one system to another, while a worm is able to spread automatically between systems by exploiting vulnerabilities on those devices.
-
When applied to a router, which command would help mitigate brute-force password attacks against the router?
- exec-timeout 30
- service password-encryption
- banner motd $Max failed logins = 5$
- login block-for 60 attempts 5 within 60
Explanation:
The login block-for command sets a limit on the maximum number of failed login attempts allowed within a defined period of time. If this limit is exceeded, no further logins are allowed for the specified period of time. This helps to mitigate brute-force password cracking since it will significantly increase the amount of time required to crack a password. The exec-timeout command specifies how long the session can be idle before the user is disconnected. The service password-encryption command encrypts the passwords in the running configuration. The banner motd command displays a message to users who are logging in to the device.
-
Match the description with the associated IOS mode. (not all options are used.)
- Question
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 004 - Answer
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 005
- Question
-
Refer to the exhibit. Match the packets with their destination IP address to the exiting interfaces on the router. (Not all targets are used.)
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 006 - Question
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 007 - Answer
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 008 Explanation:
Packets with a destination of 172.17.6.15 are forwarded through Fa0/0. Packets with a destination of 172.17.10.5 are forwarded through Fa1/1. Packets with a destination of 172.17.12.10 are forwarded through Fa1/0. Packets with a destination of 172.17.14.8 are forwarded through Fa0/1. Because network 172.17.8.0 has no entry in the routing table, it will take the gateway of last resort, which means that packets with a destination of 172.17.8.20 are forwarded through Serial0/0/0. Because a gateway of last resort exists, no packets will be dropped.
- Question
-
A company is expanding its business to other countries. All branch offices must remain connected to corporate headquarters at all times. Which network technology is required to support this requirement?
- LAN
- MAN
- WAN
- WLAN
Explanation:
A local-area network (LAN) normally connects end users and network resources over a limited geographic area using Ethernet technology. A wireless LAN (WLAN) serves the same purpose as a LAN but uses wireless technologies. A metropolitan-area network (MAN) spans a larger geographic area such as a city, and a wide-area network (WAN) connects networks together over a large geographic area. WANs can span cities, countries, or the globe.
-
A home user is looking for an ISP connection that provides high speed digital transmission over regular phone lines. What ISP connection type should be used?
- DSL
- dial-up
- satellite
- cell modem
- cable modem
-
How does quality of service help a network support a wide range of applications and services?
- by limiting the impact of a network failure
- by allowing quick recovery from network failures
- by providing mechanisms to manage congested network traffic
- by providing the ability for the network to grow to accommodate new users
Explanation:
Quality of service (QoS), is a vital component of the architecture of a network. With QoS, network administrators can provide applications with predictable and measurable service guarantees through mechanisms that manage congested network traffic.
-
After making configuration changes on a Cisco switch, a network administrator issues a copy running-config startup-config command. What is the result of issuing this command?
- The new configuration will be stored in flash memory.
- The new configuration will be loaded if the switch is restarted.
- The current IOS file will be replaced with the newly configured file.
- The configuration changes will be removed and the original configuration will be restored.
Explanation:
With the copy running-config startup-config command, the content of the current operating configuration replaces the startup configuration file stored in NVRAM. The configuration file saved in NVRAM will be loaded when the device is restarted.
-
Refer to the exhibit. A network administrator is configuring access control to switch SW1. If the administrator has already logged into a Telnet session on the switch, which password is needed to access privileged EXEC mode?
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 009 - letmein
- secretin
- lineconin
- linevtyin
Explanation:
Telnet accesses a network device through the virtual interface configured with the line VTY command. The password configured under this is required to access the user EXEC mode. The password configured under the line console 0 command is required to gain entry through the console port, and the enable and enable secret passwords are used to allow entry into the privileged EXEC mode.
- letmein
-
What function does pressing the Tab key have when entering a command in IOS?
- It aborts the current command and returns to configuration mode.
- It exits configuration mode and returns to user EXEC mode.
- It moves the cursor to the beginning of the next line.
- It completes the remainder of a partially typed word in a command.
Explanation:
Pressing the Tab key after a command has been partially typed will cause the IOS to complete the rest of the command.
-
What layer is responsible for routing messages through an internetwork in the TCP/IP model?
- internet
- transport
- network access
- session
Explanation:
The TCP/IP model consists of four layers: application, transport, internet, and network access. Of these four layers, it is the internet layer that is responsible for routing messages. The session layer is not part of the TCP/IP model but is rather part of the OSI model.
-
Which statement accurately describes a TCP/IP encapsulation process when a PC is sending data to the network?
- Data is sent from the internet layer to the network access layer.
- Packets are sent from the network access layer to the transport layer.
- Segments are sent from the transport layer to the internet layer.
- Frames are sent from the network access layer to the internet layer.
Explanation:
When the data is traveling from the PC to the network, the transport layer sends segments to the internet layer. The internet layer sends packets to the network access layer, which creates frames and then converts the frames to bits. The bits are released to the network media.
-
What unique address is embedded in an Ethernet NIC and used for communication on an Ethernet network?
- host address
- IP address
- MAC address
- network address
Explanation:
The MAC address is a 48-bit address that is burned into every Ethernet NIC. Each MAC address is unique throughout the world.
-
Which procedure is used to reduce the effect of crosstalk in copper cables?
- requiring proper grounding connections
- twisting opposing circuit wire pairs together
- wrapping the bundle of wires with metallic shielding
- designing a cable infrastructure to avoid crosstalk interference
- avoiding sharp bends during installation
Explanation:
In copper cables, crosstalk is a disturbance caused by the electric or magnetic fields of a signal on one wire interfering with the signal in an adjacent wire. Twisting opposing circuit wire pairs together can effectively cancel the crosstalk. The other options are effective measures to counter the negative effects of EMI and RFI, but not crosstalk.
-
During the encapsulation process, what occurs at the data link layer for a PC connected to an Ethernet network?
- An IP address is added.
- The logical address is added.
- The physical address is added.
- The process port number is added.
Explanation:
The Ethernet frame includes the source and destination physical address. The trailer includes a CRC value in the Frame Check Sequence field to allow the receiving device to determine if the frame has been changed (has errors) during the transmission.
-
What are two characteristics of Ethernet MAC addresses? (Choose two.)
- They are globally unique.
- They are routable on the Internet.
- They are expressed as 12 hexadecimal digits.
- MAC addresses use a flexible hierarchical structure.
- MAC addresses must be unique for both Ethernet and serial interfaces on a device.
Explanation:
An Ethernet MAC address is a 48-bit binary value expressed as 12 hexadecimal digits. MAC addresses must be globally unique by design. MAC addresses are in flat structure and thus they are not routable on the Internet. Serial interfaces do not use MAC addresses.
-
If a device receives an Ethernet frame of 60 bytes, what will it do?
- drop the frame
- process the frame as it is
- send an error message to the sending device
- add random data bytes to make it 64 bytes long and then forward it
Explanation:
Ethernet standards define the minimum frame size as 64 bytes. A frame less than 64 bytes is considered a “collision fragment” or “runt frame” and is automatically discarded by receiving devices.
-
Under which two circumstances will a switch flood a frame out of every port except the port that the frame was received on? (Choose two.)
- The frame has the broadcast address as the destination address.
- The destination address is unknown to the switch.
- The source address in the frame header is the broadcast address.
- The source address in the frame is a multicast address.
- The destination address in the frame is a known unicast address.
Explanation:
A switch will flood a frame out of every port, except the one that the frame was received from, under two circumstances. Either the frame has the broadcast address as the destination address, or the destination address is unknown to the switch.
-
Which switching method has the lowest level of latency?
- cut-through
- store-and-forward
- fragment-free
- fast-forward
Explanation:
Fast-forward switching begins to forward a frame after reading the destination MAC address, resulting in the lowest latency. Fragment-free reads the first 64 bytes before forwarding. Store-and-forward has the highest latency because it reads the entire frame before beginning to forward it. Both fragment-free and fast-forward are types of cut-through switching.
-
Which two commands can be used on a Windows host to display the routing table? (Choose two.)
- netstat -s
- route print
- show ip route
- netstat -r
- tracert
Explanation:
On a Windows host, the route print or netstat -r commands can be used to display the host routing table. Both commands generate the same output. On a router, the show ip route command is used to display the routing table. The netstat –scommand is used to display per-protocol statistics. The tracert command is used to display the path that a packet travels to its destination.
-
Which two functions are primary functions of a router? (Choose two.)
- packet forwarding
- microsegmentation
- domain name resolution
- path selection
- flow control
-
What is the binary representation of 0xCA?
- 10111010
- 11010101
- 11001010
- 11011010
Explanation:
When converted, CA in hex is equivalent to 11011010 in binary. One way to do the conversion is one nibble at a time, C = 1100 and A = 1010. Combine the two nibbles gives 11001010.
-
At a minimum, which address is required on IPv6-enabled interfaces?
- link-local
- unique local
- site local
- global unicast
Explanation:
All IPv6 enabled interfaces must at minimum have a link-local address. Other IPv6 addresses can be assigned to the interface as required.
-
Which service provides dynamic global IPv6 addressing to end devices without using a server that keeps a record of available IPv6 addresses?
- stateful DHCPv6
- SLAAC
- static IPv6 addressing
- stateless DHCPv6
Explanation:
Using stateless address autoconfiguration (SLAAC), a PC can solicit a router and receive the prefix length of the network. From this information the PC can then create its own IPv6 global unicast address.
-
What is the purpose of the command ping ::1?
- It tests the internal configuration of an IPv6 host.
- It tests the broadcast capability of all hosts on the subnet.
- It tests the multicast connectivity to all hosts on the subnet.
- It tests the reachability of the default gateway for the network.
Explanation:
The address ::1 is an IPv6 loopback address. Using the command ping ::1 tests the internal IP stack to ensure that it is configured and functioning correctly. It does not test reachability to any external device, nor does it confirm that IPv6 addresses are properly configured on the host.
-
How many usable IP addresses are available on the 192.168.1.0/27 network?
- 256
- 254
- 62
- 30
- 16
- 32
Explanation:
A /27 mask is the same as 255.255.255.224. This leaves 5 host bits. With 5 host bits, 32 IP addresses are possible, but one address represents the subnet number and one address represents the broadcast address. Thus, 30 addresses can then be used to assign to network devices.
-
A network administrator wants to have the same subnet mask for three subnetworks at a small site. The site has the following networks and numbers of devices:
Subnetwork A: IP phones – 10 addresses
Subnetwork B: PCs – 8 addresses
Subnetwork C: Printers – 2 addressesWhat single subnet mask would be appropriate to use for the three subnetworks?
- 255.255.255.0
- 255.255.255.240
- 255.255.255.248
- 255.255.255.252
Explanation:
If the same mask is to be used, then the network with the most hosts must be examined for number of hosts. Because this is 10 hosts, 4 host bits are needed. The /28 or 255.255.255.240 subnet mask would be appropriate to use for these networks.
-
What subnet mask is needed if an IPv4 network has 40 devices that need IP addresses and address space is not to be wasted?
- 255.255.255.0
- 255.255.255.128
- 255.255.255.192
- 255.255.255.224
- 255.255.255.240
Explanation:
In order to accommodate 40 devices, 6 host bits are needed. With 6 bits, 64 addresses are possible, but one address is for the subnet number and one address is for a broadcast. This leaves 62 addresses that can be assigned to network devices. The mask associated with leaving 6 host bits for addressing is 255.255.255.192.
-
What are two characteristics shared by TCP and UDP? (Choose two.)
- default window size
- connectionless communication
- port numbering
- 3-way handshake
- ability to to carry digitized voice
- use of checksum
Explanation:
Both TCP and UDP use source and destination port numbers to distinguish different data streams and to forward the right data segments to the right applications. Error checking the header and data is done by both protocols by using a checksum calculation to determine the integrity of the data that is received. TCP is connection-oriented and uses a 3-way handshake to establish an initial connection. TCP also uses window to regulate the amount of traffic sent before receiving an acknowledgment. UDP is connectionless and is the best protocol for carry digitized VoIP signals.
-
Why are port numbers included in the TCP header of a segment?
- to indicate the correct router interface that should be used to forward a segment
- to identify which switch ports should receive or forward the segment
- to determine which Layer 3 protocol should be used to encapsulate the data
- to enable a receiving host to forward the data to the appropriate application
- to allow the receiving host to assemble the packet in the proper order
-
Which two protocols operate at the highest layer of the TCP/IP protocol stack? (Choose two.)
- DNS
- Ethernet
- IP
- POP
- TCP
- UDP
Explanation:
The application layer is the top layer of the TCP/IP protocol stack. Application layer protocols include HTTP, DNS, HTML, TFTP, POP, IMAP, FTP, and SMTP.
-
What is one difference between the client-server and peer-to-peer network models?
- Only in the client-server model can file transfers occur.
- Every device in a peer-to-peer network can function as a client or a server.
- A peer-to-peer network transfers data faster than a transfer using a client-server network.
- A data transfer that uses a device serving in a client role requires that a dedicated server be present.
Explanation:
Data transfer speeds depend on a number of factors including the amount of traffic, the quality of service imposed, and the network media. Transfer speeds are not dependent on the network model type. File transfers can occur using the client-server model or the peer-to-peer model. A data transfer between a device acting in the client role and a device acting in the server role can occur in both peer-to-peer and client-server networks.
-
Which networking model is being used when an author uploads one chapter document to a file server of a book publisher?
- peer-to-peer
- master-slave
- client/server
- point-to-point
Explanation:
In the client/server network model, a network device assumes the role of server in order to provide a particular service such as file transfer and storage. In the client/server network model, a dedicated server does not have to be used, but if one is present, the network model being used is the client/server model. In contrast, a peer-to-peer network does not have a dedicated server.
-
What network service resolves the URL entered on a PC to the IP address of the destination server?
- DNS
- DHCP
- FTP
- SNMP
Explanation:
When a client attempts to connect to a website, the destination URL must be resolved to an IP address. To do this the client queries a Domain Name System (DNS) server.
-
A network engineer is analyzing reports from a recently performed network baseline. Which situation would depict a possible latency issue?
- a change in the bandwidth according to the show interfaces output
- a next-hop timeout from a traceroute
- an increase in host-to-host ping response times
- a change in the amount of RAM according to the show version output
Explanation:
While analyzing historical reports an administrator can compare host-to-host timers from the ping command and depict possible latency issues.
-
Which firewall feature is used to ensure that packets coming into a network are legitimate responses to requests initiated from internal hosts?
- stateful packet inspection
- URL filtering
- application filtering
- packet filtering
Explanation:
Stateful packet inspection on a firewall checks that incoming packets are actually legitimate responses to requests originating from hosts inside the network. Packet filtering can be used to permit or deny access to resources based on IP or MAC address. Application filtering can permit or deny access based on port number. URL filtering is used to permit or deny access based on URL or on keywords.
-
Fill in the blank.
During data communications, a host may need to send a single message to a specific group of destination hosts simultaneously. This message is in the form of a Multicast message.
-
A medium-sized business is researching available options for connecting to the Internet. The company is looking for a high speed option with dedicated, symmetric access. Which connection type should the company choose?
- DSL
- dialup
- satellite
- leased line
- cable modem
-
What is the purpose of having a converged network?
- to provide high speed connectivity to all end devices
- to make sure that all types of data packets will be treated equally
- to achieve fault tolerance and high availability of data network infrastructure devices
- to reduce the cost of deploying and maintaining the communication infrastructure
Explanation:
With the development of technology, companies can now consolidate disparate networks onto one platform called a converged network. In a converged network, voice, video, and data travel over the same network, thus eliminating the need to create and maintain separate networks. This also reduces the costs associated with providing and maintaining the communication network infrastructure.
-
What characteristic of a network enables it to quickly grow to support new users and applications without impacting the performance of the service being delivered to existing users?
- reliability
- scalability
- quality of service
- accessibility
Explanation:
Networks must be able to quickly grow to support new users and services, without impacting existing users and services. This ability to grow is known as scalability.
-
After several configuration changes are made to a router, the copy running-configuration startup-configuration command is issued. Where will the changes be stored?
- flash
- ROM
- NVRAM
- RAM
- the configuration register
- a TFTP server
-
Refer to the exhibit. From global configuration mode, an administrator is attempting to create a message-of-the-day banner by using the command banner motd V Authorized access only! Violators will be prosecuted! V When users log in using Telnet, the banner does not appear correctly. What is the problem?
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 015 - The banner message is too long.
- The delimiting character appears in the banner message.
- The symbol “!” signals the end of a banner message.
- Message-of-the-day banners will only appear when a user logs in through the console port.
-
What are three characteristics of an SVI? (Choose three.)
- It is designed as a security protocol to protect switch ports.
- It is not associated with any physical interface on a switch.
- It is a special interface that allows connectivity by different types of media.
- It is required to allow connectivity by any device at any location.
- It provides a means to remotely manage a switch.
- It is associated with VLAN1 by default.
Explanation:
Switches have one or more switch virtual interfaces (SVIs). SVIs are created in software since there is no physical hardware associated with them. Virtual interfaces provide a means to remotely manage a switch over a network that is using IP. Each switch comes with one SVI appearing in the default configuration “out-of-the-box.” The default SVI interface is VLAN1.
-
A technician configures a switch with these commands:SwitchA(config)# interface vlan 1
SwitchA(config-if)# ip address 192.168.1.1 255.255.255.0
SwitchA(config-if)# no shutdownWhat is the technician configuring?
- Telnet access
- SVI
- password encryption
- physical switchport access
Explanation:
For a switch to have an IP address, a switch virtual interface must be configured. This allows the switch to be managed remotely over the network.
-
In computer communication, what is the purpose of message encoding?
- to convert information to the appropriate form for transmission
- to interpret information
- to break large messages into smaller frames
- to negotiate correct timing for successful communication
Explanation:
Before a message is sent across a network it must first be encoded. Encoding is the process of converting the data message into another format suitable for transmission across the physical medium. Each bit of the message is encoded into a pattern of sounds, light waves, or electrical impulses depending on the network media over which the bits are transmitted. The destination host receives and decodes the signals in order to interpret the message.
-
What is the process of dividing a data stream into smaller pieces before transmission?
- segmentation
- encapsulation
- encoding
- flow control
Explanation:
Data streams would cause significant network congestion if they were transmitted as a single large stream of bits. To increase efficiency, data streams are segmented into smaller more manageable pieces which are then transmitted over the network.
-
When IPv4 addressing is manually configured on a web server, which property of the IPv4 configuration identifies the network and host portion for an IPv4 address?
- DNS server address
- subnet mask
- default gateway
- DHCP server address
Explanation:
There are several components that need to be entered when configuring IPv4 for an end device:
- IPv4 address – uniquely identifies an end device on the network
- Subnet mask – determines the network address portion and host portion for an IPv4 address
- Default gateway – the IP address of the router interface used for communicating with hosts in another network
- DNS server address – the IP address of the Domain Name System (DNS) server
DHCP server address (if DHCP is used) is not configured manually on end devices. It will be provided by a DHCP server when an end device requests an IP address.
-
A network engineer is measuring the transfer of bits across the company backbone for a mission critical database application. The engineer notices that the network throughput appears lower than the bandwidth expected. Which three factors could influence the differences in throughput? (Choose three.)
- the amount of traffic that is currently crossing the network
- the sophistication of the encapsulation method applied to the data
- the type of traffic that is crossing the network
- the latency that is created by the number of network devices that the data is crossing
- the bandwidth of the WAN connection to the Internet
- the reliability of the gigabit Ethernet infrastructure of the backbone
Explanation:
Throughput usually does not match the specified bandwidth of physical links due to multiple factors. These factors include, the amount of traffic, type of traffic, and latency created by the network devices the data has to cross.
-
Which type of UTP cable is used to connect a PC to a switch port?
- console
- rollover
- crossover
- straight-through
Explanation:
A rollover cable is a Cisco proprietary cable used to connect to a router or switch console port. A straight-through (also called patch) cable is usually used to interconnect a host to a switch and a switch to a router. A crossover cable is used to interconnect similar devices together, for example, between two switches, two routers, and two hosts.
-
What are two actions performed by a Cisco switch? (Choose two.)
- building a routing table that is based on the first IP address in the frame header
- using the source MAC addresses of frames to build and maintain a MAC address table
- forwarding frames with unknown destination IP addresses to the default gateway
- utilizing the MAC address table to forward frames via the destination MAC address
- examining the destination MAC address to add new entries to the MAC address table
Explanation:
Important actions that a switch performs are as follows:
- When a frame comes in, the switch examines the Layer 2 source address to build and maintain the Layer 2 MAC address table.
- It examines the Layer 2 destination address to determine how to forward the frame. When the destination address is in the MAC address table, then the frame is sent out a particular port. When the address is unknown, the frame is sent to all ports that have devices connected to that network.
-
What are two examples of the cut-through switching method? (Choose two.)
- store-and-forward switching
- fast-forward switching
- CRC switching
- fragment-free switching
- QOS switching
Explanation:
Store-and forward switching accepts the entire frame and performs error checking using CRC before forwarding the frame. Store-and-forward is often required for QOS analysis. Fast-forward and fragment-free are both variations of the cut-through switching method where only part of the frame is received before the switch begins to forward it.
-
What information is added during encapsulation at OSI Layer 3?
- source and destination MAC
- source and destination application protocol
- source and destination port number
- source and destination IP address
Explanation:
IP is a Layer 3 protocol. Layer 3 devices can open the Layer 3 header to inspect the Layer 3 header which contains IP-related information including the source and destination IP addresses.
-
Refer to the exhibit. The network administrator for a small advertising company has chosen to use the 192.168.5.96/27 network for internal LAN addressing. As shown in the exhibit, a static IP address is assigned to the company web server. However, the web server cannot access the Internet. The administrator verifies that local workstations with IP addresses that are assigned by a DHCP server can access the Internet, and the web server is able to ping local workstations. Which component is incorrectly configured?
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 016 - subnet mask
- DNS address
- host IP address
- default gateway address
Explanation:
When a 255.255.255.224 subnet mask is used, the first three bits of the last octet are part of the network portion for an IPv4 address in the subnet. For the 192.168.5.96/27 network, valid host addresses are 192.168.5.97 through 192.168.5.126. The default gateway address is for the Layer 3 device on the same network and it must contain an IP address within the valid IP address range.
-
Why does a Layer 3 device perform the ANDing process on a destination IP address and subnet mask?
- to identify the broadcast address of the destination network
- to identify the host address of the destination host
- to identify faulty frames
- to identify the network address of the destination network
Explanation:
ANDing allows us to identify the network address from the IP address and the network mask.
-
Which three addresses are valid public addresses? (Choose three.)
- 198.133.219.17
- 192.168.1.245
- 10.15.250.5
- 128.107.12.117
- 192.15.301.240
- 64.104.78.227
-
What type of IPv6 address is FE80::1?
- loopback
- link-local
- multicast
- global unicast
Explanation:
Link-local IPv6 addresses start with FE80::/10, which is any address from FE80:: to FEBF::. Link-local addresses are used extensively in IPv6 and allow directly connected devices to communicate with each other on the link they share.
-
Refer to the exhibit. On the basis of the output, which two statements about network connectivity are correct? (Choose two.)
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 017 - There is connectivity between this device and the device at 192.168.100.1.
- The connectivity between these two hosts allows for videoconferencing calls.
- There are 4 hops between this device and the device at 192.168.100.1.
- The average transmission time between the two hosts is 2 milliseconds.
- This host does not have a default gateway configured.
Explanation:
The output displays a successful Layer 3 connection between a host computer and a host at 19.168.100.1. It can be determined that 4 hops exist between them and the average transmission time is 1 milliseconds. Layer 3 connectivity does not necessarily mean that an application can run between the hosts.
-
How many hosts are addressable on a network that has a mask of 255.255.255.248?
- 2
- 6
- 8
- 14
- 16
- 254
Explanation:
The subnet mask of 255.255.255.248 is the same as /29. This means the network portion of the address is 29 of the 32 bits in the address. Only 3 bits remain for host bits. 2^3 = 8, but one of these addresses has to be used for the network number and one address must be used as the broadcast address to reach all of the hosts on this network. That leaves only 6 usable IP addresses that can be assigned to hosts in this network. Don’t forget that the default gateway must be one of these devices if this network is to communicate with other networks.
-
Refer to the exhibit. Consider the IP address of 192.168.10.0/24 that has been assigned to a high school building. The largest network in this building has 100 devices. If 192.168.10.0 is the network number for the largest network, what would be the network number for the next largest network, which has 40 devices?
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 018 - 192.168.10.0
- 192.168.10.128
- 192.168.10.192
- 192.168.10.224
- 192.168.10.240
Explanation:
The first thing to calculate is what IP addresses are used by the largest LAN. Because the LAN has 100 hosts, 7 bits must be left for host bits. This would be a subnet mask of 255.255.255.128 for the largest LAN (192.168.10.0/25). The IP addresses range from 192.168.10.0 through 192.168.10.127. 192.168.10.0 is the network number (all 0s in the host bits) and 192.168.10.127 is the broadcast for this Ethernet LAN (all 1s in the host bits). The next available IP address is the next network number – 192.168.10.128.
-
In what two situations would UDP be the preferred transport protocol over TCP? (Choose two.)
- when applications need to guarantee that a packet arrives intact, in sequence, and unduplicated
- when a faster delivery mechanism is needed
- when delivery overhead is not an issue
- when applications do not need to guarantee delivery of the data
- when destination port numbers are dynamic
Explanation:
UDP is a stateless protocol, which means that neither device on either end of the conversation must keep track of the conversation. As a stateless protocol, UDP is used as the Layer 4 protocol for applications that need speedy (best-effort) delivery. An example of such traffic is the transport of digitized voice or video.
-
What important information is added to the TCP/IP transport layer header to ensure communication and connectivity with a remote network device?
- timing and synchronization
- destination and source port numbers
- destination and source physical addresses
- destination and source logical network addresses
Explanation:
The destination and source port numbers are used to identify exactly which protocol and process is requesting or responding to a request.
-
What is the TCP mechanism used in congestion avoidance?
- three-way handshake
- socket pair
- two-way handshake
- sliding window
Explanation:
TCP uses windows to attempt to manage the rate of transmission to the maximum flow that the network and destination device can support while minimizing loss and retransmissions. When overwhelmed with data, the destination can send a request to reduce the of the window. This congestion avoidance is called sliding windows.
-
Which three statements characterize UDP? (Choose three.)
- UDP provides basic connectionless transport layer functions.
- UDP provides connection-oriented, fast transport of data at Layer 3.
- UDP relies on application layer protocols for error detection.
- UDP is a low overhead protocol that does not provide sequencing or flow control mechanisms.
- UDP relies on IP for error detection and recovery.
- UDP provides sophisticated flow control mechanisms.
Explanation:
UDP is a simple protocol that provides the basic transport layer functions. It has much lower overhead than TCP because it is not connection-oriented and does not offer the sophisticated retransmission, sequencing, and flow control mechanisms that provide reliability.
-
Which two roles can a computer assume in a peer-to-peer network where a file is being shared between two computers? (Choose two.)
- client
- master
- server
- slave
- transient
Explanation:
In a peer-to-peer (P2P) network, two or more computers are connected and can share resources without the use of a dedicated server. The computer that has the file acts as a server for the device (the client) that requests the file.
-
What is the function of the HTTP GET message?
- to request an HTML page from a web server
- to send error information from a web server to a web client
- to upload content to a web server from a web client
- to retrieve client email from an email server using TCP port 110
Explanation:
There are three common HTTP message types:
- GET – used by clients to request data from the web server
- POST – used by clients to upload data to a web server
- PUT – used by clients to upload data to a web server
-
When planning for network growth, where in the network should packet captures take place to assess network traffic?
- on as many different network segments as possible
- only at the edge of the network
- between hosts and the default gateway
- only on the busiest network segment
Explanation:
Because some types of traffic will be only on specific network segments, packet captures for analysis should be performed on as many segments as possible.
-
Refer to the exhibit. An administrator is testing connectivity to a remote device with the IP address 10.1.1.1. What does the output of this command indicate?
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 019 - Connectivity to the remote device was successful.
- A router along the path did not have a route to the destination.
- A ping packet is being blocked by a security device along the path.
- The connection timed out while waiting for a reply from the remote device.
Explanation:
In the output of the ping command, an exclamation mark (!) indicates a response was successfully received, a period (.) indicates that the connection timed out while waiting for a reply, and the letter “U” indicates that a router along the path did not have a route to the destination and sent an ICMP destination unreachable message back to the source.
-
Match each item to the type of topology diagram on which it is typically identified. (Not all options are used.)
- Question
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 020 - Answer
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 021 Explanation:A logical topology diagram typically depicts the IP addressing scheme and groupings of devices and ports. A physical topology diagram shows how those devices are connected to each other and the network, focusing on the physical locations of intermediary devices, configured ports, and cabling.
- Question
-
Match the situation with the appropriate use of network media.
- Question
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 024 - Answer
Cisco ITN CCNA 1 v6.0 Final Exam Answer R&S 2018 2019 025 Explanation:Copper Cables – horizontal cabling structure and desktop PCs in offices in an enterprise
Fiber optic – backbone cabling in an enterprise and long-haul networks
Wireless – coffee shops and waiting rooms in a hospital
- Question
-
Recommend
From year to year, Cisco has updated many versions with difference questions. The latest version is version 6.0 in 2018. What is your version? It depends on your instructor creating your class. We recommend you to go thought all version if you are not clear. While you take online test with netacad.com, You may get random questions from all version. Each version have 1 to 10 different questions or more. After you review all questions, You should practice with our online test system by go to «Online Test» link below.
| Version 5.02 | Version 5.1 | Version 6.0 | Online Assessment |
| Final Exam | Final Exam | Final Exam | Online A, Online B, Online C |
| CCNA2 Pretest Exam | |||
| Pretest Exam | Pretest Exam | Pretest Exam | Online Test |
CCNA 3 Final Exam Answers
1. Which design feature will limit the size of a failure domain in an enterprise network?
- the purchase of enterprise equipment that is designed for large traffic volume
- the installation of redundant power supplies
- the use of a collapsed core design
- the use of the building switch block approach
2. Which two things should a network administrator modify on a router to perform password recovery? (Choose two.)
- the system image file
- the NVRAM file system
- the configuration register value
- the startup configuration file
- system ROM
3. What type of network uses one common infrastructure to carry voice, data, and video signals?
- borderless
- converged
- managed
- switched
4. What are three advantages of using private IP addresses and NAT? (Choose three.)
- hides private LAN addressing from outside devices that are connected to the Internet
- permits LAN expansion without additional public IP addresses
- reduces CPU usage on customer routers
- creates multiple public IP addresses
- improves the performance of the router that is connected to the Internet
- conserves registered public IP addresses
5. Which two scenarios are examples of remote access VPNs? (Choose two.)
- All users at a large branch office can access company resources through a single VPN connection.
- A small branch office with three employees has a Cisco ASA that is used to create a VPN connection to the HQ.
- A toy manufacturer has a permanent VPN connection to one of its parts suppliers.
- A mobile sales agent is connecting to the company network via the Internet connection at a hotel.
- An employee who is working from home uses VPN client software on a laptop in order to connect to the company network.
6. What are three benefits of cloud computing? (Choose three.)
- It utilizes end-user clients to do a substantial amount of data preprocessing and storage.
- It uses open-source software for distributed processing of large datasets.
- It streamlines the IT operations of an organization by subscribing only to needed services.
- It enables access to organizational data anywhere and at any time.
- It turns raw data into meaningful information by discovering patterns and relationships.
- It eliminates or reduces the need for onsite IT equipment, maintenance, and management.
7. What is a characteristic of a single-area OSPF network?
- All routers share a common forwarding database.
- All routers have the same neighbor table.
- All routers are in the backbone area.
- All routers have the same routing table.
8. What is a WAN?
- a network infrastructure that spans a limited physical area such as a city
- a network infrastructure that provides access to other networks over a large geographic area
- a network infrastructure that provides access in a small geographic area
- a network infrastructure designed to provide data storage, retrieval, and replication
9. A network administrator has been tasked with creating a disaster recovery plan. As part of this plan, the administrator is looking for a backup site for all of the data on the company servers. What service or technology would support this requirement?
- data center
- virtualization
- dedicated servers
- software defined networking
10. Which type of OSPF packet is used by a router to discover neighbor routers and establish neighbor adjacency?
- link-state update
- hello
- database description
- link-state request
11. Which two statements are characteristics of a virus? (Choose two.)
- A virus has an enabling vulnerability, a propagation mechanism, and a payload.
- A virus can be dormant and then activate at a specific time or date.
- A virus provides the attacker with sensitive data, such as passwords.
- A virus replicates itself by independently exploiting vulnerabilities in networks.
- A virus typically requires end-user activation.
Explanation: The type of end user interaction required to launch a virus is typically opening an application, opening a web page, or powering on the computer. Once activated, a virus may infect other files located on the computer or other computers on the same network.
12. Which public WAN access technology utilizes copper telephone lines to provide access to subscribers that are multiplexed into a single T3 link connection?
- ISDN
- DSL
- cable
- dialup
13. A customer needs a metropolitan area WAN connection that provides high-speed, dedicated bandwidth between two sites. Which type of WAN connection would best fulfill this need?
- packet-switched network
- Ethernet WAN
- circuit-switched network
- MPLS
14. A company has contracted with a network security firm to help identify the vulnerabilities of the corporate network. The firm sends a team to perform penetration tests to the company network. Why would the team use debuggers?
- to detect installed tools within files and directories that provide threat actors remote access and control over a computer or network
- to reverse engineer binary files when writing exploits and when analyzing malware
- to obtain specially designed operating systems preloaded with tools optimized for hacking
- to detect any evidence of a hack or malware in a computer or network
15. Consider the following output for an ACL that has been applied to a router via the access-class in command. What can a network administrator determine from the output that is shown?
R1# Standard IP access list 2 10 permit 192.168.10.0, wildcard bits 0.0.0.255 (2 matches) 20 deny any (1 match)
- Two devices connected to the router have IP addresses of 192.168.10. x .
- Two devices were able to use SSH or Telnet to gain access to the router.
- Traffic from one device was not allowed to come into one router port and be routed outbound a different router port.
- Traffic from two devices was allowed to enter one router port and be routed outbound to a different router port.
Explanation: The access-class command is used only on VTY ports. VTY ports support Telnet and/or SSH traffic. The match permit ACE is how many attempts were allowed using the VTY ports. The match deny ACE shows that a device from a network other than 192.168.10.0 was not allowed to access the router through the VTY ports.
16. What command would be used as part of configuring NAT or PAT to clear dynamic entries before the timeout has expired?
- clear ip dhcp
- clear ip nat translation
- clear access-list counters
- clear ip pat statistics
17. What are two characteristics of video traffic? (Choose two.)
- Video traffic consumes less network resources than voice traffic consumes.
- Video traffic latency should not exceed 400 ms.
- Video traffic is more resilient to loss than voice traffic is.
- Video traffic requires a minimum of 30 kbs of bandwidth.
- Video traffic is unpredictable and inconsistent.
18. Refer to the exhibit. A technician is configuring R2 for static NAT to allow the client to access the web server. What is a possible reason that the client PC cannot access the web server?
- The IP NAT statement is incorrect.
- Interface Fa0/1 should be identified as the outside NAT interface.
- Interface S0/0/0 should be identified as the outside NAT interface.
- The configuration is missing a valid access control list.
Explanation: Interface S0/0/0 should be identified as the outside NAT interface. The command to do this would be R2(config-if)# ip nat outside.
19. In setting up a small office network, the network administrator decides to assign private IP addresses dynamically to workstations and mobile devices. Which feature must be enabled on the company router in order for office devices to access the internet?
- UPnP
- MAC filtering
- NAT
- QoS
Explanation: Network Address Translation (NAT) is the process used to convert private addresses to internet-routable addresses that allow office devices to access the internet.
20. A data center has recently updated a physical server to host multiple operating systems on a single CPU. The data center can now provide each customer with a separate web server without having to allocate an actual discrete server for each customer. What is the networking trend that is being implemented by the data center in this situation?
- online collaboration
- BYOD
- virtualization
- maintaining communication integrity
21. Refer to the exhibit. Which address or addresses represent the inside global address?
- 192.168.0.100
- 10.1.1.2
- any address in the 10.1.1.0 network
- 209.165.20.25
22. Which two IPsec protocols are used to provide data integrity?
- MD5
- DH
- AES
- SHA
- RSA
Explanation: The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. Two popular algorithms used to ensure that data is not intercepted and modified (data integrity) are MD5 and SHA. AES is an encryption protocol and provides data confidentiality. DH (Diffie-Hellman) is an algorithm used for key exchange. RSA is an algorithm used for authentication.
23. If an outside host does not have the Cisco AnyConnect client preinstalled, how would the host gain access to the client image?
- The Cisco AnyConnect client is installed by default on most major operating systems.
- The host initiates a clientless VPN connection using a compliant web browser to download the client.
- The host initiates a clientless connection to a TFTP server to download the client.
- The host initiates a clientless connection to an FTP server to download the client.
Explanation: If an outside host does not have the Cisco AnyConnect client preinstalled, the remote user must initiate a clientless SSL VPN connection via a compliant web browser, and then download and install the AnyConnect client on the remote host.
24. A company is considering updating the campus WAN connection. Which two WAN options are examples of the private WAN architecture? (Choose two.)
- leased line
- cable
- digital subscriber line
- Ethernet WAN
- municipal Wi-Fi
25. Which type of QoS marking is applied to Ethernet frames?
- IP precedence
- DSCP
- ToS
- CoS
26. Refer to the exhibit. Routers R1 and R2 are connected via a serial link. One router is configured as the NTP master, and the other is an NTP client. Which two pieces of information can be obtained from the partial output of the show ntp associations detail command on R2? (Choose two.)
- Both routers are configured to use NTPv2.
- Router R1 is the master, and R2 is the client
- The IP address of R2 is 192 168.1.2.
- Router R2 is the master, and R1 is the client
- The IP address of R1 is 192.168.1.2
Explanation: With the show NTP associations command, the IP address of the NTP master is given.
27. Refer to the exhibit. The network administrator that has the IP address of 10.0.70.23/25 needs to have access to the corporate FTP server (10.0.54.5/28). The FTP server is also a web server that is accessible to all internal employees on networks within the 10.x.x.x address. No other traffic should be allowed to this server. Which extended ACL would be used to filter this traffic, and how would this ACL be applied? (Choose two.)
R1(config)# interface s0/0/0
R1(config-if)# ip access-group 105 out
R2(config)# interface gi0/0
R2(config-if)# ip access-group 105 in
access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 20
access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 21
access-list 105 permit tcp 10.0.0.0 0.255.255.255 host 10.0.54.5 eq www
access-list 105 deny ip any host 10.0.54.5
access-list 105 permit ip any any
access-list 105 permit ip host 10.0.70.23 host 10.0.54.5
access-list 105 permit tcp any host 10.0.54.5 eq www
access-list 105 permit ip any any
R1(config)# interface gi0/0
R1(config-if)# ip access-group 105 out
access-list 105 permit tcp host 10.0.54.5 any eq www
access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 20
access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 21
Explanation: The first two lines of the ACL allow host 10.0.70.23 FTP access to the server that has the IP address of 10.0.54.5. The next line of the ACL allows HTTP access to the server from any host that has an IP address that starts with the number 10. The fourth line of the ACL denies any other type of traffic to the server from any source IP address. The last line of the ACL permits anything else in case there are other servers or devices added to the 10.0.54.0/28 network. Because traffic is being filtered from all other locations and for the 10.0.70.23 host device, the best place to put this ACL is closest to the server.
28. Refer to the exhibit. If the network administrator created a standard ACL that allows only devices that connect to the R2 G0/0 network access to the devices on the R1 G0/1 interface, how should the ACL be applied?
- inbound on the R2 G0/0 interface
- outbound on the R1 G0/1 interface
- inbound on the R1 G0/1 interface
- outbound on the R2 S0/0/1 interface
Explanation: Because standard access lists only filter on the source IP address, they are commonly placed closest to the destination network. In this example, the source packets will be coming from the R2 G0/0 network. The destination is the R1 G0/1 network. The proper ACL placement is outbound on the R1 G0/1 interface.
29. Which is a characteristic of a Type 2 hypervisor?
- does not require management console software
- has direct access to server hardware resources
- best suited for enterprise environments
- installs directly on hardware
30. What are the two types of VPN connections? (Choose two.)
- PPPoE
- Frame Relay
- site-to-site
- remote access
- leased line
Explanation: PPPoE, leased lines, and Frame Relay are types of WAN technology, not types of VPN connections.
31. Refer to the exhibit. What three conclusions can be drawn from the displayed output? (Choose three.)
- The DR can be reached through the GigabitEthernet 0/0 interface.
- There have been 9 seconds since the last hello packet sent.
- This interface is using the default priority.
- The router ID values were not the criteria used to select the DR and the BDR.
- The router ID on the DR router is 3.3.3.3
- The BDR has three neighbors.
32. Refer to the exhibit. A network administrator is configuring an ACL to limit the connection to R1 vty lines to only the IT group workstations in the network 192.168.22.0/28. The administrator verifies the successful Telnet connections from a workstation with IP 192.168.22.5 to R1 before the ACL is applied. However, after the ACL is applied to the interface Fa0/0, Telnet connections are denied. What is the cause of the connection failure?
- The enable secret password is not configured on R1.
- The IT group network is included in the deny statement.
- The permit ACE specifies a wrong port number.
- The permit ACE should specify protocol ip instead of tcp.
- The login command has not been entered for vty lines.
Explanation: The source IP range in the deny ACE is 192.168.20.0 0.0.3.255, which covers IP addresses from 192.168.20.0 to 192.168.23.255. The IT group network 192.168.22.0/28 is included in the 192.168.20/22 network. Therefore, the connection is denied. To fix it, the order of the deny and permit ACE should be switched.
33. What functionality does mGRE provide to the DMVPN technology?
- It allows the creation of dynamically allocated tunnels through a permanent tunnel source at the hub and dynamically allocated tunnel destinations at the spokes.
- It provides secure transport of private information over public networks, such as the Internet.
- It is a Cisco software solution for building multiple VPNs in an easy, dynamic, and scalable manner.
- It creates a distributed mapping database of public IP addresses for all VPN tunnel spokes.
Explanation: DMVPN is built on three protocols, NHRP, IPsec, and mGRE. NHRP is the distributed address mapping protocol for VPN tunnels. IPsec encrypts communications on VPN tunnels. The mGRE protocol allows the dynamic creation of multiple spoke tunnels from one permanent VPN hub.
34. What is used to pre-populate the adjacency table on Cisco devices that use CEF to process packets?
- the FIB
- the routing table
- the ARP table
- the DSP
35. What command would be used as part of configuring NAT or PAT to display information about NAT configuration parameters and the number of addresses in the pool?
- show running-config
- show ip nat statistics
- show ip cache
- show version
36. What is a purpose of establishing a network baseline?
- It provides a statistical average for network performance.
- It creates a point of reference for future network evaluations.
- It manages the performance of network devices.
- It checks the security configuration of network devices.
Explanation: A baseline is used to establish normal network or system performance. It can be used to compare with future network or system performances in order to detect abnormal situations.
37. Match the type of WAN device or service to the description. (Not all options are used.)
CPE —> devices and inside wiring that are located on the enterprise edge and connect to a carrier link
DCE —> devices that provide an interface for customers to connect to within the WAN cloud
DTE —> customer devices that pass the data from a customer network for transmission over the WAN
local loop —> a physical connection from the customer to the service provider POP
38. Which statement describes a characteristic of standard IPv4 ACLs?
- They filter traffic based on source IP addresses only.
- They can be created with a number but not with a name.
- They are configured in the interface configuration mode.
- They can be configured to filter traffic based on both source IP addresses and source ports.
39. Refer to the exhibit. R1 is configured for NAT as displayed. What is wrong with the configuration?
- NAT-POOL2 is not bound to ACL 1.
- Interface Fa0/0 should be identified as an outside NAT interface.
- The NAT pool is incorrect.
- Access-list 1 is misconfigured.
Explanation: R1 has to have NAT-POOL2 bound to ACL 1. This is accomplished with the command R1(config)#ip nat inside source list 1 pool NAT-POOL2. This would enable the router to check for all interesting traffic and if it matches ACL 1 it would be translated by use of the addresses in NAT-POOL2.
40. Refer to the exhibit. What method can be used to enable an OSPF router to advertise a default route to neighboring OSPF routers?
- Use a static route pointing to the ISP and redistribute it.
- Use the redistribute static command on R0-A.
- Use the default-information originate command on ISP.
- Use the default-information originate command on R0-A.
41. A company has contracted with a network security firm to help identify the vulnerabilities of the corporate network. The firm sends a team to perform penetration tests to the company network. Why would the team use applications such as John the Ripper,THC Hydra, RainbowCrack, and Medusa?
- to capture and analyze packets within traditional Ethernet LANs or WLANs
- to probe and test the robustness of a firewall by using specially created forged packets
- to make repeated guesses in order to crack a password
42. What are two syntax rules for writing a JSON array? (Choose two.)
- Each value in the array is separated by a comma.
- The array can include only one value type.
- A space must separate each value in the array.
- A semicolon separates the key and list of values.
- Values are enclosed in square brackets.
43. What is a characteristic of a Trojan horse as it relates to network security?
- An electronic dictionary is used to obtain a password to be used to infiltrate a key network device.
- Malware is contained in a seemingly legitimate executable program.
- Extreme quantities of data are sent to a particular network device interface.
- Too much information is destined for a particular memory block, causing additional memory areas to be affecte
Explanation: A Trojan horse carries out malicious operations under the guise of a legitimate program. Denial of service attacks send extreme quantities of data to a particular host or network device interface. Password attacks use electronic dictionaries in an attempt to learn passwords. Buffer overflow attacks exploit memory buffers by sending too much information to a host to render the system inoperable.
44. An attacker is redirecting traffic to a false default gateway in an attempt to intercept the data traffic of a switched network. What type of attack could achieve this?
- TCP SYN flood
- DNS tunneling
- DHCP spoofing
- ARP cache poisoning
Explanation: In DHCP spoofing attacks, an attacker configures a fake DHCP server on the network to issue DHCP addresses to clients with the aim of forcing the clients to use a false default gateway, and other false services. DHCP snooping is a Cisco switch feature that can mitigate DHCP attacks. MAC address starvation and MAC address snooping are not recognized security attacks. MAC address spoofing is a network security threat.
45. A company is developing a security policy for secure communication. In the exchange of critical messages between a headquarters office and a branch office, a hash value should only be recalculated with a predetermined code, thus ensuring the validity of data source. Which aspect of secure communications is addressed?
- data integrity
- non-repudiation
- origin authentication
- data confidentiality
Explanation: Secure communications consists of four elements:
Data confidentiality – guarantees that only authorized users can read the message
Data integrity – guarantees that the message was not altered
Origin authentication – guarantees that the message is not a forgery and does actually come from whom it states
Data nonrepudiation – guarantees that the sender cannot repudiate, or refute, the validity of a message sent
46. A company has contracted with a network security firm to help identify the vulnerabilities of the corporate network. The firm sends a team to perform penetration tests to the company network. Why would the team use packet sniffers?
- to detect installed tools within files and directories that provide threat actors remote access and control over a computer or network
- to detect any evidence of a hack or malware in a computer or network
- to probe and test the robustness of a firewall by using specially created forged packets
- to capture and analyze packets within traditional Ethernet LANs or WLANs
47. An administrator is configuring single-area OSPF on a router. One of the networks that must be advertised is 172.20.0.0 255.255.252.0. What wildcard mask would the administrator use in the OSPF network statement?
- 0.0.15.255
- 0.0.3.255
- 0.0.7.255
- 0.0.1.255
48. Match the HTTP method with the RESTful operation.
POST –>> Create
GET –>> Read
PUT/PATCH –>> Update/Replace?Modify
Delete –>> Delete
49. Refer to the exhibit. What is the OSPF cost to reach the West LAN 172.16.2.0/24 from East?
- 782
- 74
- 128
- 65
50. What is one reason to use the ip ospf priority command when the OSPF routing protocol is in use?
- to activate the OSPF neighboring process
- to influence the DR/BDR election process
- to provide a backdoor for connectivity during the convergence process
- to streamline and speed up the convergence process
51. An ACL is applied inbound on a router interface. The ACL consists of a single entry:
access-list 210 permit tcp 172.18.20.0 0.0.0.31 172.18.20.32 0.0.0.31 eq ftp .
If a packet with a source address of 172.18.20.14, a destination address of 172.18.20.40, and a protocol of 21 is received on the interface, is the packet permitted or denied?
- permitted
52. What is a characteristic of the two-tier spine-leaf topology of the Cisco ACI fabric architecture?
- The spine and leaf switches are always linked through core switches.
- The spine switches attach to the leaf switches and attach to each other for redundancy.
- The leaf switches always attach to the spines and they are interlinked through a trunk line.
- The leaf switches always attach to the spines, but they never attach to each other.
53. Which two scenarios would result in a duplex mismatch? (Choose two.)
- connecting a device with autonegotiation to another that is manually set to full-duplex
- starting and stopping a router interface during a normal operation
- connecting a device with an interface running at 100 Mbps to another with an interface running at 1000 Mbps
- configuring dynamic routing incorrectly
- manually setting the two connected devices to different duplex modes
54. A network technician is configuring SNMPv3 and has set a security level of auth . What is the effect of this setting?
- authenticates a packet by a string match of the username or community string
- authenticates a packet by using either the HMAC with MD5 method or the SHA method
- authenticates a packet by using either the HMAC MD5 or 3.HMAC SHA algorithms and encrypts the packet with either the DES, 3DES or AES algorithms
- authenticates a packet by using the SHA algorithm only
Explanation: For enabling SNMPv3 one of three security levels can be configured:
1) noAuth
2) auth
3) priv
The security level configured determines which security algorithms are performed on SNMP packets. The auth security level uses either HMAC with MD5 or SHA.
55. What are two types of attacks used on DNS open resolvers? (Choose two.)
- amplification and reflection
- resource utilization
- fast flux
- ARP poisoning
- cushioning
Explanation: Three types of attacks used on DNS open resolvers are as follows:DNS cache poisoning – attacker sends spoofed falsified information to redirect users from legitimate sites to malicious sites
DNS amplification and reflection attacks – attacker sends an increased volume of attacks to mask the true source of the attack
DNS resource utilization attacks – a denial of service (DoS) attack that consumes server resources
56. An ACL is applied inbound on a router interface. The ACL consists of a single entry:
access-list 101 permit udp 192.168.100.0 0.0.2.255 64.100.40.0 0.0.0.15 eq telnet .
If a packet with a source address of 192.168.101.45, a destination address of 64.100.40.4, and a protocol of 23 is received on the interface, is the packet permitted or denied?
- denied
- permitted
Case 2:
access-list 101 permit udp 192.168.100.0 0.0.2.255 64.100.40.0 0.0.0.0.15 eq telnet .
If a packet with a source address of 192.168.100.219, a destination address of 64.100.40.10, and a protocol of 54 is received on the interface, is the packet permitted or denied?
- denied
- permitted
57. Which type of resources are required for a Type 1 hypervisor?
- a dedicated VLAN
- a management console
- a host operating system
58. In JSON, what is held within square brackets [ ]?
- nested values
- key/value pairs
- an object
- an array
59. What are three components used in the query portion of a typical RESTful API request? (Choose three.)
- resources
- protocol
- API server
- format
- key
- parameters
60. A user reports that when the corporate web page URL is entered on a web browser, an error message indicates that the page cannot be displayed. The help-desk technician asks the user to enter the IP address of the web server to see if the page can be displayed. Which troubleshooting method is being used by the technician?
- top-down
- bottom-up
- divide-and-conquer
- substitution
61. Which protocol provides authentication, integrity, and confidentiality services and is a type of VPN?
- MD5
- AES
- IPsec
- ESP
62. Which statement describes a characteristic of Cisco Catalyst 2960 switches?
- They are best used as distribution layer switches.
- New Cisco Catalyst 2960-C switches support PoE pass-through.
- They are modular switches.
- They do not support an active switched virtual interface (SVI) with IOS versions prior to 15.x.
63. Which component of the ACI architecture translates application policies into network programming?
- the hypervisor
- the Application Policy Infrastructure Controller
- the Nexus 9000 switch
- the Application Network Profile endpoints
64. Which two pieces of information should be included in a logical topology diagram of a network? (Choose two.)
- device type
- cable specification
- interface identifier
- OS/IOS version
- connection type
- cable type and identifier
65. Refer to the exhibit. A PC at address 10.1.1.45 is unable to access the Internet. What is the most likely cause of the problem?
- The NAT pool has been exhausted.
- The wrong netmask was used on the NAT pool.
- Access-list 1 has not been configured properly.
- The inside and outside interfaces have been configured backwards.
Explanation: The output of show ip nat statistics shows that there are 2 total addresses and that 2 addresses have been allocated (100%). This indicates that the NAT pool is out of global addresses to give new clients. Based on the show ip nat translations, PCs at 10.1.1.33 and 10.1.1.123 have used the two available addresses to send ICMP messages to a host on the outside network.
66. What are two benefits of using SNMP traps? (Choose two.)
- They eliminate the need for some periodic polling requests.
- They reduce the load on network and agent resources.
- They limit access for management systems only.
- They can provide statistics on TCP/IP packets that flow through Cisco devices.
- They can passively listen for exported NetFlow datagrams.
67. Which statement accurately describes a characteristic of IPsec?
- IPsec works at the application layer and protects all application data.
- IPsec is a framework of standards developed by Cisco that relies on OSI algorithms.
- IPsec is a framework of proprietary standards that depend on Cisco specific algorithms.
- IPsec works at the transport layer and protects data at the network layer.
- IPsec is a framework of open standards that relies on existing algorithms.
Explanation: IPsec can secure a path between two network devices. IPsec can provide the following security functions:
Confidentiality – IPsec ensures confidentiality by using encryption.
Integrity – IPsec ensures that data arrives unchanged at the destination using a hash algorithm, such as MD5 or SHA.
Authentication – IPsec uses Internet Key Exchange (IKE) to authenticate users and devices that can carry out communication independently. IKE uses several types of authentication, including username and password, one-time password, biometrics, pre-shared keys (PSKs), and digital certificates.
Secure key exchange- IPsec uses the Diffie-Hellman (DH) algorithm to provide a public key exchange method for two peers to establish a shared secret key.
68. In a large enterprise network, which two functions are performed by routers at the distribution layer? (Choose two.)
- connect users to the network
- provide a high-speed network backbone
- connect remote networks
- provide Power over Ethernet to devices
- provide data traffic security
69. Which two statements describe the use of asymmetric algorithms? (Choose two.)
- Public and private keys may be used interchangeably.
- If a public key is used to encrypt the data, a public key must be used to decrypt the data.
- If a private key is used to encrypt the data, a public key must be used to decrypt the data.
- If a public key is used to encrypt the data, a private key must be used to decrypt the data.
- If a private key is used to encrypt the data, a private key must be used to decrypt the data.
Explanation: Asymmetric algorithms use two keys: a public key and a private key. Both keys are capable of the encryption process, but the complementary matched key is required for decryption. If a public key encrypts the data, the matching private key decrypts the data. The opposite is also true. If a private key encrypts the data, the corresponding public key decrypts the data.
70. Refer to the exhibit. A network administrator has deployed QoS and has configured the network to mark traffic on the VoIP phones as well as the Layer 2 and Layer 3 switches. Where should initial marking occur to establish the trust boundary?
- Trust Boundary 4
- Trust Boundary 3
- Trust Boundary 1
- Trust Boundary 2
Explanation: Traffic should be classified and marked as close to its source as possible. The trust boundary identifies at which device marked traffic should be trusted. Traffic marked on VoIP phones would be considered trusted as it moves into the enterprise network.
71. What are two benefits of extending access layer connectivity to users through a wireless medium? (Choose two.)
- reduced costs
- decreased number of critical points of failure
- increased flexibility
- increased bandwidth availability
- increased network management options
72. What are two purposes of launching a reconnaissance attack on a network? (Choose two.)
- to scan for accessibility
- to retrieve and modify data
- to gather information about the network and devices
- to prevent other users from accessing the system
- to escalate access privileges
73. A group of users on the same network are all complaining about their computers running slowly. After investigating, the technician determines that these computers are part of a zombie network. Which type of malware is used to control these computers?
- botnet
- spyware
- virus
- rootkit
74. An ACL is applied inbound on a router interface. The ACL consists of a single entry:
access-list 101 permit tcp 10.1.1.0 0.0.0.255 host 192.31.7.45 eq dns .
If a packet with a source address of 10.1.1.201, a destination address of 192.31.7.45, and a protocol of 23 is received on the interface, is the packet permitted or denied?
- permitted
- denied
75. Refer to the exhibit. From which location did this router load the IOS?
- flash memory
- NVRAM?
- RAM
- ROM
- a TFTP server?
76. Refer to the exhibit. Which data format is used to represent the data for network automation applications?
- XML
- YAML
- HTML
- JSON
Explanation: The common data formats that are used in many applications including network automation and programmability are as follows:
- JavaScript Object Notation (JSON) – In JSON, the data known as an object is one or more key/value pairs enclosed in braces { }. Keys must be strings within double quotation marks ” “. Keys and values are separated by a colon.
- eXtensible Markup Language (XML) – In XML, the data is enclosed within a related set of tags data.
- YAML Ain’t Markup Language (YAML) – In YAML, the data known as an object is one or more key value pairs. Key value pairs are separated by a colon without the use of quotation marks. YAML uses indentation to define its structure, without the use of brackets or commas.
77. What QoS step must occur before packets can be marked?
- classifying
- shaping
- queuing
- policing
78. What is the main function of a hypervisor?
- It is used to create and manage multiple VM instances on a host machine.
- It is a device that filters and checks security credentials.
- It is a device that synchronizes a group of sensors.
- It is software used to coordinate and prepare data for analysis.
- It is used by ISPs to monitor cloud computing resources.
79. A company needs to interconnect several branch offices across a metropolitan area. The network engineer is seeking a solution that provides high-speed converged traffic, including voice, video, and data on the same network infrastructure. The company also wants easy integration to their existing LAN infrastructure in their office locations. Which technology should be recommended?
- Frame Relay
- Ethernet WAN
- VSAT
- ISDN
80. Refer to the exhibit. As traffic is forwarded out an egress interface with QoS treatment, which congestion avoidance technique is used?
- traffic shaping
- weighted random early detection
- classification and marking
- traffic policing
Explanation: Traffic shaping buffers excess packets in a queue and then forwards the traffic over increments of time, which creates a smoothed packet output rate. Traffic policing drops traffic when the amount of traffic reaches a configured maximum rate, which creates an output rate that appears as a saw-tooth with crests and troughs.
81. An ACL is applied inbound on a router interface. The ACL consists of a single entry:
access-list 101 permit tcp 10.1.1.0 0.0.0.255 host 10.1.3.8 eq dns .
If a packet with a source address of 10.1.3.8, a destination address of 10.10.3.8, and a protocol of 53 is received on the interface, is the packet permitted or denied?
- denied
- permitted
82. Refer to the exhibit. What is the purpose of the command marked with an arrow shown in the partial configuration output of a Cisco broadband router?
- defines which addresses are allowed into the router
- defines which addresses can be translated
- defines which addresses are assigned to a NAT pool
- defines which addresses are allowed out of the router
83. If a router has two interfaces and is routing both IPv4 and IPv6 traffic, how many ACLs could be created and applied to it?
- 12
- 4
- 8
- 16
- 6
84. Refer to the exhibit. An administrator first configured an extended ACL as shown by the output of the show access-lists command. The administrator then edited this access-list by issuing the commands below.
Router(config)# ip access-list extended 101 Router(config-ext-nacl)# no 20 Router(config-ext-nacl)# 5 permit tcp any any eq 22 Router(config-ext-nacl)# 20 deny udp any any
Which two conclusions can be drawn from this new configuration? (Choose two.)
- TFTP packets will be permitted.
- Ping packets will be permitted.
- Telnet packets will be permitted.
- SSH packets will be permitted.
- All TCP and UDP packets will be denied.
Explanation: After the editing, the final configuration is as follows:
Router# show access-lists
Extended IP access list 101
5 permit tcp any any eq ssh
10 deny tcp any any
20 deny udp any any
30 permit icmp any any
So, only SSH packets and ICMP packets will be permitted.
85. Which troubleshooting approach is more appropriate for a seasoned network administrator rather than a less-experienced network administrator?
- a less-structured approach based on an educated guess
- an approach comparing working and nonworking components to spot significant differences
- a structured approach starting with the physical layer and moving up through the layers of the OSI model until the cause of the problem is identified
- an approach that starts with the end-user applications and moves down through the layers of the OSI model until the cause of the problem has been identified
86. Refer to the exhibit. Many employees are wasting company time accessing social media on their work computers. The company wants to stop this access. What is the best ACL type and placement to use in this situation?
- extended ACL outbound on R2 WAN interface towards the internet
- standard ACL outbound on R2 WAN interface towards the internet
- standard ACL outbound on R2 S0/0/0
- extended ACLs inbound on R1 G0/0 and G0/1
87. Refer to the exhibit. An administrator is trying to configure PAT on R1, but PC-A is unable to access the Internet. The administrator tries to ping a server on the Internet from PC-A and collects the debugs that are shown in the exhibit. Based on this output, what is most likely the cause of the problem?
- The inside and outside NAT interlaces have been configured backwards
- The inside global address is not on the same subnet as the ISP
- The address on Fa0/0 should be 64.100.0.1.
- The NAT source access list matches the wrong address range.
Explanation: The output of debug ip nat shows each packet that is translated by the router. The “s” is the source IP address of the packet and the “d” is the destination. The address after the arrow (“->”) shows the translated address. In this case, the translated address is on the 209.165.201.0 subnet but the ISP facing interface is in the 209.165.200.224/27 subnet. The ISP may drop the incoming packets, or might be unable to route the return packets back to the host because the address is in an unknown subnet.
88. Why is QoS an important issue in a converged network that combines voice, video, and data communications?
- Data communications must be given the first priority.
- Voice and video communications are more sensitive to latency.
- Legacy equipment is unable to transmit voice and video without QoS.
- Data communications are sensitive to jitter.
89. Which statement describes a VPN?
- VPNs use logical connections to create public networks through the Internet.
- VPNs use open source virtualization software to create the tunnel through the Internet.
- VPNs use dedicated physical connections to transfer data between remote users.
- VPNs use virtual connections to create a private network through a public network.
90. In which OSPF state is the DR/BDR election conducted?
- ExStart
- Init
- Two-Way
- Exchange
91. Two corporations have just completed a merger. The network engineer has been asked to connect the two corporate networks without the expense of leased lines. Which solution would be the most cost effective method of providing a proper and secure connection between the two corporate networks?
- Cisco Secure Mobility Clientless SSL VPN
- Frame Relay
- remote access VPN using IPsec
- Cisco AnyConnect Secure Mobility Client with SSL
- site-to-site VPN
Explanation: The site-to-site VPN is an extension of a classic WAN network that provides a static interconnection of entire networks. Frame Relay would be a better choice than leased lines, but would be more expensive than implementing site-to-site VPNs. The other options refer to remote access VPNs which are better suited for connecting users to the corporate network versus interconnecting two or more networks.
92. What is the final operational state that will form between an OSPF DR and a DROTHER once the routers reach convergence?
- loading
- established
- full
- two-way
93. Refer to the exhibit. If the switch reboots and all routers have to re-establish OSPF adjacencies, which routers will become the new DR and BDR?
- Router R3 will become the DR and router R1 will become the BDR.
- Router R4 will become the DR and router R3 will become the BDR.
- Router R1 will become the DR and router R2 will become the BDR.
- Router R3 will become the DR and router R2 will become the BDR.
Explanation: OSPF elections of a DR are based on the following in order of precedence:
- highest pritority from 1 -255 (0 = never a DR)
- highest router ID
- highest IP address of a loopback or active interface in the absence of a manually configured router ID. Loopback IP addresses take higher precedence than other interfaces.
In this case routers R3 and R1 have the highest router priority. Between the two, R3 has the higher router ID. Therefore, R3 will become the DR and R1 will become the BDR.
94. Which type of server would be used to keep a historical record of messages from monitored network devices?
- DNS
- DHCP
- syslog
- authentication
95. When QoS is implemented in a converged network, which two factors can be controlled to improve network performance for real-time traffic? (Choose two.)
- packet addressing
- delay
- jitter
- packet routing
- link speed
Explanation: Delay is the latency between a sending and receiving device. Jitter is the variation in the delay of the received packets. Both delay and jitter need to be controlled in order to support real-time voice and video traffic.
96. In which step of gathering symptoms does the network engineer determine if the problem is at the core, distribution, or access layer of the network?
- Determine ownership.
- Determine the symptoms.
- Narrow the scope.
- Document the symptoms.
- Gather information.
97. What protocol sends periodic advertisements between connected Cisco devices in order to learn device name, IOS version, and the number and type of interfaces?
- CDP
- SNMP
- NTP
- LLDP
98. An administrator is configuring single-area OSPF on a router. One of the networks that must be advertised is 192.168.0.0 255.255.252.0. What wildcard mask would the administrator use in the OSPF network statement?
- 0.0.0.127
- 0.0.0.31
- 0.0.3.255
- 0.0.0.63
99. Refer to the exhibit. An administrator configures the following ACL in order to prevent devices on the 192.168.1.0 subnet from accessing the server at 10.1.1.5:
access-list 100 deny ip 192.168.1.0 0.0.0.255 host 10.1.1.5 access-list 100 permit ip any any
Where should the administrator place this ACL for the most efficient use of network resources?
- inbound on router A Fa0/0
- outbound on router B Fa0/0
- outbound on router A Fa0/1
- inbound on router B Fa0/1
100. Which type of OSPFv2 packet is used to forward OSPF link change information?
- link-state acknowledgment
- link-state update
- hello
- database description
101. What protocol synchronizes with a private master clock or with a publicly available server on the internet?
- MPLS
- CBWFQ
- TFTP
- NTP
102. Which type of VPN allows multicast and broadcast traffic over a secure site-to-site VPN?
- dynamic multipoint VPN
- SSL VPN
- IPsec virtual tunnel interface
- GRE over IPsec
103. An OSPF router has three directly connected networks; 10.0.0.0/16, 10.1.0.0/16, and 10.2.0.0/16. Which OSPF network command would advertise only the 10.1.0.0 network to neighbors?
- router(config-router)# network 10.1.0.0 0.0.255.255 area 0
- router(config-router)# network 10.1.0.0 0.0.15.255 area 0
- router(config-router)# network 10.1.0.0 255.255.255.0 area 0
- router(config-router)# network 10.1.0.0 0.0.0.0 area 0
104. Refer to the exhibit. Which sequence of commands should be used to configure router A for OSPF?
router ospf 1
network 192.168.10.0 area 0
router ospf 1
network 192.168.10.0
router ospf 1
network 192.168.10.64 255.255.255.192
network 192.168.10.192 255.255.255.252
router ospf 1
network 192.168.10.64 0.0.0.63 area 0
network 192.168.10.192 0.0.0.3 area 0
105. An administrator is configuring single-area OSPF on a router. One of the networks that must be advertised is 192.168.0.0 255.255.254.0. What wildcard mask would the administrator use in the OSPF network statement?
- 0.0.7.255
- 0.0.1.255
- 0.0.3.255
- 0.0.15.255
106. How does virtualization help with disaster recovery within a data center?
- improvement of business practices
- supply of consistent air flow
- support of live migration
- guarantee of power
Explanation: Live migration allows moving of one virtual server to another virtual server that could be in a different location that is some distance from the original data center.
Case 2:
- Less energy is consumed.
- Server provisioning is faster.
- Hardware at the recovery site does not have to be identical to production equipment.
- Power is always provided.
Explanation: Improved disaster recovery – Virtualization offers advanced business continuity solutions. It provides hardware abstraction capability so that the recovery site no longer needs to have hardware that is identical to the hardware in the production environment. Most enterprise server virtualization platforms also have software that can help test and automate the failover before a disaster does happen.
107. How does virtualization help with disaster recovery within a data center?
- Hardware does not have to be identical.
- (Other case) Hardware at the recovery site does not have to be identical to production equipment.
- Power is always provided.
- Less energy is consumed.
- Server provisioning is faster.
Explanation: Disaster recovery is how a company goes about accessing applications, data, and the hardware that might be affected during a disaster. Virtualization provides hardware independence which means the disaster recovery site does not have to have the exact equipment as the equipment in production. Server provisioning is relevant when a server is built for the first time. Although data centers do have backup generators, the entire data center is designed for disaster recovery. One particular data center could never guarantee that the data center itself would never be without power.
108. Refer to the exhibit. Which devices exist in the failure domain when switch S3 loses power?
- S4 and PC_2
- PC_3 and AP_2
- AP_2 and AP_1
- PC_3 and PC_2
- S1 and S4
A failure domain is the area of a network that is impacted when a critical device such as switch S3 has a failure or experiences problems.
109. Which set of access control entries would allow all users on the 192.168.10.0/24 network to access a web server that is located at 172.17.80.1, but would not allow them to use Telnet?
access-list 103 deny tcp host 192.168.10.0 any eq 23
access-list 103 permit tcp host 192.168.10.1 eq 80
access-list 103 permit tcp 192.168.10.0 0.0.0.255 host 172.17.80.1 eq 80
access-list 103 deny tcp 192.168.10.0 0.0.0.255 any eq 23
access-list 103 permit tcp 192.168.10.0 0.0.0.255 any eq 80
access-list 103 deny tcp 192.168.10.0 0.0.0.255 any eq 23
access-list 103 permit 192.168.10.0 0.0.0.255 host 172.17.80.1
access-list 103 deny tcp 192.168.10.0 0.0.0.255 any eq telnet
For an extended ACL to meet these requirements the following need to be included in the access control entries:
identification number in the range 100-199 or 2000-2699
permit or deny parameter
protocol
source address and wildcard
destination address and wildcard
port number or name
110. Refer to the exhibit. A network administrator needs to add an ACE to the TRAFFIC-CONTROL ACL that will deny IP traffic from the subnet 172.23.16.0/20. Which ACE will meet this requirement?
- 5 deny 172.23.16.0 0.0.15.255
- 5 deny 172.23.16.0 0.0.255.255
- 15 deny 172.23.16.0 0.0.15.255
- 30 deny 172.23.16.0 0.0.15.255
111. Which step in the link-state routing process is described by a router building a link-state database based on received LSAs?
- executing the SPF algorithm
- building the topology table
- selecting the router ID
- declaring a neighbor to be inaccessible
112. What protocol uses agents, that reside on managed devices, to collect and store information about the device and its operation?
- SYSLOG
- TFTP
- CBWFQ
- SNMP
113. An administrator is configuring single-area OSPF on a router. One of the networks that must be advertised is 10.27.27.0 255.255.255.0. What wildcard mask would the administrator use in the OSPF network statement?
- 0.0.0.63
- 0.0.0.255
- 0.0.0.31
- 0.0.0.15
114. When will an OSPF-enabled router transition from the Down state to the Init state?
- when an OSPF-enabled interface becomes active
- as soon as the router starts
- when the router receives a hello packet from a neighbor router
- as soon as the DR/BDR election process is complete
115. What type of traffic is described as having a high volume of data per packet?
- data
- video
- voice
116. What protocol is a vendor-neutral Layer 2 protocol that advertises the identity and capabilities of the host device to other connected network devices?
- LLDP
- NTP
- TFTP
- SNMP
117. Which step in the link-state routing process is described by a router running an algorithm to determine the best path to each destination?
- building the topology table
- selecting the router ID
- declaring a neighbor to be inaccessible
- executing the SPF algorithm
118. Refer to the exhibit. Which conclusion can be drawn from this OSPF multiaccess network?
- If the DR stops producing Hello packets, a BDR will be elected, and then it promotes itself to assume the role of DR.
- With an election of the DR, the number of adjacencies is reduced from 6 to 3.
- When a DR is elected all other non-DR routers become DROTHER.
- All DROTHER routers will send LSAs to the DR and BDR to multicast 224.0.0.5.
On OSPF multiaccess networks, a DR is elected to be the collection and distribution point for LSAs sent and received. A BDR is also elected in case the DR fails. All other non-DR or BDR routers become DROTHER. Instead of flooding LSAs to all routers in the network, DROTHERs only send their LSAs to the DR and BDR using the multicast address 224.0.0.6. If there is no DR/BDR election, the number of required adjacencies is n(n-1)/2 = > 4(4-1)/2 = 6. With the election, this number is reduced to 3.
119. Refer to the exhibit. The network administrator has an IP address of 192.168.11.10 and needs access to manage R1. What is the best ACL type and placement to use in this situation?
- extended ACL outbound on R2 WAN interface towards the internet
- standard ACL inbound on R1 vty lines
- extended ACLs inbound on R1 G0/0 and G0/1
- extended ACL outbound on R2 S0/0/1
Explanation: Standard ACLs permit or deny packets based only on the source IPv4 address. Because all traffic types are permitted or denied, standard ACLs should be located as close to the destination as possible.
Extended ACLs permit or deny packets based on the source IPv4 address and destination IPv4 address, protocol type, source and destination TCP or UDP ports and more. Because the filtering of extended ACLs is so specific, extended ACLs should be located as close as possible to the source of the traffic to be filtered. Undesirable traffic is denied close to the source network without crossing the network infrastructure.
120. Which type of VPN connects using the Transport Layer Security (TLS) feature?
- SSL VPN
- IPsec virtual tunnel interface
- GRE over IPsec
- dynamic multipoint VPN
121. Which group of APIs are used by an SDN controller to communicate with various applications?
- eastbound APIs
- westbound APIs
- northbound APIs
- southbound APIs
122. A company has consolidated a number of servers and it is looking for a program or firmware to create and control virtual machines which have access to all the hardware of the consolidated servers. What service or technology would support this requirement?
- Cisco ACI
- software defined networking
- Type-1 hypervisor
- APIC-EM
123. What command would be used as part of configuring NAT or PAT to identify inside local addresses that are to be translated?
- ip nat inside source list 24 interface serial 0/1/0 overload
- ip nat inside source list 14 pool POOL-STAT overload
- access-list 10 permit 172.19.89.0 0.0.0.255
- ip nat inside source list ACCTNG pool POOL-STAT
124. Anycompany has decided to reduce its environmental footprint by reducing energy costs, moving to a smaller facility, and promoting telecommuting, what service or technology would support requirement?
- -Cloud services
- Data center
- APIC-EM
- Cisco ACI
125. Refer to the exhibit. An administrator is trying to back up the current running configuration of the router to a USB drive, and enters the command copy usbflash0:/R1-config running-config on the router command line. After removing the USB drive and connecting it to a PC, the administrator discovers that the running configuration was not properly backed up to the R1-config file. What is the problem?
- The file already exists on the USB drive and cannot be overwritten.
- The drive was not properly formatted with the FAT16 file system.
- There is no space left on the USB drive.
- The USB drive is not recognized by the router.
- The command that the administrator used was incorrect.
126. Which three types of VPNs are examples of enterprise-managed site-to-site VPNs? (Choose three.)
- Layer 3 MPLS VPN
- IPsec VPN
- Cisco Dynamic Multipoint VPN
- GRE over IPsec VPN
- clientless SSL VPN
- client-based IPsec VPN
127. Refer to the exhibit. Employees on 192.168.11.0/24 work on critically sensitive information and are not allowed access off their network. What is the best ACL type and placement to use in this situation?
- standard ACL inbound on R1 vty lines
- extended ACL inbound on R1 G0/0
- standard ACL inbound on R1 G0/1
- extended ACL inbound on R3 S0/0/1
128. In an OSPF network which two statements describe the link-state database (LSDB)? (Choose two.)
- It can be viewed by using the
show ip ospf databasecommand. - A neighbor table is created based on the LSDB.
- It contains a list of only the best routes to a particular network.
- It contains a list of all neighbor routers to which a router has established bidirectional communication.
- All routers within an area have an identical link-state database.
129. In an OSPF network which OSPF structure is used to create the neighbor table on a router?
- adjacency database
- link-state database
- routing table
- forwarding database
130. What protocol is used in a system that consists of three elements–a manager, agents, and an information database?
- MPLS
- SYSLOG
- SNMP
- TFTP
131. What type of traffic is described as not resilient to loss?
- data
- video
- voice
Explanation: Video traffic tends to be unpredictable, inconsistent, and bursty compared to voice traffic. Compared to voice, video is less resilient to loss and has a higher volume of data per packet.
132. Refer to the exhibit. Router R1 is configured with static NAT. Addressing on the router and the web server are correctly configured, but there is no connectivity between the web server and users on the Internet. What is a possible reason for this lack of connectivity?
- Interface Fa0/0 should be configured with the command ip nat outside .
- The inside global address is incorrect.
- The router NAT configuration has an incorrect inside local address.
- The NAT configuration on interface S0/0/1 is incorrect.
133. Which type of API would be used to allow authorized salespeople of an organization access to internal sales data from their mobile devices?
- open
- partner
- public
- private
134. Refer to the exhibit. Which data format is used to represent the data for network automation applications?
- XML
- HTML
- YAML
- JSON
135. An ACL is applied inbound on a router interface. The ACL consists of a single entry:
access-list 101 permit udp 192.168.100.32 0.0.0.7 host 198.133.219.76 eq telnet .
If a packet with a source address of 198.133.219.100, a destination address of 198.133.219.170, and a protocol of 23 is received on the interface, is the packet permitted or denied?
- denied
- permitted
136. Refer to the exhibit. If no router ID was manually configured, what would router R1 use as its OSPF router ID?
- 10.0.0.1
- 10.1.0.1
- 192.168.1.100
- 209.165.201.1
137. What protocol is a vendor-neutral Layer 2 protocol that advertises the identity and capabilities of the host device to other connected network devices?
- NTP
- LLDP
- SNMP
- MPLS
138. Which type of VPN uses a hub-and-spoke configuration to establish a full mesh topology?
- MPLS VPN
- GRE over IPsec
- IPsec virtual tunnel interface
- dynamic multipoint VPN
139. What is a characteristic of the REST API?
- evolved into what became SOAP
- used for exchanging XML structured information over HTTP or SMTP
- considered slow, complex, and rigid
- most widely used API for web services
140. Refer to the exhibit. If the switch reboots and all routers have to re-establish OSPF adjacencies, which routers will become the new DR and BDR?
Enterprise Networking, Security, and Automation (Version 7.00) – ENSA Final Exam
- Router R2 will become the DR and router R4 will become the BDR.
- Router R1 will become the DR and router R3 will become the BDR.
- Router R4 will become the DR and router R3 will become the BDR.
- Router R3 will become the DR and router R2 will become the BDR.
141. A student, doing a summer semester of study overseas, has taken hundreds of pictures on a smartphone and wants to back them up in case of loss. What service or technology would support this requirement?
- Cisco ACI
- cloud services
- software defined networking
- dedicated servers
142. Consider the following access list that allows IP phone configuration file transfers from a particular host to a TFTP server:
R1(config)# access-list 105 permit udp host 10.0.70.23 host 10.0.54.5 range 1024 5000 R1(config)# access-list 105 deny ip any any R1(config)# interface gi0/0 R1(config-if)# ip access-group 105 out
Which method would allow the network administrator to modify the ACL and include FTP transfers from any source IP address?
R1(config)# interface gi0/0
R1(config-if)# no ip access-group 105 out
R1(config)# access-list 105 permit tcp any host 10.0.54.5 eq 20
R1(config)# access-list 105 permit tcp any host 10.0.54.5 eq 21
R1(config)# interface gi0/0
R1(config-if)# ip access-group 105 out
R1(config)# access-list 105 permit tcp any host 10.0.54.5 eq 20
R1(config)# access-list 105 permit tcp any host 10.0.54.5 eq 21
R1(config)# interface gi0/0
R1(config-if)# no ip access-group 105 out
R1(config)# no access-list 105
R1(config)# access-list 105 permit udp host 10.0.70.23 host 10.0.54.5 range 1024 5000
R1(config)# access-list 105 permit tcp any host 10.0.54.5 eq 20
R1(config)# access-list 105 permit tcp any host 10.0.54.5 eq 21
R1(config)# access-list 105 deny ip any any
R1(config)# interface gi0/0
R1(config-if)# ip access-group 105 out
R1(config)# access-list 105 permit udp host 10.0.70.23 host 10.0.54.5 range 1024 5000
R1(config)# access-list 105 permit tcp any host 10.0.54.5 eq 20
R1(config)# access-list 105 permit tcp any host 10.0.54.5 eq 21
R1(config)# access-list 105 deny ip any any
143. Which three statements are generally considered to be best practices in the placement of ACLs? (Choose three.)
- Filter unwanted traffic before it travels onto a low-bandwidth link.
- Place standard ACLs close to the destination IP address of the traffic.
- Place standard ACLs close to the source IP address of the traffic.
- Place extended ACLs close to the destination IP address of the traffic.
- Place extended ACLs close to the source IP address of the traffic.
- For every inbound ACL placed on an interface, there should be a matching outbound ACL.
Explanation: Extended ACLs should be placed as close as possible to the source IP address, so that traffic that needs to be filtered does not cross the network and use network resources. Because standard ACLs do not specify a destination address, they should be placed as close to the destination as possible. Placing a standard ACL close to the source may have the effect of filtering all traffic, and limiting services to other hosts. Filtering unwanted traffic before it enters low-bandwidth links preserves bandwidth and supports network functionality. Decisions on placing ACLs inbound or outbound are dependent on the requirements to be met.
144. Match the term to the web link http://www.buycarsfromus.com/2020models/ford/suv.html#Escape component. (Not all options are used.)
Http —-> Protocol
buycarsfromus.com/2020models/ford/suv.html#Escape —-> URN
http://www.buycarsfromus.com/2020models/ford/suv.html —-> URL
http://www.buycarsfromus.com/2020models/ford/suv.html#Escape —-> URI
#Escape —- Fragment
145. What command would be used as part of configuring NAT or PAT to display all static translations that have been configured?
- show ip nat translations
- show ip pat translations
- show ip cache
- show running-config
146. A network administrator modified an OSPF-enabled router to have a hello timer setting of 20 seconds. What is the new dead interval time setting by default?
- 40 seconds
- 60 seconds
- 80 seconds
- 100 seconds
147. Which type of VPN is the preferred choice for support and ease of deployment for remote access?
- SSL VPN
- GRE over IPsec
- dynamic multipoint VPN
- IPsec virtual tunnel interface
148. What type of traffic is described as predictable and smooth?
- video
- data
- voice
149. Which queuing mechanism has no provision for prioritizing or buffering but simply forwards packets in the order they arrive?
- FIFO
- LLQ
- CBWFQ
- WFQ
150. Refer to the exhibit. A network administrator has configured OSPFv2 on the two Cisco routers. The routers are unable to form a neighbor adjacency. What should be done to fix the problem on router R2?
- Implement the command no passive-interface Serial0/1.
- Implement the command network 192.168.2.6 0.0.0.0 area 0 on router R2.
- Change the router-id of router R2 to 2.2.2.2.
- Implement the command network 192.168.3.1 0.0.0.0 area 0 on router R2.
151. A network administrator is troubleshooting an OSPF problem that involves neighbor adjacency. What should the administrator do?
- Make sure that the router priority is unique on each router.
- Make sure that the DR/BDR election is complete.
- Make sure that the router ID is included in the hello packet.
- Make sure that the hello and dead interval timers are the same on all routers.
152. Refer to the exhibit. Internet privileges for an employee have been revoked because of abuse but the employee still needs access to company resources. What is the best ACL type and placement to use in this situation?
CCNA 3 v7 Modules 3 – 5: Network Security Exam Answers 49
- standard ACL inbound on R2 WAN interface connecting to the internet
- standard ACL outbound on R2 WAN interface towards the internet
- standard ACL inbound on R1 G0/0
- standard ACL outbound on R1 G0/0
Explanation: – Standard ACLs permit or deny packets based only on the source IPv4 address. Because all traffic types are permitted or denied, standard ACLs should be located as close to the destination as possible.
– Extended ACLs permit or deny packets based on the source IPv4 address and destination IPv4 address, protocol type, source and destination TCP or UDP ports and more. Because the filtering of extended ACLs is so specific, extended ACLs should be located as close as possible to the source of the traffic to be filtered. Undesirable traffic is denied close to the source network without crossing the network infrastructure.
153. An ACL is applied inbound on a router interface. The ACL consists of a single entry:
access-list 100 permit tcp 192.168.10.0 0.0.0.255 172.17.200.0 0.0.0.255 eq www .
If a packet with a source address of 192.168.10.244, a destination address of 172.17.200.56, and a protocol of 80 is received on the interface, is the packet permitted or denied?
- denied
- permitted
154. A company has contracted with a network security firm to help identify the vulnerabilities of the corporate network. The firm sends a team to perform penetration tests to the company network. Why would the team use applications such as Nmap, SuperScan, and Angry IP Scanner?
- to detect installed tools within files and directories that provide threat actors remote access and control over a computer or network
- to detect any evidence of a hack or malware in a computer or network
- to reverse engineer binary files when writing exploits and when analyzing malware
- to probe network devices, servers, and hosts for open TCP or UDP ports
155. What command would be used as part of configuring NAT or PAT to display any dynamic PAT translations that have been created by traffic?
- show ip pat translations
- show ip cache
- show running-config
- show ip nat translations
156. An administrator is configuring single-area OSPF on a router. One of the networks that must be advertised is 172.16.91.0 255.255.255.192. What wildcard mask would the administrator use in the OSPF network statement?
- 0.0.31.255
- 0.0.0.63
- 0.0.15.255
- 0.0.7.255
157. What type of traffic is described as requiring latency to be no more than 400 milliseconds (ms)?
- video
- data
- voice
158. Refer to the exhibit. Which two configurations would be used to create and apply a standard access list on R1, so that only the 10.0.70.0/25 network devices are allowed to access the internal database server? (Choose two.)
A.
R1(config)# interface GigabitEthernet0/0
R1(config-if)# ip access-group 5 out
B.
R1(config)# access-list 5 permit 10.0.54.0 0.0.1.255
C.
R1(config)# interface Serial0/0/0
R1(config-if)# ip access-group 5 in
D.
R1(config)# access-list 5 permit 10.0.70.0 0.0.0.127
E.
R1(config)# access-list 5 permit any
159. A network administrator is writing a standard ACL that will deny any traffic from the 172.16.0.0/16 network, but permit all other traffic. Which two commands should be used? (Choose two.)
- Router(config)# access-list 95 deny 172.16.0.0 255.255.0.0
- Router(config)# access-list 95 permit any
- Router(config)# access-list 95 host 172.16.0.0
- Router(config)# access-list 95 deny 172.16.0.0 0.0.255.255
- Router(config)# access-list 95 172.16.0.0 255.255.255.255
- Router(config)# access-list 95 deny any
Explanation: To deny traffic from the 172.16.0.0/16 network, the access-list 95 deny 172.16.0.0 0.0.255.255 command is used. To permit all other traffic, the access-list 95 permit any statement is added.
160. Refer to the exhibit. The company has decided that no traffic initiating from any other existing or future network can be transmitted to the Research and Development network. Furthermore, no traffic that originates from the Research and Development network can be transmitted to any other existing or future networks in the company. The network administrator has decided that extended ACLs are better suited for these requirements. Based on the information given, what will the network administrator do?
- One ACL will be placed on the R1 Gi0/0 interface and one ACL will be placed on the R2 Gi0/0 interface.
- Only a numbered ACL will work for this situation.
- One ACL will be placed on the R2 Gi0/0 interface and one ACL will be placed on the R2 S0/0/0 interface.
- Two ACLs (one in each direction) will be placed on the R2 Gi0/0 interface.
161. What protocol uses smaller stratum numbers to indicate that the server is closer to the authorized time source than larger stratum numbers?
- TFTP
- SYSLOG
- NTP
- MPLS
162. Refer to the exhibit. If no router ID was manually configured, what would router Branch1 use as its OSPF router ID?
- 10.0.0.1
- 10.1.0.1
- 192.168.1.100
- 209.165.201.1
Explanation: In OSPFv2, a Cisco router uses a three-tier method to derive its router ID. The first choice is the manually configured router ID with the router-id command. If the router ID is not manually configured, the router will choose the highest IPv4 address of the configured loopback interfaces. Finally if no loopback interfaces are configured, the router chooses the highest active IPv4 address of its physical interfaces.
163. Match the HTTP method with the RESTful operation.
164. Refer to the exhibit. A web designer calls to report that the web server web-s1.cisco.com is not reachable through a web browser. The technician uses command line utilities to verify the problem and to begin the troubleshooting process. Which two things can be determined about the problem? (Choose two.)
- The web server at 192.168.0.10 is reachable from the source host.
- DNS cannot resolve the IP address for the server web-s1.cisco.com.
- A router is down between the source host and the server web-s1.cisco.com.
- There is a problem with the web server software on web-s1.cisco.com.
- The default gateway between the source host and the server at 192.168.0.10 is down.
Explanation: The successful result of the ping to the IP address indicates that the network is operational and the web server is online. However, the fact that the ping to the domain name of the server fails indicates there is a DNS issue, namely that the host cannot resolve the domain name to its associated IP address.
165. What type of traffic is described as tending to be unpredictable, inconsistent, and bursty?
- video
- voice
- data
166. Match the functions to the corresponding layers. (Not all options are used.)
167. What type of traffic is described as consisting of traffic that requires a higher priority if interactive?
- voice
- data
- video
168. Which type of VPN provides a flexible option to connect a central site with branch sites?
- IPsec virtual tunnel interface
- MPLS VPN
- dynamic multipoint VPN
- GRE over IPsec
169. A company has contracted with a network security firm to help identify the vulnerabilities of the corporate network. The firm sends a team to perform penetration tests to the company network. Why would the team use fuzzers?
- to discover security vulnerabilities of a computer
- to detect any evidence of a hack or malware in a computer or network
- to reverse engineer binary files when writing exploits and when analyzing malware
- to detect installed tools within files and directories that provide threat actors remote access and control over a computer or network
170. Refer to the exhibit. A network administrator has configured a standard ACL to permit only the two LAN networks attached to R1 to access the network that connects to R2 G0/1 interface, but not the G0/0 interface. When following the best practices, in what location should the standard ACL be applied?
- R1 S0/0/0 outbound
- R2 G0/0 outbound
- R2 S0/0/1 outbound
- R1 S0/0/0 inbound
- R2 G0/1 inbound
171. Two OSPF-enabled routers are connected over a point-to-point link. During the ExStart state, which router will be chosen as the first one to send DBD packets?
- the router with the highest router ID
- the router with the lowest IP address on the connecting interface
- the router with the highest IP address on the connecting interface
- the router with the lowest router ID
Explain:In the ExStart state, the two routers decide which router will send the DBD packets first. The router with the higher router ID will be the first router to send DBD packets during the Exchange state
172. Which step in the link-state routing process is described by a router sending Hello packets out all of the OSPF-enabled interfaces?
- exchanging link-state advertisements
- electing the designated router
- injecting the default route
- establishing neighbor adjacencies
173. A company has contracted with a network security firm to help identify the vulnerabilities of the corporate network. The firm sends a team to perform penetration tests to the company network. Why would the team use forensic tools?
- to obtain specially designed operating systems preloaded with tools optimized for hacking
- to detect any evidence of a hack or malware in a computer or network
- to detect installed tools within files and directories that provide threat actors remote access and control over a computer or network
- to reverse engineer binary files when writing exploits and when analyzing malware
174. Refer to the exhibit. A network administrator has configured OSPFv2 on the two Cisco routers but PC1 is unable to connect to PC2. What is the most likely problem?
- Interface Fa0/0 has not been activated for OSPFv2 on router R2.
- Interface Fa0/0 is configured as a passive-interface on router R2.
- Interface S0/0 is configured as a passive-interface on router R2.
- Interface s0/0 has not been activated for OSPFv2 on router R2.
Explanation: If a LAN network is not advertised using OSPFv2, a remote network will not be reachable. The output displays a successful neighbor adjacency between router R1 and R2 on the interface S0/0 of both routers.
175. ABCTech is investigating the use of automation for some of its products. In order to control and test these products, the programmers require Windows, Linux, and MAC OS on their computers. What service or technology would support this requirement?
- dedicated servers
- software defined networking
- virtualization
- Cisco ACI
176. A network engineer has noted that some expected network route entries are not displayed in the routing table. Which two commands will provide additional information about the state of router adjacencies, timer intervals, and the area ID? (Choose two.)
- show ip protocols
- show ip ospf neighbor
- show running-configuration
- show ip ospf interface
- show ip route ospf
Explanation: The show ip ospf interface command will display routing table information that is already known. The show running-configuration and show ip protocols commands will display aspects of the OSPF configuration on the router but will not display adjacency state details or timer interval details.
177. Which type of VPN involves the forwarding of traffic over the backbone through the use of labels distributed among core routers?
- MPLS VPN
- GRE over IPsec
- IPsec virtual tunnel interface
- dynamic multipoint VPN
178. Which type of VPN involves a nonsecure tunneling protocol being encapsulated by IPsec?
- SSL VPN
- dynamic multipoint VPN
- GRE over IPsec
- IPsec virtual tunnel interface
179. A company has contracted with a network security firm to help identify the vulnerabilities of the corporate network. The firm sends a team to perform penetration tests to the company network. Why would the team use hacking operation systems?
- to detect any evidence of a hack or malware in a computer or network
- to obtain specially designed operating systems preloaded with tools optimized for hacking
- to encode data, using algorithm schemes, to prevent unauthorized access to the encrypted data
- to reverse engineer binary files when writing exploits and when analyzing malware
180. What command would be used as part of configuring NAT or PAT to identify an interface as part of the external global network?
- ip pat inside
- access-list 10 permit 172.19.89.0 0.0.0.255
- ip nat inside
- ip nat outside
181. To avoid purchasing new hardware, a company wants to take advantage of idle system resources and consolidate the number of servers while allowing for multiple operating systems on a single hardware platform. What service or technology would support this requirement?
- data center
- cloud services
- virtualization
- dedicated servers
Explain: Server virtualization takes advantage of idle resources and consolidates the number of required servers. This also allows for multiple operating systems to exist on a single hardware platform.
182. Which type of VPN routes packets through virtual tunnel interfaces for encryption and forwarding?
- MPLS VPN
- IPsec virtual tunnel interface
- dynamic multipoint VPN
- GRE over IPsec
183. Which step in the link-state routing process is described by a router flooding link-state and cost information about each directly connected link?
- building the topology table
- selecting the router ID
- exchanging link-state advertisements
- injecting the default route
184. What type of traffic is described as using either TCP or UDP depending on the need for error recovery?
- video
- voice
- data
185. Refer to the exhibit. The company CEO demands that one ACL be created to permit email traffic to the internet and deny FTP access. What is the best ACL type and placement to use in this situation?
- extended ACL outbound on R2 WAN interface towards the internet
- standard ACL outbound on R2 S0/0/0
- extended ACL inbound on R2 S0/0/0
- standard ACL inbound on R2 WAN interface connecting to the internet
186. What command would be used as part of configuring NAT or PAT to define a pool of addresses for translation?
- ip nat inside source static 172.19.89.13 198.133.219.65
- ip nat inside source list 24 interface serial 0/1/0 overload
- ip nat pool POOL-STAT 64.100.14.17 64.100.14.30 netmask 255.255.255.240
- ip nat outside
187. What is the name of the layer in the Cisco borderless switched network design that is considered to be the backbone used for high-speed connectivity and fault isolation?
- data link
- access
- core
- network
- network access
Explanation: The three layers of the Cisco borderless switch network design are access, distribution, and core. The access layer switches are the ones used to connect end devices to the network. The distribution layer switches accept connections from access layer switches and provides switching, routing, and access policy functions. The core layer is called the backbone and core switches commonly have high-speed redundant connections.
188. An ACL is applied inbound on router interface. The ACL consists of a single entry:
access-list 210 permit tcp 172.18.20.0 0.0.0.47 any eq ftp
If a packet with a source address of 172.18.20.40, a destination address of 10.33.19.2, and a protocol of 21 is received on the interface, is the packet permitted or denied?
- permitted
- denied
189. What type of traffic is described as consisting of traffic that gets a lower priority if it is not mission-critical?
- video
- data
- voice
190. Which OSPF table is identical on all converged routers within the same OSPF area?
- routing
- neighbor
- adjacency
- topology
191. An ACL is applied inbound on a router interface. The ACL consists of a single entry:
access-list 100 permit tcp 192.168.10.0 0.0.0.255 any eq www .
If a packet with a source address of 192.168.10.45, a destination address of 10.10.3.27, and a protocol of 80 is received on the interface, is the packet permitted or denied?
- permitted
- denied
192. What protocol allows the manager to poll agents to access information from the agent MIB?
- CBWFQ
- SYSLOG
- TFTP
- SNMP
193. Match each component of a WAN connection to its description. (Not all options are used.)
Case 2:
194. What type of traffic is described as being able to tolerate a certain amount of latency, jitter, and loss without any noticeable effects?
- voice
- video
- data
195. What term describes adding a value to the packet header, as close to the source as possible, so that the packet matches a defined policy?
- policing
- traffic marking
- weighted random early detection (WRED)
- traffic shaping
- tail drop
196. Which three traffic-related factors would influence selecting a particular WAN link type? (Choose three.)
- cost of the link
- amount of traffic
- distance between sites
- reliability
- security needs
- type of traffic
Explanation: The traffic-related factors that influence selecting a particular WAN link type include the type of traffic, amount of traffic, quality requirements, and security requirements. Quality requirements include ensuring that traffic that cannot tolerate delay gets priority treatment as well as important business transactional traffic.
197. What command would be used as part of configuring NAT or PAT to link the inside local addresses to the pool of addresses available for PAT translation?
- ip nat inside source list ACCTNG pool POOL-STAT
- ip nat translation timeout 36000
- ip nat inside source list 14 pool POOL-STAT overload
- ip nat inside source static 172.19.89.13 198.133.219.65
198. What protocol is a vendor-neutral Layer 2 discovery protocol that must be configured separately to transmit and receive information packets?
- SNMP
- MPLS
- LLDP
- NTP
199. An ACL is applied inbound on a router interface. The ACL consists of a single entry:access-list 210 permit tcp 172.18.20.0 0.0.0.31 172.18.20.32 0.0.0.31 eq ftp .
If a packet with a source address of 172.18.20.55, a destination address of 172.18.20.3, and a protocol of 21 is received on the interface, is the packet permitted or denied?
- permitted
- denied
200. Refer to the exhibit. Corporate policy demands that access to the server network be restricted to internal employees only. What is the best ACL type and placement to use in this situation?
Corporate policy demands that access to the server network be restricted to internal employees only. What is the best ACL type and placement to use in this situation
- extended ACL outbound on R2 S0/0/1
- standard ACL outbound on R2 S0/0/0
- standard ACL inbound on R2 WAN interface connecting to the internet
- extended ACL inbound on R2 S0/0/0
201. A technician is working on a Layer 2 switch and notices that a %CDP-4-DUPLEX_MISMATCH message keeps appearing for port G0/5. What command should the technician issue on the switch to start the troubleshooting process?
- show cdp neighbors
- show ip interface brief
- show interface g0/5
- show cdp
202. Which virtual resource would be installed on a network server to provide direct access to hardware resources?
- VMware Fusion
- a management console
- a dedicated VLAN
- a Type 1 hypervisor
Explanation: Type 1 hypervisors, the hypervisor is installed directly on the server or networking hardware. Then, instances of an OS are installed on the hypervisor, as shown in the figure. Type 1 hypervisors have direct access to the hardware resources. Therefore, they are more efficient than hosted architectures. Type 1 hypervisors improve scalability, performance, and robustness.
203. Refer to the exhibit. A network administrator has configured a standard ACL to permit only the two LAN networks attached to R1 to access the network that connects to R2 G0/1 interface. When following the best practices, in what location should the standard ACL be applied?
Enterprise Networking, Security, and Automation ( Version 7.00) – ENSA Final Exam
- R2 G0/1 inbound
- R2 S0/0/1 outbound
- R1 S0/0/0 outbound
- R2 G0/1 outbound
- R2 G0/0 outbound
204. Which OSPF database is identical on all converged routers within the same OSPF area?
- neighbor
- forwarding
- link-state
- adjacency
Explanation: Regardless of which OSPF area a router resides in, the adjacency database, routing table, and forwarding database are unique for each router. The link-state database lists information about all other routers within an area and is identical across all OSPF routers participating in that area.
205. What are two features to consider when creating a named ACL? (Choose two.)
- Use alphanumeric characters if needed.
- Use special characters, such as ! or * to show the importance of the ACL.
- Modify the ACL using a text editor.
- Be descriptive when creating the ACL name.
- Use a space for ease of reading to separate the name from the description
Explanation: The following summarizes the rules to follow for named ACLs:
- Assign a name to identify the purpose of the ACL.
- Names can contain alphanumeric characters.
- Names cannot contain spaces or punctuation.
- It is suggested that the name be written in CAPITAL LETTERS.
- Entries can be added or deleted within the ACL.
206. Match the RESTful API method to CRUD function.
Match the RESTful API method to CRUD function.
207. What type of traffic is described as requiring at least 384 Kbps of bandwidth?
- voice
- data
- video
208. Which step in the link-state routing process is described by a router inserting best paths into the routing table?
- declaring a neighbor to be inaccessible
- executing the SPF algorithm
- load balancing equal-cost paths
- choosing the best route
209. Anycompany has decided to reduce its environmental footprint by reducing energy costs, moving to a smaller facility, and promoting telecommuting. What service or technology would support this requirement?
- data center
- virtualization
- cloud services
- dedicated servers
210. Which QoS technique smooths packet output rate?
- policing
- shaping
- weighted random early detection
- Integrated Services (IntServ)
- marking
211. Refer to the exhibit. The company has provided IP phones to employees on the 192.168.10.0/24 network and the voice traffic will need priority over data traffic. What is the best ACL type and placement to use in this situation?
- extended ACL inbound on R1 G0/0
- extended ACL outbound on R2 WAN interface towards the internet
- extended ACL outbound on R2 S0/0/1
- extended ACLs inbound on R1 G0/0 and G0/1
Explanation: Standard ACLs permit or deny packets based only on the source IPv4 address. Because all traffic types are permitted or denied, standard ACLs should be located as close to the destination as possible.
Extended ACLs permit or deny packets based on the source IPv4 address and destination IPv4 address, protocol type, source and destination TCP or UDP ports and more. Because the filtering of extended ACLs is so specific, extended ACLs should be located as close as possible to the source of the traffic to be filtered. Undesirable traffic is denied close to the source network without crossing the network infrastructure.
212. A network technician is configuring SNMPv3 and has set a security level of SNMPv3 authPriv. What is a feature of using this level?
- authenticates a packet by using the SHA algorithm only
- authenticates a packet by a string match of the username or community string
- authenticates a packet by using either the HMAC with MD5 method or the SHA method
- authenticates a packet by using either the HMAC MD5 or HMAC SHA algorithms and a username
CCNA 1 – ITN Introduction to Networks (Version 7.00) – ITNv7 Final Exam Answers Full
Number of questions: 60; Passed score: 80-100%
1. What two ICMPv6 message types must be permitted through IPv6 access control lists to allow resolution of Layer 3 addresses to Layer 2 MAC addresses? (Choose two.)
- neighbor solicitations
- echo requests
- neighbor advertisements
- echo replies
- router solicitations
- router advertisements
2. Which range of link-local addresses can be assigned to an IPv6-enabled interface?
- FEC0::/10
- FDEE::/7
- FE80::/10
- FF00::/8
Explain:
Link-local addresses are in the range of FE80::/10 to FEBF::/10. The original IPv6 specification defined site-local addresses and used the prefix range FEC0::/10, but these addresses were deprecated by the IETF in favor of unique local addresses. FDEE::/7 is a unique local address because it is in the range of FC00::/7 to FDFF::/7. IPv6 multicast addresses have the prefix FF00::/8.
3. What would be the interface ID of an IPv6 enabled interface with a MAC address of 1C-6F-65-C2-BD-F8 when the interface ID is generated by using the EUI-64 process?
- 0C6F:65FF:FEC2:BDF8
- 1E6F:65FF:FEC2:BDF8
- C16F:65FF:FEC2:BDF8
- 106F:65FF:FEC2:BDF8
Explanation: To derive the EUI-64 interface ID by using the MAC address 1C-6F-65-C2-BD-F8, three steps are taken.
- Change the seventh bit of the MAC address from a binary 0 to a binary 1 which changes the hex C, into a hex E.
- Insert hex digits FFFE into the middle of the address.
- Rewrite the address in IPv6 format.
The three steps, when complete, give the interface ID of 1E6F:65FF:FEC2:BDF8.
4. An organization is assigned an IPv6 address block of 2001:db8:0:ca00::/56. How many subnets can be created without using bits in the interface ID space?
- 256
- 512
- 1024
- 4096
5. Refer to the exhibit. If host A sends an IP packet to host B, what will the destination address be in the frame when it leaves host A?
- DD:DD:DD:DD:DD:DD
- 172.168.10.99
- CC:CC:CC:CC:CC:CC
- 172.168.10.65
- BB:BB:BB:BB:BB:BB
- AA:AA:AA:AA:AA:AA
Explain:
When a host sends information to a distant network, the Layer 2 frame header will contain a source and destination MAC address. The source address will be the originating host device. The destination address will be the router interface that connects to the same network. In the case of host A sending information to host B, the source address is AA:AA:AA:AA:AA:AA and the destination address is the MAC address assigned to the R2 Ethernet interface, BB:BB:BB:BB:BB:BB.
6. When a switch configuration includes a user-defined error threshold on a per-port basis, to which switching method will the switch revert when the error threshold is reached?
- cut-through
- store-and-forward
- fast-forward
- fragment-free
7. Which two statements are correct about MAC and IP addresses during data transmission if NAT is not involved? (Choose two.)
- Destination IP addresses in a packet header remain constant along the entire path to a target host.
- Destination MAC addresses will never change in a frame that goes across seven routers.
- Every time a frame is encapsulated with a new destination MAC address, a new destination IP address is needed.
- Destination and source MAC addresses have local significance and change every time a frame goes from one LAN to another.
- A packet that has crossed four routers has changed the destination IP address four times.
8. What is one main characteristic of the data link layer?
- It generates the electrical or optical signals that represent the 1 and 0 on the media.
- It converts a stream of data bits into a predefined code.
- It shields the upper layer protocol from being aware of the physical medium to be used in the communication.
- It accepts Layer 3 packets and decides the path by which to forward the packet to a remote network.
9. What are three characteristics of the CSMA/CD process? (Choose three.)
- The device with the electronic token is the only one that can transmit after a collision.
- A device listens and waits until the media is not busy before transmitting.
- After detecting a collision, hosts can attempt to resume transmission after a random time delay has expired.
- All of the devices on a segment see data that passes on the network medium.
- A jam signal indicates that the collision has cleared and the media is not busy.
- Devices can be configured with a higher transmission priority.
Explanation: The Carrier Sense Multiple Access/Collision Detection (CSMA/CD) process is a contention-based media access control mechanism used on shared media access networks, such as Ethernet. When a device needs to transmit data, it listens and waits until the media is available (quiet), then it will send data. If two devices transmit at the same time, a collision will occur. Both devices will detect the collision on the network. When a device detects a collision, it will stop the data transmission process, wait for a random amount of time, then try again.
10. What are two primary responsibilities of the Ethernet MAC sublayer? (Choose two.)
- error detection
- frame delimiting
- accessing the media
- data encapsulation
- logical addressing
11. Which two commands can be used on a Windows host to display the routing table? (Choose two.)
- netstat -s
- route print
- show ip route
- netstat -r
- tracert
Explain:
On a Windows host, the route print or netstat -r commands can be used to display the host routing table. Both commands generate the same output. On a router, the show ip route command is used to display the routing table. The netstat –s command is used to display per-protocol statistics. The tracert command is used to display the path that a packet travels to its destination.
12. What are two functions that are provided by the network layer? (Choose two.)
- directing data packets to destination hosts on other networks
- placing data on the network medium
- carrying data between processes that are running on source and destination hosts
- providing dedicated end-to-end connections
- providing end devices with a unique network identifier
13. Which two statements describe features of an IPv4 routing table on a router? (Choose two.)
- Directly connected interfaces will have two route source codes in the routing table: C and S.
- If there are two or more possible routes to the same destination, the route associated with the higher metric value is included in the routing table.
- The netstat -r command can be used to display the routing table of a router.
- The routing table lists the MAC addresses of each active interface.
- It stores information about routes derived from the active router interfaces.
- If a default static route is configured in the router, an entry will be included in the routing table with source code S.
14. How does the service password-encryption command enhance password security on Cisco routers and switches?
- It requires encrypted passwords to be used when connecting remotely to a router or switch with Telnet.
- It encrypts passwords that are stored in router or switch configuration files.
- It requires that a user type encrypted passwords to gain console access to a router or switch.
- It encrypts passwords as they are sent across the network.
Explain: The service password-encryption command encrypts plaintext passwords in the configuration file so that they cannot be viewed by unauthorized users.
15. Why would a Layer 2 switch need an IP address?
- to enable the switch to send broadcast frames to attached PCs
- to enable the switch to function as a default gateway
- to enable the switch to be managed remotely
- to enable the switch to receive frames from attached PCs
Explanation: A switch, as a Layer 2 device, does not need an IP address to transmit frames to attached devices. However, when a switch is accessed remotely through the network, it must have a Layer 3 address. The IP address must be applied to a virtual interface rather than to a physical interface. Routers, not switches, function as default gateways.
16. What characteristic describes identity theft?
- the use of stolen credentials to access private data
- software on a router that filters traffic based on IP addresses or applications
- software that identifies fast-spreading threats
- a tunneling protocol that provides remote users with secure access into the network of an organization
17. Match each description to its corresponding term. (Not all options are used.)
18. A user sends an HTTP request to a web server on a remote network. During encapsulation for this request, what information is added to the address field of a frame to indicate the destination?
- the network domain of the destination host
- the IP address of the default gateway
- the MAC address of the destination host
- the MAC address of the default gateway
Explanation: A frame is encapsulated with source and destination MAC addresses. The source device will not know the MAC address of the remote host. An ARP request will be sent by the source and will be responded to by the router. The router will respond with the MAC address of its interface, the one which is connected to the same network as the source.
19. Data is being sent from a source PC to a destination server. Which three statements correctly describe the function of TCP or UDP in this situation? (Choose three.)
- The source port field identifies the running application or service that will handle data returning to the PC.
- The TCP process running on the PC randomly selects the destination port when establishing a session with the server.
- UDP segments are encapsulated within IP packets for transport across the network.
- The UDP destination port number identifies the application or service on the server which will handle the data.
- TCP is the preferred protocol when a function requires lower network overhead.
- The TCP source port number identifies the sending host on the network.
Explanation: Layer 4 port numbers identify the application or service which will handle the data. The source port number is added by the sending device and will be the destination port number when the requested information is returned. Layer 4 segments are encapsulated within IP packets. UDP, not TCP, is used when low overhead is needed. A source IP address, not a TCP source port number, identifies the sending host on the network. Destination port numbers are specific ports that a server application or service monitors for requests.
20. Match each description with the corresponding TCP mechanism. (Not all options are used.)
21. Refer to the exhibit. Which two network addresses can be assigned to the network containing 10 hosts? Your answers should waste the fewest addresses, not reuse addresses that are already assigned, and stay within the 10.18.10.0/24 range of addresses. (Choose two.)
- 10.18.10.200/28
- 10.18.10.208/28
- 10.18.10.240/27
- 10.18.10.200/27
- 10.18.10.224/27
- 10.18.10.224/28
Explanation: Addresses 10.18.10.0 through 10.18.10.63 are taken for the leftmost network. Addresses 192 through 199 are used by the center network. Because 4 host bits are needed to accommodate 10 hosts, a /28 mask is needed. 10.18.10.200/28 is not a valid network number. Two subnets that can be used are 10.18.10.208/28 and 10.18.10.224/28.
22. Refer to the exhibit. A company uses the address block of 128.107.0.0/16 for its network. What subnet mask would provide the maximum number of equal size subnets while providing enough host addresses for each subnet in the exhibit?
- 255.255.255.192
- 255.255.255.0
- 255.255.255.128
- 255.255.255.240
- 255.255.255.224
Explanation: The largest subnet in the topology has 100 hosts in it so the subnet mask must have at least 7 host bits in it (27-2=126). 255.255.255.0 has 8 hosts bits, but this does not meet the requirement of providing the maximum number of subnets.
23. A network administrator wants to have the same subnet mask for three subnetworks at a small site. The site has the following networks and numbers of devices:
Subnetwork A: IP phones – 10 addresses Subnetwork B: PCs – 8 addresses Subnetwork C: Printers – 2 addresses
What single subnet mask would be appropriate to use for the three subnetworks?
- 255.255.255.0
- 255.255.255.240
- 255.255.255.248
- 255.255.255.252
Explain:
If the same mask is to be used, then the network with the most hosts must be examined for number of hosts. Because this is 10 hosts, 4 host bits are needed. The /28 or 255.255.255.240 subnet mask would be appropriate to use for these networks.
24. Match each item to the type of topology diagram on which it is typically identified. (Not all options are used.)
25. What two pieces of information are displayed in the output of the show ip interface brief command? (Choose two.)
- IP addresses
- interface descriptions
- MAC addresses
- next-hop addresses
- Layer 1 statuses
- speed and duplex settings
Explanation: The command show ip interface brief shows the IP address of each interface, as well as the operational status of the interfaces at both Layer 1 and Layer 2. In order to see interface descriptions and speed and duplex settings, use the command show running-config interface. Next-hop addresses are displayed in the routing table with the command show ip route, and the MAC address of an interface can be seen with the command show interfaces.
26. A user is complaining that an external web page is taking longer than normal to load.The web page does eventually load on the user machine. Which tool should the technician use with administrator privileges in order to locate where the issue is in the network?
- ping
- nslookup
- tracert
- ipconfig /displaydns
27. A network technician is researching the use of fiber optic cabling in a new technology center. Which two issues should be considered before implementing fiber optic media? (Choose two.)
- Fiber optic cabling requires different termination and splicing expertise from what copper cabling requires.
- Fiber optic cabling requires specific grounding to be immune to EMI.
- Fiber optic cabling is susceptible to loss of signal due to RFI.
- Fiber optic cable is able to withstand rough handling.
- Fiber optic provides higher data capacity but is more expensive than copper cabling.
28. What technique is used with UTP cable to help protect against signal interference from crosstalk?
- wrapping a foil shield around the wire pairs
- twisting the wires together into pairs
- terminating the cable with special grounded connectors
- encasing the cables within a flexible plastic sheath
Explanation: To help prevent the effects of crosstalk, UTP cable wires are twisted together into pairs. Twisting the wires together causes the magnetic fields of each wire to cancel each other out.
29. A network administrator is designing the layout of a new wireless network. Which three areas of concern should be accounted for when building a wireless network? (Choose three.)
- extensive cabling
- mobility options
- packet collision
- interference
- security
- coverage area
Explanation: The three areas of concern for wireless networks focus on the size of the coverage area, any nearby interference, and providing network security. Extensive cabling is not a concern for wireless networks, as a wireless network will require minimal cabling for providing wireless access to hosts. Mobility options are not a component of the areas of concern for wireless networks.
30. Match each description with an appropriate IP address. (Not all options are used.)
31. Users report that the network access is slow. After questioning the employees, the network administrator learned that one employee downloaded a third-party scanning program for the printer. What type of malware might be introduced that causes slow performance of the network?
- virus
- worm
- phishing
- spam
Explanation: A cybersecurity specialist needs to be familiar with the characteristics of the different types of malware and attacks that threaten an organization.
32. Which scenario describes a function provided by the transport layer?
- A student is using a classroom VoIP phone to call home. The unique identifier burned into the phone is a transport layer address used to contact another network device on the same network.
- A student is playing a short web-based movie with sound. The movie and sound are encoded within the transport layer header.
- A student has two web browser windows open in order to access two web sites. The transport layer ensures the correct web page is delivered to the correct browser window.
- A corporate worker is accessing a web server located on a corporate network. The transport layer formats the screen so the web page appears properly no matter what device is being used to view the web site.
Explain:
The source and destination port numbers are used to identify the correct application and window within that application.
33.Refer to the exhibit. Host B on subnet Teachers transmits a packet to host D on subnet Students. Which Layer 2 and Layer 3 addresses are contained in the PDUs that are transmitted from host B to the router?
Layer 2 destination address = 00-00-0c-94-36-ab
Layer 2 source address = 00-00-0c-94-36-bb
Layer 3 destination address = 172.16.20.200
Layer 3 source address = 172.16.10.200
Layer 2 destination address = 00-00-0c-94-36-dd
Layer 2 source address = 00-00-0c-94-36-bb
Layer 3 destination address = 172.16.20.200
Layer 3 source address = 172.16.10.200
Layer 2 destination address = 00-00-0c-94-36-cd
Layer 2 source address = 00-00-0c-94-36-bb
Layer 3 destination address = 172.16.20.99
Layer 3 source address = 172.16.10.200
Layer 2 destination address = 00-00-0c-94-36-ab
Layer 2 source address = 00-00-0c-94-36-bb
Layer 3 destination address = 172.16.20.200
Layer 3 source address = 172.16.100.200
34. What does the term “attenuation” mean in data communication?
- strengthening of a signal by a networking device
- leakage of signals from one cable pair to another
- time for a signal to reach its destination
- loss of signal strength as distance increases
35. Refer to the exhibit. An administrator is trying to configure the switch but receives the error message that is displayed in the exhibit. What is the problem?
- The entire command, configure terminal, must be used.
- The administrator is already in global configuration mode.
- The administrator must first enter privileged EXEC mode before issuing the command.
- The administrator must connect via the console port to access global configuration mode.
36. Which two protocols operate at the top layer of the TCP/IP protocol suite? (Choose two.)
- TCP
- IP
- UDP
- POP
- DNS
- Ethernet
37. A company has a file server that shares a folder named Public. The network security policy specifies that the Public folder is assigned Read-Only rights to anyone who can log into the server while the Edit rights are assigned only to the network admin group. Which component is addressed in the AAA network service framework?
- automation
- accounting
- authentication
- authorization
After a user is successfully authenticated (logged into the server), the authorization is the process of determining what network resources the user can access and what operations (such as read or edit) the user can perform.
38. What three requirements are defined by the protocols used in network communcations to allow message transmission across a network? (Choose three.)
- message size
- message encoding
- connector specifications
- media selection
- delivery options
- end-device installation
39. What are two characteristics of IP? (Choose two.)
- does not require a dedicated end-to-end connection
- operates independently of the network media
- retransmits packets if errors occur
- re-assembles out of order packets into the correct order at the receiver end
- guarantees delivery of packets
Explain:
The Internet Protocol (IP) is a connectionless, best effort protocol. This means that IP requires no end-to-end connection nor does it guarantee delivery of packets. IP is also media independent, which means it operates independently of the network media carrying the packets.
40. An employee of a large corporation remotely logs into the company using the appropriate username and password. The employee is attending an important video conference with a customer concerning a large sale. It is important for the video quality to be excellent during the meeting. The employee is unaware that after a successful login, the connection to the company ISP failed. The secondary connection, however, activated within seconds. The disruption was not noticed by the employee or other employees.
What three network characteristics are described in this scenario? (Choose three.)
- security
- quality of service
- scalability
- powerline networking
- integrity
- fault tolerance
41. What are two common causes of signal degradation when using UTP cabling? (Choose two.)
- improper termination
- low-quality shielding in cable
- installing cables in conduit
- low-quality cable or connectors
- loss of light over long distances
42. Which subnet would include the address 192.168.1.96 as a usable host address?
- 192.168.1.64/26
- 192.168.1.32/27
- 192.168.1.32/28
- 192.168.1.64/29
Explanation: For the subnet of 192.168.1.64/26, there are 6 bits for host addresses, yielding 64 possible addresses. However, the first and last subnets are the network and broadcast addresses for this subnet. Therefore, the range of host addresses for this subnet is 192.168.1.65 to 192.168.1.126. The other subnets do not contain the address 192.168.1.96 as a valid host address.
43. Refer to the exhibit. On the basis of the output, which two statements about network connectivity are correct? (Choose two.)
- This host does not have a default gateway configured.
- There are 4 hops between this device and the device at 192.168.100.1.
- There is connectivity between this device and the device at 192.168.100.1.
- The connectivity between these two hosts allows for videoconferencing calls.
- The average transmission time between the two hosts is 2 milliseconds.
Explain:
The output displays a successful Layer 3 connection between a host computer and a host at 19.168.100.1. It can be determined that 4 hops exist between them and the average transmission time is 1 milliseconds. Layer 3 connectivity does not necessarily mean that an application can run between the hosts.
44. Which two statements describe how to assess traffic flow patterns and network traffic types using a protocol analyzer? (Choose two.)
- Capture traffic on the weekends when most employees are off work.
- Capture traffic during peak utilization times to get a good representation of the different traffic types.
- Only capture traffic in the areas of the network that receive most of the traffic such as the data center.
- Perform the capture on different network segments.
- Only capture WAN traffic because traffic to the web is responsible for the largest amount of traffic on a network.
Explanation: Traffic flow patterns should be gathered during peak utilization times to get a good representation of the different traffic types. The capture should also be performed on different network segments because some traffic will be local to a particular segment.
45. What is the consequence of configuring a router with the ipv6 unicast-routing global configuration command?
- All router interfaces will be automatically activated.
- The IPv6 enabled router interfaces begin sending ICMPv6 Router Advertisement messages.
- Each router interface will generate an IPv6 link-local address.
- It statically creates a global unicast address on this router.
46. Which three layers of the OSI model map to the application layer of the TCP/IP model? (Choose three.)
- application
- network
- data link
- session
- presentation
- transport
Explanation: The TCP/IP model consists of four layers: application, transport, internet, and network access. The OSI model consists of seven layers: application, presentation, session, transport, network, data link, and physical. The top three layers of the OSI model: application, presentation, and session map to the application layer of the TCP/IP model.
47. Refer to the exhibit. If PC1 is sending a packet to PC2 and routing has been configured between the two routers, what will R1 do with the Ethernet frame header attached by PC1?
- nothing, because the router has a route to the destination network
- open the header and use it to determine whether the data is to be sent out S0/0/0
- open the header and replace the destination MAC address with a new one
- remove the Ethernet header and configure a new Layer 2 header before sending it out S0/0/0
Explanation: When PC1 forms the various headers attached to the data one of those headers is the Layer 2 header. Because PC1 connects to an Ethernet network, an Ethernet header is used. The source MAC address will be the MAC address of PC1 and the destination MAC address will be that of G0/0 on R1. When R1 gets that information, the router removes the Layer 2 header and creates a new one for the type of network the data will be placed onto (the serial link).
48. What will happen if the default gateway address is incorrectly configured on a host?
- The host cannot communicate with other hosts in the local network.
- The host cannot communicate with hosts in other networks.
- A ping from the host to 127.0.0.1 would not be successful.
- The host will have to use ARP to determine the correct address of the default gateway.
- The switch will not forward packets initiated by the host.
49. What are two features of ARP? (Choose two.)
- When a host is encapsulating a packet into a frame, it refers to the MAC address table to determine the mapping of IP addresses to MAC addresses.
- An ARP request is sent to all devices on the Ethernet LAN and contains the IP address of the destination host and its multicast MAC address.
- If a host is ready to send a packet to a local destination device and it has the IP address but not the MAC address of the destination, it generates an ARP broadcast.
- If no device responds to the ARP request, then the originating node will broadcast the data packet to all devices on the network segment.
- If a device receiving an ARP request has the destination IPv4 address, it responds with an ARP reply.
50. A network administrator is adding a new LAN to a branch office. The new LAN must support 90 connected devices. What is the smallest network mask that the network administrator can use for the new network?
- 255.255.255.128
- 255.255.255.240
- 255.255.255.248
- 255.255.255.224
51. What are two ICMPv6 messages that are not present in ICMP for IPv4? (Choose two.)
- Neighbor Solicitation
- Destination Unreachable
- Host Confirmation
- Time Exceeded
- Router Advertisement
- Route Redirection
52. A client packet is received by a server. The packet has a destination port number of 80. What service is the client requesting?
- DHCP
- SMTP
- DNS
- HTTP
53. What is an advantage for small organizations of adopting IMAP instead of POP?
- POP only allows the client to store messages in a centralized way, while IMAP allows distributed storage.
- Messages are kept in the mail servers until they are manually deleted from the email client.
- When the user connects to a POP server, copies of the messages are kept in the mail server for a short time, but IMAP keeps them for a long time.
- IMAP sends and retrieves email, but POP only retrieves email.
Explanation: IMAP and POP are protocols that are used to retrieve email messages. The advantage of using IMAP instead of POP is that when the user connects to an IMAP-capable server, copies of the messages are downloaded to the client application. IMAP then stores the email messages on the server until the user manually deletes those messages.
54. A technician can ping the IP address of the web server of a remote company but cannot successfully ping the URL address of the same web server. Which software utility can the technician use to diagnose the problem?
- tracert
- ipconfig
- netstat
- nslookup
Explain:
Traceroute (tracert) is a utility that generates a list of hops that were successfully reached along the path from source to destination.This list can provide important verification and troubleshooting information. The ipconfig utility is used to display the IP configuration settings on a Windows PC. The Netstat utility is used to identify which active TCP connections are open and running on a networked host. Nslookup is a utility that allows the user to manually query the name servers to resolve a given host name. This utility can also be used to troubleshoot name resolution issues and to verify the current status of the name servers.
55. Which two functions are performed at the LLC sublayer of the OSI Data Link Layer to facilitate Ethernet communication? (Choose two.)
- implements CSMA/CD over legacy shared half-duplex media
- enables IPv4 and IPv6 to utilize the same physical medium
- integrates Layer 2 flows between 10 Gigabit Ethernet over fiber and 1 Gigabit Ethernet over copper
- implements a process to delimit fields within an Ethernet 2 frame
- places information in the Ethernet frame that identifies which network layer protocol is being encapsulated by the frame
Other case:
- responsible for internal structure of Ethernet frame
- applies source and destination MAC addresses to Ethernet frame
- handles communication between upper layer networking software and Ethernet NIC hardware
- adds Ethernet control information to network protocol data
- implements trailer with frame check sequence for error detection
Other case:
- integrates Layer 2 flows between 10 Gigabit Ethernet over fiber and 1 Gigabit Ethernet over copper
- places information in the Ethernet frame that identifies which network layer protocol is being encapsulated by the frame
- implements CSMA/CD over legacy shared half-duplex media
- adds Ethernet control information to network protocol data
- applies source and destination MAC addresses to Ethernet frame
Other case:
- enables IPv4 and IPv6 to utilize the same physical medium
- adds Ethernet control information to network protocol data
- applies source and destination MAC addresses to Ethernet frame
- responsible for the internal structure of Ethernet frame
- implements trailer with frame check sequence for error detection
Other case:
- enables IPv4 and IPv6 to utilize the same physical medium
- applies source and destination MAC addresses to Ethernet frame
- integrates Layer 2 flows between 10 Gigabit Ethernet over fiber and 1 Gigabit Ethernet over copper
- handles communication between upper layer networking software and Ethernet NIC hardware
- responsible for internal structure of Ethernet frame
Explanation: The data link layer is actually divided into two sublayers:
+ Logical Link Control (LLC): This upper sublayer defines the software processes that provide services to the network layer protocols. It places information in the frame that identifies which network layer protocol is being used for the frame. This information allows multiple Layer 3 protocols, such as IPv4 and IPv6, to utilize the same network interface and media.
+ Media Access Control (MAC): This lower sublayer defines the media access processes performed by the hardware. It provides data link layer addressing and delimiting of data according to the physical signaling requirements of the medium and the type of data link layer protocol in use.
56. The global configuration command ip default-gateway 172.16.100.1 is applied to a switch. What is the effect of this command?
- The switch can communicate with other hosts on the 172.16.100.0 network.
- The switch can be remotely managed from a host on another network.
- The switch is limited to sending and receiving frames to and from the gateway 172.16.100.1.
- The switch will have a management interface with the address 172.16.100.1.
Explanation: A default gateway address is typically configured on all devices to allow them to communicate beyond just their local network.In a switch this is achieved using the command ip default-gateway .
57. What happens when the transport input ssh command is entered on the switch vty lines?
- The SSH client on the switch is enabled.
- The switch requires a username/password combination for remote access.
- Communication between the switch and remote users is encrypted.
- The switch requires remote connections via a proprietary client software.
Explanation: The transport input ssh command when entered on the switch vty (virtual terminal lines) will encrypt all inbound controlled telnet connections.
58. Match the type of threat with the cause. (Not all options are used.)
59. A disgruntled employee is using some free wireless networking tools to determine information about the enterprise wireless networks. This person is planning on using this information to hack the wireless network. What type of attack is this?
- DoS
- access
- reconnaissance
- Trojan horse
60. What service is provided by HTTP?
- Uses encryption to secure the exchange of text, graphic images, sound, and video on the web.
- Allows for data transfers between a client and a file server.
- An application that allows real-time chatting among remote users.
- A basic set of rules for exchanging text, graphic images, sound, video, and other multimedia files on the web.
61. A client packet is received by a server. The packet has a destination port number of 67. What service is the client requesting?
- FTP
- DHCP
- Telnet
- SSH
62. What are two problems that can be caused by a large number of ARP request and reply messages? (Choose two.)
- Switches become overloaded because they concentrate all the traffic from the attached subnets.
- The ARP request is sent as a broadcast, and will flood the entire subnet.
- The network may become overloaded because ARP reply messages have a very large payload due to the 48-bit MAC address and 32-bit IP address that they contain.
- A large number of ARP request and reply messages may slow down the switching process, leading the switch to make many changes in its MAC table.
- All ARP request messages must be processed by all nodes on the local network.
Explanation: ARP requests are sent as broadcasts:
(1) All nodes will receive them, and they will be processed by software, interrupting the CPU.
(2) The switch forwards (floods) Layer 2 broadcasts to all ports.
A switch does not change its MAC table based on ARP request or reply messages. The switch populates the MAC table using the source MAC address of all frames. The ARP payload is very small and does not overload the switch.
63. A group of Windows PCs in a new subnet has been added to an Ethernet network. When testing the connectivity, a technician finds that these PCs can access local network resources but not the Internet resources. To troubleshoot the problem, the technician wants to initially confirm the IP address and DNS configurations on the PCs, and also verify connectivity to the local router. Which three Windows CLI commands and utilities will provide the necessary information? (Choose three.)
- netsh interface ipv6 show neighbor
- arp -a
- tracert
- ping
- ipconfig
- nslookup
- telnet
64. During the process of forwarding traffic, what will the router do immediately after matching the destination IP address to a network on a directly connected routing table entry?
- analyze the destination IP address
- switch the packet to the directly connected interface
- look up the next-hop address for the packet
- discard the traffic after consulting the route table
65. What characteristic describes antispyware?
- applications that protect end devices from becoming infected with malicious software
- a network device that filters access and traffic coming into a network
- software on a router that filters traffic based on IP addresses or applications
- a tunneling protocol that provides remote users with secure access into the network of an organization
66. A network administrator needs to keep the user ID, password, and session contents private when establishing remote CLI connectivity with a switch to manage it. Which access method should be chosen?
- Telnet
- AUX
- SSH
- Console
67. What are the two most effective ways to defend against malware? (Choose two.)
- Implement a VPN.
- Implement network firewalls.
- Implement RAID.
- Implement strong passwords.
- Update the operating system and other application software.
- Install and update antivirus software.
Explanation: A cybersecurity specialist must be aware of the technologies and measures that are used as countermeasures to protect the organization from threats and vulnerabilities.
68. Which type of security threat would be responsible if a spreadsheet add-on disables the local software firewall?
- brute-force attack
- Trojan horse
- DoS
- buffer overflow
Explanation: A Trojan horse is software that does something harmful, but is hidden in legitimate software code. A denial of service (DoS) attack results in interruption of network services to users, network devices, or applications. A brute-force attack commonly involves trying to access a network device. A buffer overflow occurs when a program attempts to store more data in a memory location than it can hold.
69. Which frame field is created by a source node and used by a destination node to ensure that a transmitted data signal has not been altered by interference, distortion, or signal loss?
- User Datagram Protocol field
- transport layer error check field
- flow control field
- frame check sequence field
- error correction process field
70. A network administrator is adding a new LAN to a branch office. The new LAN must support 4 connected devices. What is the smallest network mask that the network administrator can use for the new network?
- 255.255.255.248
- 255.255.255.0
- 255.255.255.128
- 255.255.255.192
71. What service is provided by POP3?
- Retrieves email from the server by downloading the email to the local mail application of the client.
- An application that allows real-time chatting among remote users.
- Allows remote access to network devices and servers.
- Uses encryption to provide secure remote access to network devices and servers.
72. What two security solutions are most likely to be used only in a corporate environment? (Choose two.)
- antispyware
- virtual private networks
- intrusion prevention systems
- strong passwords
- antivirus software
73. What characteristic describes antivirus software?
- applications that protect end devices from becoming infected with malicious software
- a network device that filters access and traffic coming into a network
- a tunneling protocol that provides remote users with secure access into the network of an organization
- software on a router that filters traffic based on IP addresses or applications
74. What mechanism is used by a router to prevent a received IPv4 packet from traveling endlessly on a network?
- It checks the value of the TTL field and if it is 0, it discards the packet and sends a Destination Unreachable message to the source host.
- It checks the value of the TTL field and if it is 100, it discards the packet and sends a Destination Unreachable message to the source host.
- It decrements the value of the TTL field by 1 and if the result is 0, it discards the packet and sends a Time Exceeded message to the source host.
- It increments the value of the TTL field by 1 and if the result is 100, it discards the packet and sends a Parameter Problem message to the source host.
75. A client packet is received by a server. The packet has a destination port number of 69. What service is the client requesting?
- DNS
- DHCP
- SMTP
- TFTP
76. An administrator defined a local user account with a secret password on router R1 for use with SSH. Which three additional steps are required to configure R1 to accept only encrypted SSH connections? (Choose three.)
- Configure DNS on the router.
- Generate two-way pre-shared keys.
- Configure the IP domain name on the router.
- Generate the SSH keys.
- Enable inbound vty SSH sessions.
- Enable inbound vty Telnet sessions.
77. Which two functions are performed at the MAC sublayer of the OSI Data Link Layer to facilitate Ethernet communication? (Choose two.)
- places information in the Ethernet frame that identifies which network layer protocol is being encapsulated by the frame
- adds Ethernet control information to network protocol data
- responsible for internal structure of Ethernet frame
- enables IPv4 and IPv6 to utilize the same physical medium
- implements trailer with frame check sequence for error detection
Other case
- integrates Layer 2 flows between 10 Gigabit Ethernet over fiber and 1 Gigabit Ethernet over copper
- handles communication between upper layer networking software and Ethernet NIC hardware
- implements CSMA/CD over legacy shared half-duplex media
- applies source and destination MAC addresses to Ethernet frame
- applies delimiting of Ethernet frame fields to synchronize communication between nodes
78. An IPv6 enabled device sends a data packet with the destination address of FF02::2. What is the target of this packet?
- all IPv6 enabled devices on the local link
- all IPv6 DHCP servers
- all IPv6 enabled devices across the network
- all IPv6 configured routers on the local link
79. What are the three parts of an IPv6 global unicast address? (Choose three.)
- subnet ID
- subnet mask
- broadcast address
- global routing prefix
- interface ID
80. A client is using SLAAC to obtain an IPv6 address for its interface. After an address has been generated and applied to the interface, what must the client do before it can begin to use this IPv6 address?
- It must send a DHCPv6 INFORMATION-REQUEST message to request the address of the DNS server.
- It must send a DHCPv6 REQUEST message to the DHCPv6 server to request permission to use this address.
- It must send an ICMPv6 Router Solicitation message to determine what default gateway it should use.
- It must send an ICMPv6 Neighbor Solicitation message to ensure that the address is not already in use on the network.
81. A new network administrator has been asked to enter a banner message on a Cisco device. What is the fastest way a network administrator could test whether the banner is properly configured?
- Enter CTRL-Z at the privileged mode prompt.
- Exit global configuration mode.
- Power cycle the device.
- Reboot the device.
- Exit privileged EXEC mode and press Enter .
82. What method is used to manage contention-based access on a wireless network?
- token passing
- CSMA/CA
- priority ordering
- CSMA/CD
83. What is a function of the data link layer?
- provides the formatting of data
- provides end-to-end delivery of data between hosts
- provides delivery of data between two applications
- provides for the exchange of frames over a common local media
84. What is the purpose of the TCP sliding window?
- to ensure that segments arrive in order at the destination
- to end communication when data transmission is complete
- to inform a source to retransmit data from a specific point forward
- to request that a source decrease the rate at which it transmits data
85. What characteristic describes spyware?
- a network device that filters access and traffic coming into a network
- software that is installed on a user device and collects information about the user
- an attack that slows or crashes a device or network service
- the use of stolen credentials to access private data
86. Which switching method drops frames that fail the FCS check?
- store-and-forward switching
- borderless switching
- ingress port buffering
- cut-through switching
87. Two pings were issued from a host on a local network. The first ping was issued to the IP address of the default gateway of the host and it failed. The second ping was issued to the IP address of a host outside the local network and it was successful. What is a possible cause for the failed ping?
- The default gateway is not operational.
- The default gateway device is configured with the wrong IP address.
- Security rules are applied to the default gateway device, preventing it from processing ping requests.
- The TCP/IP stack on the default gateway is not working properly.
88. What service is provided by FTP?
- A basic set of rules for exchanging text, graphic images, sound, video, and other multimedia files on the web.
- An application that allows real-time chatting among remote users.
- Allows for data transfers between a client and a file server.
- Uses encryption to secure the exchange of text, graphic images, sound, and video on the web.
89. A user is attempting to access http://www.cisco.com/ without success. Which two configuration values must be set on the host to allow this access? (Choose two.)
- DNS server
- source port number
- HTTP server
- source MAC address
- default gateway
90. Which two statements accurately describe an advantage or a disadvantage when deploying NAT for IPv4 in a network? (Choose two.)
- NAT adds authentication capability to IPv4.
- NAT introduces problems for some applications that require end-to-end connectivity.
- NAT will impact negatively on switch performance.
- NAT provides a solution to slow down the IPv4 address depletion.
- NAT improves packet handling.
- NAT causes routing tables to include more information.
91. What subnet mask is needed if an IPv4 network has 40 devices that need IP addresses and address space is not to be wasted?
- 255.255.255.0
- 255.255.255.240
- 255.255.255.128
- 255.255.255.192
- 255.255.255.224
92. Refer to the exhibit. PC1 issues an ARP request because it needs to send a packet to PC2. In this scenario, what will happen next?
- PC2 will send an ARP reply with its MAC address.
- RT1 will send an ARP reply with its Fa0/0 MAC address.
- RT1 will send an ARP reply with the PC2 MAC address.
- SW1 will send an ARP reply with the PC2 MAC address.
- SW1 will send an ARP reply with its Fa0/1 MAC address.
Explain:
When a network device wants to communicate with another device on the same network, it sends a broadcast ARP request. In this case, the request will contain the IP address of PC2. The destination device (PC2) sends an ARP reply with its MAC address.
93. What service is provided by BOOTP?
- Uses encryption to secure the exchange of text, graphic images, sound, and video on the web.
- Allows for data transfers between a client and a file server.
- Legacy application that enables a diskless workstation to discover its own IP address and find a BOOTP server on the network.
- A basic set of rules for exchanging text, graphic images, sound, video, and other multimedia files on the web.
94. What characteristic describes adware?
- a network device that filters access and traffic coming into a network
- software that is installed on a user device and collects information about the user
- the use of stolen credentials to access private data
- an attack that slows or crashes a device or network service
95. What is a benefit of using cloud computing in networking?
- Technology is integrated into every-day appliances allowing them to interconnect with other devices, making them more ‘smart’ or automated.
- Network capabilities are extended without requiring investment in new infrastructure, personnel, or software.
- End users have the freedom to use personal tools to access information and communicate across a business network.
- Home networking uses existing electrical wiring to connect devices to the network wherever there is an electrical outlet, saving the cost of installing data cables.
96. Match a statement to the related network model. (Not all options are used.)
Place the options in the following order:peer-to-peer network
[+] no dedicated server is required
[+] client and server roles are set on a per request basis
peer-to-peer aplication
[#] requires a specific user interface
[#] a background service is required
Explain:
Peer-to-peer networks do not require the use of a dedicated server, and devices can assume both client and server roles simultaneously on a per request basis. Because they do not require formalized accounts or permissions, they are best used in limited situations. Peer-to-peer applications require a user interface and background service to be running, and can be used in more diverse situations.
97. Which information does the show startup-config command display?
- the IOS image copied into RAM
- the bootstrap program in the ROM
- the contents of the current running configuration file in the RAM
- the contents of the saved configuration file in the NVRAM
Explain:
The show startup-config command displays the saved configuration located in NVRAM. The show running-config command displays the contents of the currently running configuration file located in RAM.
98. Refer to the exhibit. What three facts can be determined from the viewable output of the show ip interface brief command? (Choose three.)
- Two physical interfaces have been configured.
- The switch can be remotely managed.
- One device is attached to a physical interface.
- Passwords have been configured on the switch.
- Two devices are attached to the switch.
- The default SVI has been configured.
Explain:
Vlan1 is the default SVI. Because an SVI has been configured, the switch can be configured and managed remotely. FastEthernet0/0 is showing up and up, so a device is connected.
99. Match each type of frame field to its function. (Not all options are used.)
100. What is the subnet ID associated with the IPv6 address 2001:DA48:FC5:A4:3D1B::1/64?
- 2001:DA48::/64
- 2001:DA48:FC5::A4:/64
- 2001:DA48:FC5:A4::/64
- 2001::/64
101. Match the firewall function to the type of threat protection it provides to the network. (Not all options are used.)
- packet filtering – prevents access based on IP or MAC address
- URL filtering – prevents access to websites
- network address translator – (none)
- stateful packet inspection – prevents unsolicited incoming sessions
- application filtering – prevents access by port number
Explain:Firewall products come packaged in various forms. These products use different techniques for determining what will be permitted or denied access to a network. They include the following:
+ Packet filtering – Prevents or allows access based on IP or MAC addresses
+ Application filtering – Prevents or allows access by specific application types based on port numbers
+ URL filtering – Prevents or allows access to websites based on specific URLs or keywords
+ Stateful packet inspection (SPI) – Incoming packets must be legitimate responses to requests from internal hosts. Unsolicited packets are blocked unless permitted specifically. SPI can also include the capability to recognize and filter out specific types of attacks, such as denial of service (DoS)
102. Users are reporting longer delays in authentication and in accessing network resources during certain time periods of the week. What kind of information should network engineers check to find out if this situation is part of a normal network behavior?
- syslog records and messages
- the network performance baseline
- debug output and packet captures
- network configuration files
103. What characteristic describes a VPN?
- software on a router that filters traffic based on IP addresses or applications
- software that identifies fast-spreading threats
- a tunneling protocol that provides remote users with secure access into the network of an organization
- a network device that filters access and traffic coming into a network
104. Which two statements are correct in a comparison of IPv4 and IPv6 packet headers? (Choose two.)
- The Source Address field name from IPv4 is kept in IPv6.
- The Version field from IPv4 is not kept in IPv6.
- The Destination Address field is new in IPv6.
- The Header Checksum field name from IPv4 is kept in IPv6.
- The Time-to-Live field from IPv4 has been replaced by the Hop Limit field in IPv6.
105. A network administrator wants to have the same network mask for all networks at a particular small site. The site has the following networks and number of devices:
IP phones – 22 addresses
PCs – 20 addresses needed
Printers – 2 addresses needed
Scanners – 2 addresses needed
The network administrator has deemed that 192.168.10.0/24 is to be the network used at this site. Which single subnet mask would make the most efficient use of the available addresses to use for the four subnetworks?
- 255.255.255.192
- 255.255.255.252
- 255.255.255.240
- 255.255.255.248
- 255.255.255.0
- 255.255.255.224
106. What is an advantage to using a protocol that is defined by an open standard?
- A company can monopolize the market.
- The protocol can only be run on equipment from a specific vendor.
- An open standard protocol is not controlled or regulated by standards organizations.
- It encourages competition and promotes choices.
Explain:
A monopoly by one company is not a good idea from a user point of view. If a protocol can only be run on one brand, it makes it difficult to have mixed equipment in a network. A proprietary protocol is not free to use. An open standard protocol will in general be implemented by a wide range of vendors.
107. A network administrator is adding a new LAN to a branch office. The new LAN must support 200 connected devices. What is the smallest network mask that the network administrator can use for the new network?
- 255.255.255.240
- 255.255.255.0
- 255.255.255.248
- 255.255.255.224
108. What are three commonly followed standards for constructing and installing cabling? (Choose three.)
- cost per meter (foot)
- cable lengths
- connector color
- pinouts
- connector types
- tensile strength of plastic insulator
109. Refer to the exhibit. What is wrong with the displayed termination?
- The woven copper braid should not have been removed.
- The wrong type of connector is being used.
- The untwisted length of each wire is too long.
- The wires are too thick for the connector that is used.
Explanation: When a cable to an RJ-45 connector is terminated, it is important to ensure that the untwisted wires are not too long and that the flexible plastic sheath surrounding the wires is crimped down and not the bare wires. None of the colored wires should be visible from the bottom of the jack.
110. Match the characteristic to the category. (Not all options are used.)
111. A client packet is received by a server. The packet has a destination port number of 143. What service is the client requesting?
- IMAP
- FTP
- SSH
- Telnet
112. What are two characteristics shared by TCP and UDP? (Choose two.)
- default window size
- connectionless communication
- port numbering
- 3-way handshake
- ability to to carry digitized voice
- use of checksum
Explain:
Both TCP and UDP use source and destination port numbers to distinguish different data streams and to forward the right data segments to the right applications. Error checking the header and data is done by both protocols by using a checksum calculation to determine the integrity of the data that is received. TCP is connection-oriented and uses a 3-way handshake to establish an initial connection. TCP also uses window to regulate the amount of traffic sent before receiving an acknowledgment. UDP is connectionless and is the best protocol for carry digitized VoIP signals.
113. Which value, that is contained in an IPv4 header field, is decremented by each router that receives a packet?
- Header Length
- Differentiated Services
- Time-to-Live
- Fragment Offset
Explanation: When a router receives a packet, the router will decrement the Time-to-Live (TTL) field by one. When the field reaches zero, the receiving router will discard the packet and will send an ICMP Time Exceeded message to the sender.
114. A client packet is received by a server. The packet has a destination port number of 21. What service is the client requesting?
- FTP
- LDAP
- SLP
- SNMP
115. What attribute of a NIC would place it at the data link layer of the OSI model?
- attached Ethernet cable
- IP address
- MAC address
- RJ-45 port
- TCP/IP protocol stack
116. A network administrator is adding a new LAN to a branch office. The new LAN must support 10 connected devices. What is the smallest network mask that the network administrator can use for the new network?
- 255.255.255.192
- 255.255.255.248
- 255.255.255.224
- 255.255.255.240
117. A user is executing a tracert to a remote device. At what point would a router, which is in the path to the destination device, stop forwarding the packet?
- when the router receives an ICMP Time Exceeded message
- when the RTT value reaches zero
- when the host responds with an ICMP Echo Reply message
- when the value in the TTL field reaches zero
- when the values of both the Echo Request and Echo Reply messages reach zero
Explain:
When a router receives a traceroute packet, the value in the TTL field is decremented by 1. When the value in the field reaches zero, the receiving router will not forward the packet, and will send an ICMP Time Exceeded message back to the source.
118. Refer to the exhibit. The network administrator has assigned the LAN of LBMISS an address range of 192.168.10.0. This address range has been subnetted using a /29 prefix. In order to accommodate a new building, the technician has decided to use the fifth subnet for configuring the new network (subnet zero is the first subnet). By company policies, the router interface is always assigned the first usable host address and the workgroup server is given the last usable host address. Which configuration should be entered into the properties of the workgroup server to allow connectivity to the Internet?
- IP address: 192.168.10.65 subnet mask: 255.255.255.240, default gateway: 192.168.10.76
- IP address: 192.168.10.38 subnet mask: 255.255.255.240, default gateway: 192.168.10.33
- IP address: 192.168.10.38 subnet mask: 255.255.255.248, default gateway: 192.168.10.33
- IP address: 192.168.10.41 subnet mask: 255.255.255.248, default gateway: 192.168.10.46
- IP address: 192.168.10.254 subnet mask: 255.255.255.0, default gateway: 192.168.10.1
Explain:
Using a /29 prefix to subnet 192.168.10.0 results in subnets that increment by 8:
192.168.10.0 (1)
192.168.10.8 (2)
192.168.10.16 (3)
192.168.10.24 (4)
192.168.10.32 (5)
119. Refer to the exhibit. The switches are in their default configuration. Host A needs to communicate with host D, but host A does not have the MAC address for its default gateway. Which network hosts will receive the ARP request sent by host A?
- only host D
- only router R1
- only hosts A, B, and C
- only hosts A, B, C, and D
- only hosts B and C
- only hosts B, C, and router R1
Explain:
Since host A does not have the MAC address of the default gateway in its ARP table, host A sends an ARP broadcast. The ARP broadcast would be sent to every device on the local network. Hosts B, C, and router R1 would receive the broadcast. Router R1 would not forward the message.
120. Which two traffic types use the Real-Time Transport Protocol (RTP)? (Choose two.)
- video
- web
- file transfer
- voice
- peer to peer
121. Which wireless technology has low-power and data rate requirements making it popular in home automation applications?
- ZigBee
- LoRaWAN
- 5G
- Wi-Fi
122. Which layer of the TCP/IP model provides a route to forward messages through an internetwork?
- application
- network access
- internet
- transport
Explain:
The OSI model network layer corresponds directly to the internet layer of the TCP/IP model and is used to describe protocols that address and route messages through an internetwork.
123. Which type of server relies on record types such as A, NS, AAAA, and MX in order to provide services?
- DNS
- file
- web
Explain:
A DNS server stores records that are used to resolve IP addresses to host names. Some DNS record types include the following:
A – an end device IPv4 address
NS – an authoritative name server
AAAA – an end device IPv6 address
MX – a mail exchange record
124. What are proprietary protocols?
- protocols developed by private organizations to operate on any vendor hardware
- protocols that can be freely used by any organization or vendor
- protocols developed by organizations who have control over their definition and operation
- a collection of protocols known as the TCP/IP protocol suite
Explain:
Proprietary protocols have their definition and operation controlled by one company or vendor. Some of them can be used by different organizations with permission from the owner. The TCP/IP protocol suite is an open standard, not a proprietary protocol.
125. What service is provided by DNS?
- Resolves domain names, such as cisco.com, into IP addresses.
- A basic set of rules for exchanging text, graphic images, sound, video, and other multimedia files on the web.
- Allows for data transfers between a client and a file server.
- Uses encryption to secure the exchange of text, graphic images, sound, and video on the web.
126. A client packet is received by a server. The packet has a destination port number of 110. What service is the client requesting?
- DNS
- DHCP
- SMTP
- POP3
127. What command can be used on a Windows PC to see the IP configuration of that computer?
- show ip interface brief
- ping
- show interfaces
- ipconfig
128. A wired laser printer is attached to a home computer. That printer has been shared so that other computers on the home network can also use the printer. What networking model is in use?
- client-based
- master-slave
- point-to-point
- peer-to-peer (P2P)
Explanation: Peer-to-peer (P2P) networks have two or more network devices that can share resources such as printers or files without having a dedicated server.
129. What characteristic describes a virus?
- a network device that filters access and traffic coming into a network
- the use of stolen credentials to access private data
- an attack that slows or crashes a device or network service
- malicious software or code running on an end device
130. Three bank employees are using the corporate network. The first employee uses a web browser to view a company web page in order to read some announcements. The second employee accesses the corporate database to perform some financial transactions. The third employee participates in an important live audio conference with other corporate managers in branch offices. If QoS is implemented on this network, what will be the priorities from highest to lowest of the different data types?
- financial transactions, web page, audio conference
- audio conference, financial transactions, web page
- financial transactions, audio conference, web page
- audio conference, web page, financial transactions
Explanation: QoS mechanisms enable the establishment of queue management strategies that enforce priorities for different categories of application data. Thus, this queuing enables voice data to have priority over transaction data, which has priority over web data.
131. Match the description to the IPv6 addressing component. (Not all options are used.)
132. Refer to the exhibit. If Host1 were to transfer a file to the server, what layers of the TCP/IP model would be used?
- only application and Internet layers
- only Internet and network access layers
- only application, Internet, and network access layers
- application, transport, Internet, and network access layers
- only application, transport, network, data link, and physical layers
- application, session, transport, network, data link, and physical layers
Explanation: The TCP/IP model contains the application, transport, internet, and network access layers. A file transfer uses the FTP application layer protocol. The data would move from the application layer through all of the layers of the model and across the network to the file server.
133. Match the characteristic to the forwarding method. (Not all options are used.)
Explanation: A store-and-forward switch always stores the entire frame before forwarding, and checks its CRC and frame length. A cut-through switch can forward frames before receiving the destination address field, thus presenting less latency than a store-and-forward switch. Because the frame can begin to be forwarded before it is completely received, the switch may transmit a corrupt or runt frame. All forwarding methods require a Layer 2 switch to forward broadcast frames.
134. Refer to the exhibit. The IP address of which device interface should be used as the default gateway setting of host H1?
- R1: S0/0/0
- R2: S0/0/1
- R1: G0/0
- R2: S0/0/0
135. What service is provided by Internet Messenger?
- An application that allows real-time chatting among remote users.
- Allows remote access to network devices and servers.
- Resolves domain names, such as cisco.com, into IP addresses.
- Uses encryption to provide secure remote access to network devices and servers.
136. Refer to the exhibit. Match the network with the correct IP address and prefix that will satisfy the usable host addressing requirements for each network.
Explanation: Network A needs to use 192.168.0.128 /25, which yields 128 host addresses.
Network B needs to use 192.168.0.0 /26, which yields 64 host addresses.
Network C needs to use 192.168.0.96 /27, which yields 32 host addresses.
Network D needs to use 192.168.0.80/30, which yields 4 host addresses.
137. Refer to the exhibit. Which protocol was responsible for building the table that is shown?
- DHCP
- ARP
- DNS
- ICMP
138. A network administrator notices that some newly installed Ethernet cabling is carrying corrupt and distorted data signals. The new cabling was installed in the ceiling close to fluorescent lights and electrical equipment. Which two factors may interfere with the copper cabling and result in signal distortion and data corruption? (Choose two.)
- crosstalk
- extended length of cabling
- RFI
- EMI
- signal attenuation
139. A host is trying to send a packet to a device on a remote LAN segment, but there are currently no mappings in its ARP cache. How will the device obtain a destination MAC address?
A host is trying to send a packet to a device on a remote LAN segment, but there are currently no mappings in the ARP cache. How will the device obtain a destination MAC address?
- It will send the frame and use its own MAC address as the destination.
- It will send an ARP request for the MAC address of the destination device.
- It will send the frame with a broadcast MAC address.
- It will send a request to the DNS server for the destination MAC address.
- It will send an ARP request for the MAC address of the default gateway.
140. Which two functions are performed at the MAC sublayer of the OSI Data Link Layer to facilitate Ethernet communication?
- integrates Layer 2 flows between 10 Gigabit Ethernet over fiber and 1 Gigabit Ethernet over copper
- enables IPv4 and IPv6 to utilize the same physical medium
- handles communication between upper layer networking software and Ethernet NIC hardware
- adds Ethernet control information to network protocol data
- implements CSMA/CD over legacy shared half-duplex media
141. A client packet is received by a server. The packet has a destination port number of 53. What service is the client requesting?
- DNS
- NetBIOS (NetBT)
- POP3
- IMAP
142. A network administrator is adding a new LAN to a branch office. The new LAN must support 25 connected devices. What is the smallest network mask that the network administrator can use for the new network?
- 255.255.255.128
- 255.255.255.192
- 255.255.255.224
- 255.255.255.240
143. What characteristic describes a Trojan horse?
- malicious software or code running on an end device
- an attack that slows or crashes a device or network service
- the use of stolen credentials to access private data
- a network device that filters access and traffic coming into a network
144. What service is provided by HTTPS?
- Uses encryption to provide secure remote access to network devices and servers.
- Resolves domain names, such as cisco.com, into IP addresses.
- Uses encryption to secure the exchange of text, graphic images, sound, and video on the web.
- Allows remote access to network devices and servers.
145. A technician with a PC is using multiple applications while connected to the Internet. How is the PC able to keep track of the data flow between multiple application sessions and have each application receive the correct packet flows?
- The data flow is being tracked based on the destination MAC address of the technician PC.
- The data flow is being tracked based on the source port number that is used by each application.*
- The data flow is being tracked based on the source IP address that is used by the PC of the technician.
- The data flow is being tracked based on the destination IP address that is used by the PC of the technician.
Explanation:
The source port number of an application is randomly generated and used to individually keep track of each session connecting out to the Internet. Each application will use a unique source port number to provide simultaneous communication from multiple applications through the Internet.
146. A network administrator is adding a new LAN to a branch office. The new LAN must support 61 connected devices. What is the smallest network mask that the network administrator can use for the new network?
- 255.255.255.240
- 255.255.255.224
- 255.255.255.192
- 255.255.255.128
147. Refer to the exhibit. Match the network with the correct IP address and prefix that will satisfy the usable host addressing requirements for each network. (Not all options are used.)
Question
Answer
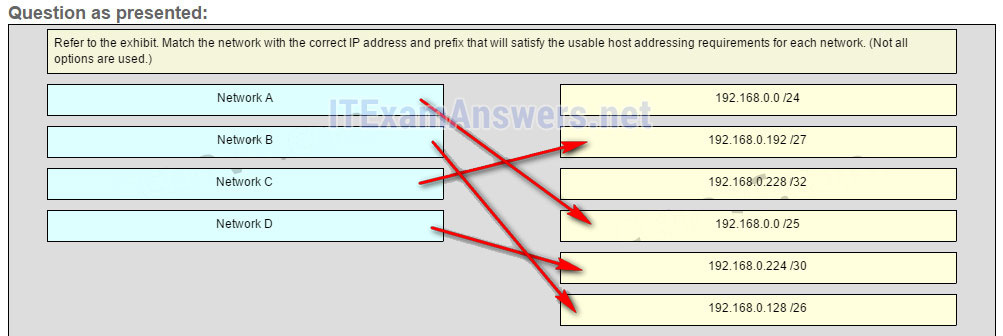
Explanation:
Network A needs to use 192.168.0.0 /25 which yields 128 host addresses.
Network B needs to use 192.168.0.128 /26 which yields 64 host addresses.
Network C needs to use 192.168.0.192 /27 which yields 32 host addresses.
Network D needs to use 192.168.0.224 /30 which yields 4 host addresses.
148. What characteristic describes a DoS attack?
- the use of stolen credentials to access private data
- a network device that filters access and traffic coming into a network
- software that is installed on a user device and collects information about the user
- an attack that slows or crashes a device or network service
149. Match the application protocols to the correct transport protocols
150. What service is provided by SMTP?
- Allows clients to send email to a mail server and the servers to send email to other servers.
- Allows remote access to network devices and servers.
- Uses encryption to provide secure remote access to network devices and servers.
- An application that allows real-time chatting among remote users.
151. Match a statement to the related network model. (Not all options are used.)
Place the options in the following order:peer-to-peer network
[+] no dedicated server is required
[+] client and server roles are set on a per request basis
peer-to-peer aplication
[#] requires a specific user interface
[#] a background service is required
Explain:
Peer-to-peer networks do not require the use of a dedicated server, and devices can assume both client and server roles simultaneously on a per request basis. Because they do not require formalized accounts or permissions, they are best used in limited situations. Peer-to-peer applications require a user interface and background service to be running, and can be used in more diverse situations.
152. Match the application protocols to the correct transport protocols.
153. Refer to the exhibit. A network engineer has been given the network address of 192.168.99.0 and a subnet mask of 255.255.255.192 to subnet across the four networks shown. How many total host addresses are unused across all four subnets?
- 88
- 200
- 72
- 224
- 158
154. Which connector is used with twisted-pair cabling in an Ethernet LAN?
True Answer:
155. A client packet is received by a server. The packet has a destination port number of 22. What service is the client requesting?
- SSH
- SMB/CIFS
- HTTPS
- SLP
156. What characteristic describes an IPS?
- a tunneling protocol that provides remote users with secure access into the network of an organization
- a network device that filters access and traffic coming into a network
- software that identifies fast-spreading threats
- software on a router that filters traffic based on IP addresses or applications
157. What service is provided by DHCP?
- An application that allows real-time chatting among remote users.
- Allows remote access to network devices and servers.
- Dynamically assigns IP addresses to end and intermediary devices.
- Uses encryption to provide secure remote access to network devices and servers.
158. Match the header field with the appropriate layer of the OSI model. (Not all options are used.)
159. Refer to the exhibit. The switches have a default configuration. Host A needs to communicate with host D, but host A does not have the MAC address for the default gateway. Which network devices will receive the ARP request sent by host A?
- only host D
- only hosts A, B, C, and D
- only hosts B and C
- only hosts B, C, and router R1
- only hosts A, B, and C
- only router R1
160. Which wireless technology has low-power and low-data rate requirements making it popular in IoT environments?
- Bluetooth
- Zigbee
- WiMAX
- Wi-Fi
Explanation: Zigbee is a specification used for low-data rate, low-power communications. It is intended for applications that require short-range, low data-rates and long battery life. Zigbee is typically used for industrial and Internet of Things (IoT) environments such as wireless light switches and medical device data collection.
161. The global configuration command ip default-gateway 172.16.100.1 is applied to a switch. What is the effect of this command?
- The switch will have a management interface with the address 172.16.100.1.
- The switch can be remotely managed from a host on another network.
- The switch can communicate with other hosts on the 172.16.100.0 network.
- The switch is limited to sending and receiving frames to and from the gateway 172.16.100.1.
Explanation: A default gateway address is typically configured on all devices to allow them to communicate beyond just their local network.In a switch this is achieved using the command ip default-gateway <ip address>.
Network Essentials Final Exam Answers 100%
-
What is a disadvantage of deploying a peer-to-peer network model?
- difficulty of setup
- lack of centralized administration
- high degree of complexity
- high cost
Explanation:The simplest peer-to-peer network consists of two computers that are directly connected to each other through the use of a wired or wireless connection. The primary disadvantages of a peer-to-peer network are its lack of central administration, minimal security, and its lack of scalability.
-
What is a purpose of an IP address?
- It identifies the physical location of a data center.
- It identifies a location in memory from which a program runs.
- It identifies a return address for replying to email messages.
- It identifies the source and destination of data packets.
Explanation:Packets that are routed across the Internet contain source and destination IP addresses. These addresses are used to determine how the packets should be routed from source to destination by intermediate devices.
-
A consumer places a smartphone close to a pay terminal at a store and the shopping charge is successfully paid. Which type of wireless technology was used?
- Bluetooth
- NFC
- Wi-Fi
- 3G
Explanation:NFC is a wireless technology that allows data to be exchanged between devices that are in very close proximity to each other.
-
Which type of network cable is commonly used to connect office computers to the local network?
- coaxial cable
- twisted-pair cable
- glass fiber-optic cable
- plastic fiber-optic cable
Explanation:Twisted-pair is a type of copper cable used to interconnect devices on a local network.
-
What are two advantages of using fiber-optic cabling to interconnect devices? (Choose two.)
- Fiber-optic cable is immune from EMI and RFI.
- Fiber-optic cables can extend several miles.
- Fiber-optic cables use extra shielding to protect copper wires.
- Fiber-optic cables are easy to install..
- Fiber-optic cables are commonly found in both homes and small businesses.
Explanation:Fiber-optic cables provide immunity to both EMI and RFI and a single cable can extend for several miles before regeneration is needed.
-
The functions of which two layers of the OSI model are matched to the network access layer of the TCP/IP model? (Choose two.)
- application
- physical
- transport
- network
- data link
Explanation:The application layer of the TCP/IP model is composed of the application, presentation, and session layers of the OSI model and is used by network applications to complete specific tasks. The network access layer of the TCP/IP model is composed of the physical and data link layers of the OSI model and describes how a device accesses and sends data over the network media.
-
What is the minimum size of a valid Ethernet frame?
- 48 bytes
- 64 bytes
- 96 bytes
- 128 bytes
Explanation:Ethernet standards define a frame with a minimum of 64 bytes and a maximum of 1518 bytes including fields of destination MAC address, source MAC, Length/Type, data payload, and FCS.
-
A network design engineer has been asked to design the IP addressing scheme for a customer network. The network will use IP addresses from the 192.168.30.0/24 network. The engineer allocates 254 IP addresses for the hosts on the network but excludes 192.168.30.0/24 and 192.168.30.255/24 IP addresses. Why must the engineer exclude these two IP addresses?
- 192.168.30.0/24 and 192.168.30.255/24 IP addresses are reserved for the email and DNS servers.
- 192.168.30.0/24 and 192.168.30.255/24 IP addresses are reserved for outside Internet connectivity.
- 192.168.30.0/24 is the network IP address and 192.168.30.255/24 is the IP broadcast address.
- 192.168.30.0/24 is the IP address reserved for the default gateway, and 192.168.30.255/24 is the IP address reserved for the DHCP server.
Explanation:The IPv4 addressing system is a hierarchical addressing system. An IPv4 address is made up of two parts, the network address and the host address. When the host portion is all “0s” in binary, it is designated as a network address. When the host portion is all “1s” in binary, it is designated as a broadcast address. These two addresses cannot be assigned to individual hosts.
-
Which protocol is used to automatically assign IP addresses to hosts?
- DNS
- NAT
- DHCP
- HTTP
Explanation:DHCP, or Dynamic Host Configuration Protocol, is used to automatically assign IP addresses to hosts that are configured as DHCP clients.
-
What are three advantages of using private IP addresses and NAT? (Choose three.)
- conserves registered public IP addresses
- reduces CPU usage on customer routers
- creates multiple public IP addresses
- hides private LAN addressing from outside devices that are connected to the Internet
- permits LAN expansion without additional public IP addresses
- improves the performance of the router that is connected to the Internet
Explanation:Private IP addresses are designed to be exclusively used for internal networks and they cannot be used on the Internet. Thus they are not visible directly from the Internet and they can be used freely by network administrators for internal networks. In order for the internal hosts to access the Internet, NAT is used to translate between private and public IP addresses. NAT takes an internal private IP address and translates it to a global public IP address before the packet is forwarded.
-
What was the reason for the creation and implementation of IPv6?
- to make reading a 32-bit address easier
- to relieve IPv4 address depletion
- to provide more address space in the Internet Names Registry
- to allow NAT support for private addressing
Explanation:IPv4 addressing space is exhausted by the rapid growth of the Internet and the devices connected to the Internet. IPv6 expands the IP addressing space by increasing the address length from the 32 bits to 128 bits, which should provide sufficient addresses for future Internet growth needs for many years to come.
-
Which three pieces of information are identified by a URL? (Choose three.)
- the MAC address of the web server
- the protocol that is being used
- the domain name that is being accessed
- the IP address of the gateway
- the version of the browser
- the location of the resource
Explanation:URLs are used to access specific content on a web server through a web browser. The URL identifies the protocol that is being used such as HTTP or FTP, the domain of the server, and the location of the resource on the server.
-
Which protocol is used by web servers to serve up a web page?
- FTP
- HTTP
- IMAP
- POP
Explanation:Hypertext Transfer Protocol (HTTP) is a protocol that is used by web servers to serve up a web page.
-
Why do streaming audio and video applications use UDP instead of TCP?
- Streaming audio and video applications require receipt of all packets regardless of delay.
- The three-way handshake used in UDP speeds up the audio and video streams.
- Streaming audio and video applications cannot tolerate the delay caused by retransmission.
- UDP provides guaranteed segment delivery to provide reliable audio and video streams.
Explanation:UDP is a ‘best effort’ delivery system that does not require acknowledgment of receipt and is the preferred transport service for streaming audio and video. UDP provides low overhead and does not implement as much delay as TCP. Streaming audio and video cannot tolerate network traffic congestion and long delays.
-
At which layer of the TCP/IP model does TCP operate?
- transport
- application
- internetwork
- network access
Explanation:TCP is the Transmission Control Protocol and it operates at the transport layer of the TCP/IP model. TCP ensures that IP packets are delivered reliably.
-
Which protocol is used to transfer web pages from a server to a client device?
- HTML
- SMTP
- HTTP
- SSH
- POP
Explanation:The Hypertext Transfer Protocol (HTTP) provides services between a web browser requesting web pages and a web server responding to the requests. HTML (Hypertext Markup Language) is a markup language to instruct a web browser how to interpret and display a web page.
-
Which type of device filtering can be enabled on some wireless access points or wireless routers?
- authentication
- IP address
- user ID
- MAC address
Explanation:On wireless access points, MAC addresses can be manually entered to filter which devices are allowed on the wireless network.
-
Which technology is used to uniquely identify a WLAN network?
- MAC address table
- SSID
- WEP
- WPA
Explanation:When a wireless AP or router is being set up, an SSID is configured to uniquely identify the WLAN that is managed by the device.
-
What type of Internet connection would be best for a residence in a remote area without mobile phone coverage or wired connectivity?
- dial-up
- cellular
- satellite
- DSL
Explanation:Satellite Internet service provides the best option for a home user that would otherwise have no Internet connectivity at all. Cellular Internet is only available in areas with mobile phone coverage.
-
Which advanced wireless security measure allows a network administrator to keep sensitive data secure as it travels over the air in a wireless network?
- encryption
- authentication
- traffic filtering
- MAC address filtering
Explanation:Encryption is used to secure plaintext data that would be viewable traveling over a wireless network.
-
Which three steps must be completed to manually connect an Android or IOS device to a secured wireless network? (Choose three.)
- Input the authentication password.
- Enter the network SSID.
- Choose the correct security type.
- Set the IP address.
- Activate the Bluetooth antenna.
- Change the MAC address.
Explanation:In order to connect an Android or IOS device to a Wi-Fi network manually, perform these steps:
- Enter the network SSID of the wireless network.
- Choose the security type used by the wireless network.
- Input the password to authenticate successfully.
-
Which three attacks exploit human behavior? (Choose three.)
- pretexting
- brute force
- phishing
- zombies
- vishing
- malware
Explanation:Attacks aimed at exploiting human behavior such as pretexting, phishing, and vishing are commonly used by hackers to obtain information directly from authorized users.
-
Which address prefix range is reserved for IPv4 multicast?
- 240.0.0.0 – 254.255.255.255
- 224.0.0.0 – 239.255.255.255
- 169.254.0.0 – 169.254.255.255
- 127.0.0.0 – 127.255.255.255
Explanation:Multicast IPv4 addresses use the reserved class D address range of 224.0.0.0 to 239.255.255.255.
-
An intruder tries a large number of possibilities in rapid succession to guess a password. As a result, other users on the network are locked out. What type of attack has occurred?
- DDoS
- brute force
- ping of death
- SYN flooding
Explanation:In a brute force attack, an unauthorized person will try to gain access to a system by sending as many passwords as possible as rapidly as possible.
-
What type of DoS attack originates from a malicious host that has an invalid source IP address and that requests a client connection?
- ping of death
- SYN flooding
- phishing
- brute force
Explanation:SYN flooding is a type of denial of services attack where the attacker sends fake session requests to a target host in an attempt to prevent the host from responding to legitimate session requests.
-
Which two ports can be used for the initial configuration of a Cisco router? (Choose two.)
- AUX
- console
- flash slot
- LAN interface
- WAN interface
Explanation:The AUX and console ports on a Cisco 1941 router can be used to perform initial setup. The initial setup does not require that the router be connected to a network. A network administrator uses a computer to connect to the console ports directly. A network administrator can also access the router remotely through a dialup phone line and a modem connected to the AUX port. LAN and WAN interfaces are used to connect to networks. The flash slots expand storage capability through the use of a compact flash card.
-
When is an IP address required to be configured on a Cisco LAN switch?
- when the switch is connected to another switch
- when the switch must forward LAN traffic
- when the switch needs to be managed through an in-band connection
- when the switch is configured from a computer connected to the console port
Explanation:A LAN switch uses Layer 2 addresses to determine how to forward packets. An IP address is only necessary if the switch needs to be remotely managed through an in-band connection on the network.
-
What advantage does SSH offer over Telnet?
- encryption
- more connection lines
- connection-oriented services
- username and password authentication
Explanation:Both Telnet and SSH are used to remotely connect to a network device for management tasks. However, Telnet uses plaintext communications, whereas SSH provides security for remote connections by providing encryption of all transmitted data between devices.
-
Refer to the exhibit. A network technician is statically assigning an IP address to a PC. The default gateway is correct. What would be a valid IP address to assign to the host?
Network Essentials Final Exam Answers 001
- 128.106.10.100
- 128.107.255.1
- 128.107.255.254
- 128.108.100.10
Explanation:In data communication, the default gateway device is involved only when a host needs to communicate with other hosts on another network. The default gateway address identifies a network device used by hosts to communicate with devices on remote networks. The IP address of the host and the default gateway address must be in the same network. With the default subnet mask, valid host IP addresses range from 128.107.0.1 to 128.107.255.254.
-
Which three items should be documented after troubleshooting an internal web server crash? (Choose three.)
- when the problem occurred
- the dialogue with the user
- the configuration of all networking devices on the LAN at the time of the crash
- the configuration of all hosts on the LAN at the time of the crash
- steps that were performed to identify the cause of the problem
- steps that were performed that failed to identify the cause of the problem
Explanation:Proper documentation is a very important step in troubleshooting. The proper documentation can help troubleshoot the same or similar problems in the future. The documentation should include as much information as possible about the following:
- the problem encountered
- steps taken to determine the cause of the problem
- steps to correct the problem and ensure that it will not reoccur
-
Which step should be taken next once a problem is resolved during a troubleshooting process?
- Consult an FAQ.
- Escalate the problem.
- Update the documentation.
- Run remote access software.
Explanation:Proper documentation can help troubleshoot the same or similar problems in the future. Proper documentation should include the type of error encountered, the steps taken to determine the cause of the problem, and the steps taken to correct the problem.
-
Which three pieces of information are revealed by the ipconfig command (without the /all switch)? (Choose three.)
- IP address
- DHCP server
- subnet mask
- default gateway
- DNS server
- MAC address
Explanation:The ipconfig command is used to display the current TCP/IP network configuration values of the device. This includes the IP address; the subnet mask and the default gateway addresses. Using the ipconfig /all switch displays additional information like the physical address of the device and the DHCP server address among other things.
-
Fill in the blank.
A zombie is a computer that is infected with malicious software and instructed to join a botnet.
Explanation:Zombies are computer systems that are infected with bot software which, once activated, instructs infected machines to function as a botnet.
-
Match the router prompt to the configuration task.
Network Essentials Final Exam Answers 001
-
Match the command to the function.
Network Essentials Final Exam Answers 002